Ivan Štambuk (talk | contribs) →Collection and analysis programs or hardware: +Treasure Map |
→November: Operation Dreadnought (edited with ProveIt) |
||
| Line 406: | Line 406: | ||
==== November ==== |
==== November ==== |
||
The ''[[New York Times]]'' reported that the NSA carries out an eavesdropping effort, dubbed Operation Dreadnought, against the [[Iran|Iranian]] leader [[Ayatollah Ali Khamenei]]. During his 2009 visit to [[Iranian Kurdistan]], the agency collaborated with the GCHQ and the US' [[National Geospatial-Intelligence Agency]], collecting radio transmissions between aircraft and airports, examining Khamenei's convoy with satellite imagery, and enumerating military radar stations. According to the story, an objective of the operation is "communications fingerprinting": the ability to distinguish Khamenei's communications from those of other people in [[Iran]].<ref name="omnivore">{{cite news |
|||
| url=http://www.nytimes.com/2013/11/03/world/no-morsel-too-minuscule-for-all-consuming-nsa.html?pagewanted=7&_r=2&pagewanted=all |
|||
| title=No Morsel Too Minuscule for All-Consuming N.S.A. |
|||
| work=New York Times |
|||
| date=2013-11-02 |
|||
| accessdate=2013-11-25 |
|||
| author=Shane, Scott |
|||
| archiveurl=http://www.webcitation.org/query?url=http%3A%2F%2Fwww.nytimes.com%2F2013%2F11%2F03%2Fworld%2Fno-morsel-too-minuscule-for-all-consuming-nsa.html%3Fpagewanted%3D7%26_r%3D2%26pagewanted%3Dall&date=2013-11-25 |
|||
|archivedate=2013-11-25 |
|||
|quote=This "communications fingerprinting," as a document called it, is the key to what the N.S.A. does. It allows the agency's computers to scan the stream of international communications and pluck out messages tied to the supreme leader.}}</ref> |
|||
According to the British newspaper ''[[The Independent]]'', the British intelligence agency GCHQ maintains a listening post on the roof of the [[Embassy of the United Kingdom, Berlin|British Embassy in Berlin]] that is capable of intercepting mobile phone calls, wi-fi data and long-distance communications all over the German capital, including adjacent government buildings such as the [[Reichstag building|Reichstag]] (seat of the Germany's parliament) and the [[German Chancellery|Chancellery]] (seat of Germany's government) clustered around the [[Brandenburg Gate]].<ref>{{cite news|last=Campbell|first=Duncan|title=Revealed: Britain's 'secret listening post in the heart of Berlin'|url=http://www.independent.co.uk/news/uk/home-news/revealed-britains-secret-listening-post-in-the-heart-of-berlin-8921548.html|accessdate=November 5, 2013|newspaper=The Independent|date=November 5, 2013}}</ref> |
According to the British newspaper ''[[The Independent]]'', the British intelligence agency GCHQ maintains a listening post on the roof of the [[Embassy of the United Kingdom, Berlin|British Embassy in Berlin]] that is capable of intercepting mobile phone calls, wi-fi data and long-distance communications all over the German capital, including adjacent government buildings such as the [[Reichstag building|Reichstag]] (seat of the Germany's parliament) and the [[German Chancellery|Chancellery]] (seat of Germany's government) clustered around the [[Brandenburg Gate]].<ref>{{cite news|last=Campbell|first=Duncan|title=Revealed: Britain's 'secret listening post in the heart of Berlin'|url=http://www.independent.co.uk/news/uk/home-news/revealed-britains-secret-listening-post-in-the-heart-of-berlin-8921548.html|accessdate=November 5, 2013|newspaper=The Independent|date=November 5, 2013}}</ref> |
||
Revision as of 18:09, 25 November 2013
 National Security Agency surveillance |
|---|
 |
The 2013 global surveillance disclosures refer to numerous media reports beginning in June 2013 which revealed operational details of the US National Security Agency (NSA) and its international partners' mass surveillance of foreign nationals as well as US citizens. The series of reports emanated from a cache of top secret documents leaked by ex-NSA contractor Edward Snowden. On June 6, 2013, the first set of documents were published simultaneously by The Washington Post and The Guardian, attracting considerable public attention.[1]
The disclosures provided impetus for the creation of social movements against mass surveillance, such as Restore the Fourth. Domestic spying programs in countries such as France, the UK, and India have also been exposed. On the legal front, the Electronic Frontier Foundation joined a coalition of diverse groups filing suit against the NSA. Several human rights organizations have urged the Obama administration not to prosecute, but protect, "whistleblower Snowden": Amnesty International, Human Rights Watch, Transparency International, and the Index on Censorship,inter alia.[2][3][4][5]
On June 14, 2013, United States prosecutors charged Edward Snowden with espionage and theft of government property.[6] In late July 2013, he was granted asylum by the Russian government,[7] contributing to a deterioration of Russia–United States relations.[8][9] On August 6, 2013, President Obama made a public appearance on national television where he reassured Americans that "We don't have a domestic spying program" and "There is no spying on Americans".[10] Towards the end of October 2013, the British Prime Minister David Cameron warned The Guardian not to publish any more leaks, or it will receive a DA-Notice (publication ban).[11] Currently, a criminal investigation of these disclosures is being undertaken by Britain's Metropolitan Police Service.[12]
Historical background

.
General disclosures regarding a mass surveillance program involving U.S. citizens had been made in the U.S. media in 2006.[14] In early 2013, Edward Snowden handed over 15,000 – 20,000 top secret documents to various media outlets, triggering one of the biggest news leaks in the modern history of the United States.[15]
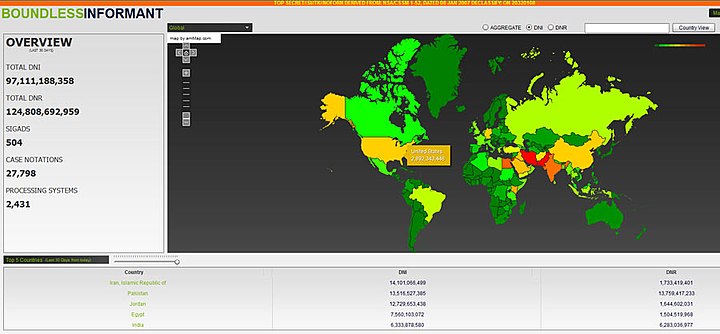
Global surveillance emerged as a phenomenon in the late 1940s (as demonstrated by the joint U.S.-British program code-named "ECHELON"),[16] In the aftermath of the 1970s Watergate affair and a subsequent congressional inquiry led by Sen. Frank Church,[17] it was revealed that the NSA, in collaboration with Britain's GCHQ, had routinely intercepted the international communications of prominent anti-Vietnam War leaders such as Jane Fonda and Dr. Benjamin Spock.[18] Decades later, a multi-year investigation by the European Parliament highlighted the NSA's role in economic espionage in a report entitled 'Development of Surveillance Technology and Risk of Abuse of Economic Information', in 1999.[19] However, for the general public, it was a series of detailed disclosures of internal NSA documents in June 2013 that first revealed the massive extent of the NSA's spying, both foreign and domestic. Most of these were leaked by an ex-contractor, Edward Snowden. Even so, a number of these older global surveillance programs such as PRISM, XKeyscore, and Tempora were referenced in the 2013 release of thousands of documents.[20] Many countries around the world, including Western Allies and member states of NATO, have been targeted by the "Five Eyes" strategic alliance of Australia, Canada, New Zealand, the UK and the USA—five English-speaking Western democracies aiming to achieve Total Information Awareness by mastering the Internet with analytical tools such as the Boundless Informant.[21] As confirmed by the NSA's director Keith B. Alexander on September 26, 2013, the NSA collects and stores all phone records of all American citizens.[22] Much of the data is kept in large storage facilities such as the Utah Data Center, a US$1.5 billion megaproject referred to by The Wall Street Journal as a "symbol of the spy agency's surveillance prowess."[23]
Origins of clandestine surveillance in the United States
Wartime censorship of communications during the World Wars was paralleled by peacetime decipherment of communications by the Black Chamber (Cipher Bureau, MI-8), operating with the approval of the U.S. State Department from 1919 to 1929.[26] In 1945 the now-defunct Project SHAMROCK was created to gather all telegraphic data entering into or exiting from the United States.[26][27] Major communication companies such as Western Union, RCA Global and ITT World Communications actively aided the U.S. government in the latter's attempt to gain access to international message traffic.[28]
In 1952, the NSA was officially established.[26] According to The New York Times, the NSA was created in "absolute secrecy" by President Truman.[29] Six weeks after President Truman took office, he ordered wiretaps on the telephones of Thomas Gardiner Corcoran, a close advisor of Franklin D. Roosevelt.[30] The recorded conversations are currently kept at the Harry S. Truman Presidential Library and Museum, along with other sensitive documents (~233,600 pages)
Under J. Edgar Hoover, the Federal Bureau of Investigation (FBI) carried out wide-ranging surveillance of communications and political expression, targeting many well-known speakers such as Albert Einstein,[13][31][32] Frank Sinatra,[33][34] First Lady Eleanor Roosevelt,[35][36] Marilyn Monroe,[37] John Lennon,[38] Martin Luther King, Jr.,[39][40] A FBI memo recognized King to be the "most dangerous and effective Negro leader in the country.",[41] Daniel Ellsberg,[42][43] Some of these activities were eventually uncovered in the aftermath of the Watergate scandal, leading to the Resignation of Richard Nixon.[44]
INVESTIGATIONS: Nobody Asked: Is It Moral?
It did not matter that much of the information had already been released —or leaked—to the public. The effect was still overwhelming: a stunning, dismaying indictment of U.S. intelligence agencies and six Presidents, from Franklin Roosevelt to Richard Nixon, for having blithely violated democratic ideals and individual rights while gathering information at home or conducting clandestine operations abroad...
— Time magazine, May 10, 1976[45]
Mass surveillance in a global context (1940–2001)

During World War II the U.K. and U.S. governments entered into a series of agreements for sharing of signals intelligence of enemy communications traffic.[50] In March 1946, a secret agreement, the "British-US Communication Intelligence Agreement", known as BRUSA, was established, based on the wartime agreements. The agreement "tied the two countries into a worldwide network of listening posts run by Government Communications Headquarters (GCHQ), the U.K's biggest spying organisation, and its U.S. equivalent, the National Security Agency."[51]
In 1988, an article titled "Somebody's listening" by Duncan Campbell in the New Statesman, described the signals intelligence gathering activities of a program code-named "ECHELON.[52] The program was engaged by English-speaking World War II Allied powers Australia, Canada, New Zealand, the United Kingdom and the United States (collectively know as AUSCANNZUKUS). Based on the UKUSA Agreement, it was created to monitor the military and diplomatic communications of the Soviet Union and its Eastern Bloc allies during the Cold War in the early 1960s.[53] Though its existence had long been known, the UKUSA agreement only became public in 2010. It enabled the U.S. and the U.K. to exchange "knowledge from operations involving intercepting, decoding and translating foreign communications." The agreement forbade the parties to reveal its existence to any third party.[51]
By the late 1990s the ECHELON system was capable of intercepting satellite transmissions, public switched telephone network (PSTN) communications (including most Internet traffic), and transmissions carried by microwave. A detailed description of ECHELON was provided by New Zealand journalist Nicky Hager in his 1996 book "Secret Power". While the existence of ECHELON was denied by some member governments, a report by a committee of the European Parliament in 2001 confirmed the program's use and warned Europeans about its reach and effects.[16] The European Parliament stated in its report that the term "ECHELON" was used in a number of contexts, but that the evidence presented indicated it was a signals intelligence collection system capable of interception and content inspection of telephone calls, fax, e-mail and other data traffic globally. The report to the European Parliament confirmed that this was a "global system for the interception of private and commercial communications."[53]
Echelon spy network revealed
Imagine a global spying network that can eavesdrop on every single phone call, fax or e-mail, anywhere on the planet. It sounds like science fiction, but it's true. Two of the chief protagonists - Britain and America - officially deny its existence. But the BBC has confirmation from the Australian Government that such a network really does exist..."
9/11 and its implications on mass surveillance (2001–2009)


In the aftermath of the September 11 attacks in 2001 on the World Trade Center and Pentagon, the scope of domestic spying in the United States increased significantly. The bid to prevent future attacks of this scale led to the passage of the Patriot Act. Later acts include the Protect America Act (which removes the warrant requirement for government surveillance of foreign targets[58]) and the FISA Amendments Act (which relaxed some of the original FISA court requirements).
In 2005, the existence of STELLARWIND was revealed by Thomas Tamm. On January 1, 2006, days after The New York Times wrote that "Bush Lets U.S. Spy on Callers Without Courts,[59] the President emphasized that "This is a limited program designed to prevent attacks on the United States of America. And I repeat, limited."[60]
In 2006, Mark Klein revealed the existence of Room 641A that he had wired back in 2003.[61] In 2008, Babak Pasdar, a computer security expert, and CEO of Bat Blue publicly revealed the existence of the "Quantico circuit", that he and his team found in 2003. He described it as a back door to the federal government in the systems of an unnamed wireless provider; the company was later independently identified as Verizon.[62]
You Are a Suspect
Every purchase you make with a credit card, every magazine subscription you buy and medical prescription you fill, every Web site you visit and e-mail you send or receive, every academic grade you receive, every bank deposit you make, every trip you book and every event you attend -- all these transactions and communications will go into what the Defense Department describes as a virtual, centralized grand database. To this computerized dossier on your private life from commercial sources, add every piece of information that government has about you -- passport application, driver's license and toll records, judicial and divorce records, complaints from nosy neighbors to the F.B.I., your lifetime paper trail plus the latest hidden camera surveillance -- and you have the supersnoop's dream: a Total Information Awareness about every U.S. citizen.
— The New York Times, November 2002[63]
Acceleration of media leaks (2010–present)
On November 28, 2010, WikiLeaks and five major news outlets in Spain (El País), France (Le Monde), Germany (Der Spiegel), the United Kingdom (The Guardian), and the United States (The New York Times) began publishing the first 220 of 251,287 leaked U.S. State department diplomatic "cables" simultaneously.[64]
Other notable media leaks include the Afghan War documents leak (considered to be one of the largest leaks in U.S. military history[65]), as well as the Iraq War documents leak (A collection of 391,832 United States Army field reports[66]), and the Guantanamo Bay files leak (779 top secret documents marked NOFORN).
On March 15, 2012, the American magazine Wired published an article with the headline "The NSA Is Building the Country's Biggest Spy Center (Watch What You Say)",[67] which was later mentioned by U.S. Rep. Hank Johnson during a congressional hearing. In response to Johnson's inquiry, NSA director Keith B. Alexander testified that these allegations made by Wired magazine were untrue.[68]
U.S. agency denies data center to monitor citizens' emails
"Many unfounded allegations have been made about the planned activities of the Utah Data Center," the NSA said in a statement, noting that "one of the biggest misconceptions about NSA is that we are unlawfully listening in on, or reading emails of, U.S. citizens. This is simply not the case."
Summary of revealed surveillance details







On June 6, 2013, Britain's The Guardian newspaper began publishing a series of revelations by an as yet unknown American whistleblower, revealed several days later to be ex-CIA and ex-NSA-contracted systems analyst Edward Snowden. Snowden gave a cache of documents to two journalists: Glenn Greenwald and Laura Poitras, Greenwald later estimated that the cache contains 15,000 – 20,000 documents, some very large and very detailed, and some very small.[77][78] In over two subsequent months of publications, it became clear that the NSA had operated a complex web of spying programs which allowed it to intercept internet and telephone conversations from over a billion users from dozens of countries around the world. Specific revelations were made about China, the European Union, Latin America, Iran and Pakistan, and Australia and New Zealand, however the published documentation reveals that many of the programs indiscriminately collected bulk information directly from central servers and internet backbones, which almost invariably carry and reroute information from distant countries.
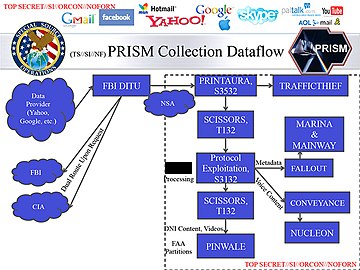
Due to this central server and backbone monitoring, many of the programs overlapped and interrelated among one another. These programs were often carried out with the assistance of US entities such as the United States Department of Justice and the FBI,[79] were sanctioned by US laws such as the FISA Amendments Act, and the necessary court orders for them were signed by the secret Foreign Intelligence Surveillance Court. Some of the NSA's programs were directly aided by national and foreign intelligence agencies, Britain's GCHQ and Australia's DSD, as well as by large private telecommunications and internet corporations, such as Verizon, Telstra,[80] Google and Facebook.[81]
Purposes
According to the April 2013 summary of documents leaked by Snowden, other than to combat terrorism, these surveillance programs were employed to assess the foreign policy and economic stability of other countries,[82] and to gather "commercial secrets".[83]
In a statement addressed to the National Congress of Brazil in early August 2013, journalist Glenn Greenwald maintained that the U.S. government had used counter-terrorism as a pretext for clandestine surveillance in order to compete with other countries in the "business, industrial and economic fields".[84][85][86]
In an interview with Der Spiegel published on August 12, 2013, former NSA Director Michael Hayden admitted that "We (the NSA) steal secrets. We're number one in it". Hayden also added: "We steal stuff to make you safe, not to make you rich".[82]
According to documents seen by the news agency Reuters, these "secrets" were subsequently funnelled to authorities across the nation to help them launch criminal investigations of Americans.[87] Federal agents are then instructed to "recreate" the investigative trail in order to "cover up" where the information originated.[87]
Targets
According to the April 2013 summary of disclosures, the NSA defined its "intelligence priorities" on a scale of "1" (highest interest) to "5" (lowest interest).[82] It classified about 30 countries as "3rd parties", with whom it cooperates but also spies on:
- Main targets: China, Russia, Iran, Pakistan and Afghanistan were ranked highly on the NSA's list of spying priorities, followed by France, Germany, Japan, and Brazil. The European Union's "international trade" and "economic stability" are also of interest.[82] Other high priority targets include Cuba, Israel, and North Korea.[88]
- North Korea: Despite being a priority target, and despite continuous surveillance from sensors located outside the country, the NSA knew little about North Korea and Kim Jong Un.[88]
- Syria: Syria was being closely monitored, particularly for signs of chemical weapons use.[88]
- Iran: suspected nuclear sites that did not show up on satellite imagery were identified by new surveillance techniques.[88]
- Irrelevant : From a US intelligence perspective, countries such as Cambodia, Laos and Nepal were largely irrelevant, as were most European countries like Finland, Denmark, Croatia and the Czech Republic.[82]
Other prominent targets included members and adherents of the internet group known as "Anonymous",[82] as well as potential whistleblowers.[89] According to Edward Snowden, the NSA targeted reporters who wrote critically about the government after 9/11.[90]
As part of a joint operation with the Central Intelligence Agency (CIA), the NSA deployed secret eavesdropping posts in eighty U.S. embassies and consulates worldwide.[70] The headquarters of NATO were also used by NSA experts to spy on the European Union.[91]
In 2013, documents provided by Edward Snowden revealed that the following intergovernmental organizations, diplomatic missions, and government ministries have been subjected to surveillance by the "Five Eyes":
| Country/ Organization |
Target | Method(s) |
|---|---|---|
| Ministry of Energy | Collection of metadata records by the Communications Security Establishment of Canada (CSEC)[92] | |
| Ministry of Foreign and European Affairs | Infiltration of virtual private networks (VPN)[93] | |
| Embassy of France in Washington, D.C | ||
| Embassy of India in Washington, D.C |
| |
| Permanent Representative of India to the United Nations | ||
| Secretariat of Public Security | ||
| Council of the European Union in Brussels |
| |
| Delegation to the United Nations in New York | ||
| Delegation to the United States in Washington, D.C | ||
| United Nations Headquarters in New York |
| |
| International Atomic Energy Agency in Vienna |
International cooperation

During World War II, the BRUSA Agreement was signed by the governments of the United States and the United Kingdom for the purpose of intelligence sharing.[50] This was later formalized in the UKUSA Agreement of 1946 as a secret treaty. The full text of the agreement was released to the public on June 25, 2010.[51]
Although the treaty was later revised to include other countries such as Denmark, Germany, Ireland, Norway, Turkey, and the Philippines,[51] most of the information sharing has been performed by the so-called "Five Eyes",[98] a term referring to the following English-speaking western democracies and their respective intelligence agencies:
 – The Defence Signals Directorate of Australia[98]
– The Defence Signals Directorate of Australia[98] – The Communications Security Establishment of Canada[98]
– The Communications Security Establishment of Canada[98] – The Government Communications Security Bureau of New Zealand[98]
– The Government Communications Security Bureau of New Zealand[98] – The Government Communications Headquarters of the United Kingdom, which is widely considered to be a leader in traditional spying due to its influence on countries that were once colonies of the British Empire.[98]
– The Government Communications Headquarters of the United Kingdom, which is widely considered to be a leader in traditional spying due to its influence on countries that were once colonies of the British Empire.[98] – The National Security Agency of the United States, which has the biggest budget and the most advanced technical abilities among the "five eyes".[98]
– The National Security Agency of the United States, which has the biggest budget and the most advanced technical abilities among the "five eyes".[98]
In 2013, media disclosures revealed how other government agencies have cooperated extensively with the "Five Eyes":
 - The Politiets Efterretningstjeneste (PET) of Denmark, a domestic intelligence agency, exchanges data with the NSA on a regular basis, as part of a secret agreement with the United States.[99]
- The Politiets Efterretningstjeneste (PET) of Denmark, a domestic intelligence agency, exchanges data with the NSA on a regular basis, as part of a secret agreement with the United States.[99]
 – The Bundesnachrichtendienst (Federal Intelligence Service) of Germany systematically transfers metadata from German intelligence sources to the NSA. In December 2012 alone, Germany provided the NSA with 500 million metadata records.[100] The NSA granted the Bundesnachrichtendienst access to X-Keyscore,[101] in exchange for Mira4 and Veras.[100] In early 2013, Hans-Georg Maaßen, President of the German domestic security agency BfV, made several visits to the headquarters of the NSA. According to classified documents of the German government, Maaßen had agreed to transfer all data collected by the BfV via XKeyscore to the NSA.[102] In addition, the BfV has been working very closely with eight other U.S. government agencies, including the CIA.[103]
– The Bundesnachrichtendienst (Federal Intelligence Service) of Germany systematically transfers metadata from German intelligence sources to the NSA. In December 2012 alone, Germany provided the NSA with 500 million metadata records.[100] The NSA granted the Bundesnachrichtendienst access to X-Keyscore,[101] in exchange for Mira4 and Veras.[100] In early 2013, Hans-Georg Maaßen, President of the German domestic security agency BfV, made several visits to the headquarters of the NSA. According to classified documents of the German government, Maaßen had agreed to transfer all data collected by the BfV via XKeyscore to the NSA.[102] In addition, the BfV has been working very closely with eight other U.S. government agencies, including the CIA.[103]
 - The SIGINT National Unit of Israel routinely receives raw intelligence data (including those of U.S. citizens) from the NSA.[104] (See also: Memorandum of understanding between the NSA and Israel)
- The SIGINT National Unit of Israel routinely receives raw intelligence data (including those of U.S. citizens) from the NSA.[104] (See also: Memorandum of understanding between the NSA and Israel)
 - In 2011, the Japanese government was asked by the NSA to intercept fiber-optic cables carrying phone and Internet data from across the entire Asia-Pacific region, including China. However, the Japanese government refused to comply.[105]
- In 2011, the Japanese government was asked by the NSA to intercept fiber-optic cables carrying phone and Internet data from across the entire Asia-Pacific region, including China. However, the Japanese government refused to comply.[105]
 - The Algemene Inlichtingen en Veiligheidsdienst (General Intelligence and Security Service) of the Netherlands has been receiving and storing user information gathered by U.S. intelligence sources such as PRISM.[106]
- The Algemene Inlichtingen en Veiligheidsdienst (General Intelligence and Security Service) of the Netherlands has been receiving and storing user information gathered by U.S. intelligence sources such as PRISM.[106]
 - The Norwegian Intelligence Service has confirmed that data collected by the agency is "shared with the Americans".[107] Kjell Grandhagen, head of Norwegian military intelligence told reporters at a news conference that "We share this information with partners, and partners share with us...We are talking about huge amounts of traffic data".[108]
- The Norwegian Intelligence Service has confirmed that data collected by the agency is "shared with the Americans".[107] Kjell Grandhagen, head of Norwegian military intelligence told reporters at a news conference that "We share this information with partners, and partners share with us...We are talking about huge amounts of traffic data".[108]
 – The Defence Ministry of Singapore and its Security and Intelligence Division have been secretly intercepting much of the fibre optic cable traffic passing through the Asian continent. Information gathered by the Government of Singapore is transferred to the Government of Australia as part of an intelligence sharing agreement. This allows the "Five Eyes" to maintain a "stranglehold on communications across the Eastern Hemisphere".[109]
– The Defence Ministry of Singapore and its Security and Intelligence Division have been secretly intercepting much of the fibre optic cable traffic passing through the Asian continent. Information gathered by the Government of Singapore is transferred to the Government of Australia as part of an intelligence sharing agreement. This allows the "Five Eyes" to maintain a "stranglehold on communications across the Eastern Hemisphere".[109]
 – The National Defence Radio Establishment of Sweden (codenamed Sardines)[110] has been working extensively with the NSA, and it has granted the "five eyes" access to underwater cables in the Baltic Sea.[110]
– The National Defence Radio Establishment of Sweden (codenamed Sardines)[110] has been working extensively with the NSA, and it has granted the "five eyes" access to underwater cables in the Baltic Sea.[110]
 - The Federal Intelligence Service (FSI) of Switzerland regularly exchanges information with the NSA, based on a secret agreement.[99][111] In addition, the NSA has been granted access to Swiss monitoring facilities in Leuk (canton of Valais) and Herrenschwanden (canton of Bern).[99]
- The Federal Intelligence Service (FSI) of Switzerland regularly exchanges information with the NSA, based on a secret agreement.[99][111] In addition, the NSA has been granted access to Swiss monitoring facilities in Leuk (canton of Valais) and Herrenschwanden (canton of Bern).[99]

Left: SEA-ME-WE 3, which runs across the Afro-Eurasian supercontinent from Japan to Northern Germany, is one of the most important submarine cables accessed by the "Five Eyes". Singapore, a former British colony in the Asia-Pacific region (blue dot), plays a vital role in intercepting internet and telecommunications traffic heading from Australia/Japan to Europe, and vice versa. An intelligence sharing agreement between Singapore and Australia allows the rest of the "Five Eyes" to gain access to SEA-ME-WE 3.[109]
Right:TAT-14, a telecommunications cable linking Europe with the United States, was identified as one of few assets of "Critical Infrastructure and Key Resources" of the USA on foreign territory. In 2013, it was revealed that British officials "pressured a handful of telecommunications and internet companies" to allow the British government to gain access to TAT-14.[112]
According to the leaked documents, aside from the Five Eyes, most other Western countries have also participatied in the NSA surveillance system and are sharing information with each other.[113] However, being a partner of the NSA does not automatically exempt a country from being targeted by the NSA. According to an internal NSA document leaked by Snowden, "We (the NSA) can, and often do, target the signals of most 3rd party foreign partners."[114]
Timeline of disclosures
| Selected headlines |
|---|


|
Edward Snowden's disclosures of the NSA's surveillance activities are a continuation of news leaks which have been ongoing since the mid-2000s.
2000—09
- 2002
In September 2002, William Binney, along with J. Kirke Wiebe and Edward Loomis, asked the U.S. Defense Department to investigate the NSA for allegedly wasting "millions and millions of dollars" on Trailblazer, a system intended to analyze data carried on communications networks such as the Internet. Binney was also publicly critical of the NSA for spying on U.S. citizens after the September 11, 2001 attacks.[119] Binney claimed that the NSA had failed to uncover the 9/11 plot despite its massive interception of data.[120]
- 2005
On December 16, 2005, The New York Times published a report under the headline "Bush Lets U.S. Spy on Callers Without Courts", which was co-written by Eric Lichtblau and the Pulitzer Prize-winning jorunalist James Risen. According to The Times, the article's date of publication was delayed for a year because of national security concerns.[121]
- 2006
In 2006, further evidence of the NSA's domestic surveillance of U.S. citizens was provided by USA Today. The newspaper released a report on May 11, 2006 regarding the NSA's "massive database" of phone records collected from "tens of millions" of U.S. citizens. According to USA Today, these phone records were provided by several telecom companies such as AT&T, Verizon and BellSouth.[116]
- 2008
In 2008, the security analyst Babak Pasdar revealed the existence of the so-called "Quantico circuit" that he and his team had set up in 2003. The circuit provided the U.S. federal government with a backdoor into the network of an unnamed wireless provider, which was later independently identified as Verizon.[62]
2010—13
- 2012
In April 2012, Edward Snowden began downloading sensitive NSA material while working for the American computer corporation Dell Inc.[122] By the end of the year, Snowden had made his first contact with journalist Glenn Greenwald of The Guardian.[123]
- January—May 2013
In January 2013, Snowden contacted documentary filmmaker Laura Poitras.[124] In March 2013, Snowden took up a new job at Booz Allen Hamilton in Hawaii, specifically to gain access to additional top-secret documents that could be leaked.[122] In April 2013, Poitras asked Greenwald to meet her in New York City.[123] In May 2013, Snowden was permitted temporary leave from his position at the NSA in Hawaii, on the pretext of receiving treatment for his epilepsy.[125] Towards the end of May, Snowden flew to Hong Kong.[126]
2013—present
June
After the editor of The Guardian held several meetings in New York City, it was decided that Greenwald, Poitras and Ewen MacAskill would fly to Hong Kong to meet Snowden. On June 6, 2013, the first media disclosure was published simultaneously by Greenwald (The Guardian) and Poitras (The Washington Post).[127][128]
It was reported that the NSA had collected phone records from over 120 million Verizon subscribers, according to a top secret court order leaked by Snowden.[118]
During the 2009 G-20 London Summit, the British intelligence agency Government Communications Headquarters (GCHQ) had intercepted the communications of foreign diplomats.[71] The GCHQ has been intercepting and storing mass quantities of fiber-optic traffic via Tempora.[129]
The Guardian revealed that XKeyscore allows analysts to search with no prior authorization through vast databases containing emails, online chats and the browsing histories of millions of individuals.[130][131][132] Microsoft "developed a surveillance capability to deal" with the interception of encrypted chats on Outlook.com, within five months after the service went into testing. NSA had access to Outlook.com emails because “Prism collects this data prior to encryption.”[133]
During specific episodes within a four-year period, the NSA hacked several Chinese mobile-phone companies,[134] the Chinese University of Hong Kong and Tsinghua University in Beijing,[135] and the Asian fiber-optic network operator Pacnet.[136] Documents provided by Edward Snowden and seen by Der Spiegel revealed that the NSA spied on various diplomatic missions of the European Union (EU), including the EU's delegation to the United States in Washington D.C.,[96] the EU's delegation to the United Nations in New York,[96] the Council of the European Union in Brussels,[96] and the United Nations Headquarters in New York.[97] Only Australia, Canada, New Zealand and the UK are explicitly exempted from NSA attacks, whose main target in the EU is Germany.[137]
The NSA collected, from 2001 to 2011 via Stellar Wind, vast amounts of records detailing the email and internet usage of Americans,[138] and after the program end of Stellar Wind due to operational and resource reasons other programs such as ShellTrumpet.[139] A method of bugging encrypted fax machines used at an EU embassy is codenamed Dropmire.[140]
The NSA's Office of Tailored Access Operations (TAO) collects intelligence on foreign targets by "hacking into their computers and telecommunications systems, cracking passwords, compromising the computer security systems protecting the targeted computer, stealing the data stored on computer hard drives, and then copying all the messages and data traffic passing within the targeted email and text-messaging systems", in a process known as 'computer network exploitation' (CNE).[141]
July
According to the Brazilian newspaper O Globo, the NSA spied on millions of emails and calls of Brazilian citizens,[142][143] while Australia and New Zealand have been aiding the United States in their surveillance program.[144][145]
The NSA gave the German intelligence agencies BND and BfV access to X-Keyscore.[101] In return, the BND turned over copies of two systems named Mira4 and Veras, reported to exceed the NSA's SIGINT capabilities in certain areas.[100] The NSA also provided the BND with analysis tools so that the BND can monitor foreign data streams flowing through Germany.[146][147]
Even if there is no reason to suspect U.S. citizens the CIA's National Counterterrorism Center is allowed to examine the government files of for possible criminal behavior. Previously the NTC was barred to do so, unless a person was a terror suspect or related to an investigation.[148]
Snowden also confirmed that Stuxnet was cooperatively developed by the United States and Israel.[149] In a report unrelated to Edward Snowden, the French newspaper Le Monde revealed thet France's DGSE was also undertaking mass surveillance, which it described as "illegal and outside any serious control".[150][151]
1. Uptstream — Under the first type of collection, data en route to its final destination would be intercepted via FAIRVIEW, STORMBREW, BLARNEY, and OAKSTAR
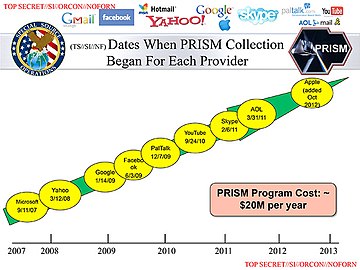
2. PRISM — Under the second type of collection, data that has already reached its final destination would be directly harvested from the servers of the following U.S. service providers: Microsoft, Yahoo!, Google, Facebook, Paltalk, AOL, Skype, YouTube, and Apple Inc.
August
Documents leaked by Edward Snowden and jointly disclosed by Süddeutsche Zeitung (SZ) and Norddeutscher Rundfunk revealed that several telecom operators have played a key role in helping the British intelligence agency Government Communications Headquarters (GCHQ) tap onto worldwide fiber-optic communications.[152][153] The telecom operators are:
- Verizon Business (codenamed "Dacron")[154]
- British Telecommunications (codenamed "Remedy")[154]
- Vodafone Cable (codenamed "Gerontic")[154]
- Global Crossing (codenamed "Pinnage")[154]
- Level 3 (codenamed "Little")[154]
- Viatel (codenamed "Vitreous")[154]
- Interoute (codenamed "Streetcar")[154]
Each of them were assigned a particular area of the international fiber-optic network for which they were individually responsible. The following networks have been infiltrated by the GCHQ: TAT-14 (Europe-USA), Atlantic Crossing 1 (Europe-USA), Circe South (France-UK), Circe North (The Netherlands-UK), Flag Atlantic-1, Flag Europa-Asia, SEA-ME-WE 3 (Southeast Asia-Middle East-Western Europe), SEA-ME-WE 4 (Southeast Asia-Middle East-Western Europe), Solas (Ireland-UK), UK-France 3, UK-Netherlands 14, ULYSSES (Europe-UK), Yellow (UK-USA) and Pan European Crossing.[112]
Telecommunication companies who participated were "forced" to do so and had "no choice in the matter".[112] Some of the companies were subsequently paid by GCHQ for their participation in the infiltration of the cables.[155] According to the SZ the GCHQ has access to the majority of internet and telephone communications flowing throughout Europe, can listen to phone calls, read emails and text messages, see which websites internet users from all around the world are visiting.[154] It can also retain and analyse nearly the entire European internet traffic.[153]
The GCHQ is collecting all data transmitted to and from the United Kingdom and Northern Europe via the undersea fibre optic telecommunications cable SEA-ME-WE 3. Singaporean intelligence co-operates with Australia in accessing and sharing communications carried by the SEA-ME-WE-3 cable. The Australian Signals Directorate, is also in a partnership with British, American and Singaporean intelligence agencies to tap undersea fibre optic telecommunications cables that link Asia, the Middle East and Europe and carry much of Australia's international phone and internet traffic.[109]
The US runs a top-secret surveillance program, code named Special Collection Service, based in over 80 consulates and embassies worldwide, including Frankfurt Germany and Vienna, Austria.[97] The NSA hacked the United Nations' video conferencing system in Summer 2012 in violation of a UN agreement.[97] The Bundesnachrichtendienst is providing the NSA with metadata collected from German systems. In December 2012 alone, Germany provided the NSA with 500 million metadata records.[156][157][158] The N.S.A. is not just intercepting the communications of Americans who are in direct contact with foreigners targeted overseas, but also searching the contents of vast amounts of e-mail and text communications into and out of the country by Americans who mention information about foreigners under surveillance.[159] It also spied on the Al Jazeera and gained access to its internal communications systems.[160]
The NSA has built a surveillance network that has the capacity to reach roughly 75% of all U.S. Internet traffic.[161][162][163] U.S. Law-enforcement agencies use tools used by computer hackers to gather information on suspects.[164][165] An internal NSA audit from May 2012 identified 2776 incidents i.e. violations of the rules or court orders for surveillance of Americans and foreign targets in the U.S. in the period from April 2011 through March 2012, while U.S. officials stressed that any mistakes are not intentional.[166][167][168][169][170][171][172]
The FISA Court that is supposed to provide critical oversight of the U.S. government's vast spying programs has limited ability to do and it must trust the government to report when it improperly spies on Americans.[173] A legal opinion declassified on August 21, 2013 revealed that the NSA intercepted for three years as many as 56,000 electronic communications a year of Americans who weren’t suspected of having links to terrorism, before FISC court that oversees surveillance found the operation unconstitutional in 2011.[174][175][176][177][178] By the Corporate Partner Access Project for major U.S. telecommunications providers these providers receive hundreds of millions of dollars a year from the NSA for clandestine access to their communications networks and filtering vast traffic flows for foreign targets.[179]
A letter drafted by the Obama administration specifically to inform Congress of the government's mass collection of Americans’ telephone communications data was withheld from lawmakers by leaders of the House Intelligence Committee in the months before a key vote affecting the future of the program.[180][181]
The NSA paid GCHQ over £100 Million between 2009 and 2012, in exchange for these funds GCHQ "must pull its weight and be seen to pull its weight." Documents referenced in the article explain that weaker laws regarding spying are "a selling point". GCHQ is also developing the technology to "exploit any mobile phone at any time."[182] The NSA has under a legal authority a secret backdoor into its databases gathered from large Internet companies enabling it to search for US citizens' email and phone calls without a warrant.[183][184]
The Privacy and Civil Liberties Oversight Board urged the U.S. intelligence chiefs to draft stronger US surveillance guidelines on domestic spying after finding that several of those guidelines have not been updated up to 30 years.[185][186] US intelligence analysts have deliberately broken rules designed to prevent them from spying on Americans by choosing to ignore so-called "minimisation procedures" aimed at protecting privacy[187][188][189]
After the Foreign Secret Intelligence Court ruled in October 2011 that some of the NSA's activities were unconstitutional paid millions of dollars to cover the costs of major internet companies involved in the Prism surveillance program[190]
"Mastering the Internet" (MTI) is part of the Interception Modernisation Programme (IMP) of the British government that involves the insertion of thousands of DPI (deep packet inspection) "black boxes" at various internet service providers, as revealed by the British media in 2009.[191]
In 2013, it was further revealed that the NSA had made a £17.2 million financial contribution to the project, which is capable of vacuuming signals from up to 200 fibre-optic cables at all physical points of entry into Great Britain.[192]
September
The Guardian and the New York Times reported on secret documents leaked by Snowden showing that the NSA has been in "collaboration with technology companies" as part of "an aggressive, multipronged effort" to weaken the encryption used in commercial software, that the GCHQ has a team dedicated to cracking "Hotmail, Google, Yahoo and Facebook" traffic, and other revelations.[193][194][195][196][197][198]
French intelligence agencies are cooperating under the codename "Lustre" with the Five Eyes alliance by systematically providing them with information after France signed a cooperation treaty with the alliance. Israel, Sweden and Italy are also cooperating with American and British intelligence agencies.[199] Germany's domestic security agency Bundesverfassungsschutz transmitted regularly informations of persons monitored in Germany to the NSA, CIA and seven other members of the US Intelligence community in exchange for information and espionage software.[200][201][202]
A special branch of the NSA called "Follow the Money" (FTM) widely monitors international payments, banking and credit card transactions and later stores the collected data in the NSA's own financial databank "Tracfin".[203] The National Security Agency directly targeted the communications of president Dilma Rousseff and her top aides.[204] It also spied on Brazil's oil firm Petrobras as well as French diplomats and gained access to the private network of the Ministry of Foreign Affairs of France and the SWIFT network.[205]
The N.S.A. uses the analysis of phone call and e-mail logs of American citizens to create sophisticated graphs of their social connections that can identify their associates, their locations at certain times, their traveling companions and other personal information.[206] The NSA routinely shares raw intelligence data with Israel without first sifting it to remove information about US citizens.[104][207]
In an effort codenamed GENIE, computer specialists can control foreign computer networks using "covert implants,” a form of remotely transmitted malware on tens of thousands of devices annually.[208][209][210][211] As worldwide sales of smartphones began exceeding those of feature phones, the NSA decided to take advantage of the smartphone boom. This is particularly advantageous because the smartphone combines a myriad of data that would interest an intelligence agency, such as social contacts, user behavior, interests, location, photos and credit card numbers and passwords.[212]
An internal NSA report from 2010 stated that the spread of the smartphone has been occurring "extremely rapidly"—developments that "certainly complicate traditional target analysis."[212] According to the document, the NSA has set up task forces assigned to several smartphone manufacturers and operating systems, including Apple Inc.'s iPhone and iOS operating system, as well as Google's Android mobile operating system.[212] Similarly, Britain's GCHQ assigned a team to study and crack the BlackBerry.[212]
Under the heading "iPhone capability," the document notes that there are smaller NSA programs, known as "scripts," that can perform surveillance on 38 different features of the iOS 3 and iOS 4 operating systems. These include the mapping feature, voicemail and photos, as well as Google Earth, Facebook and Yahoo! Messenger.[212]
- A secret NSA presentation leaked to Laura Poitras and Der Spiegel regarding the NSA's iPhone Location Services[213]
-
Who knew in 1984...Who knew in 1984...
-
...that this would be big brother......that this would be big brother...
-
...and the Zombies would be paying customers?[213]...and the Zombies would be paying customers?[213]
October
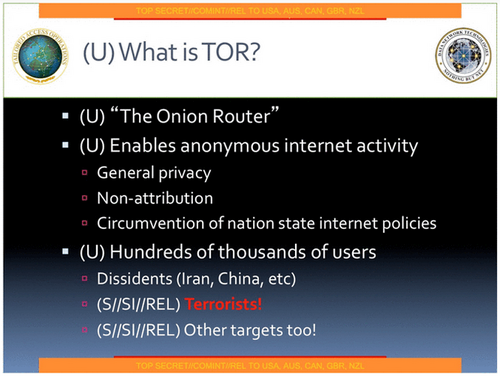
On October 4, 2013 the Washington Post and the Guardian reported that the NSA and the GCHQ has made repeated attempts to develop attacks against people using Tor.[214][215][216][217][218][219][220][221][222]
Canada's Communications Security Establishment used a software program called Olympia to map the Brazil's Mines and Energy Ministry communications by targeting "metadata" of phone calls and emails from and to the Brazilian ministry.[223][224] The Australian Federal Government knew about the internet spying program PRISM months before Edward Snowden made details public.[225][226]
The NSA monitored the president's public email account of former Mexican president Felipe Calderón (thus gaining access to the communications of high ranking cabinet members), the E-Mails of several high-ranking members of Mexico's security forces and text and the mobile phone communication of current Mexican president Enrique Peña Nieto.[227][228] The NSA tries to gather cellular and landline phone numbers — often obtained from American diplomats — for as many foreign officials as possible. The contents of the phone calls are stored in computer databases that can regularly be searched using keywords.[229][230]
The NSA has been monitoring telephone conversations of 35 world leaders.[231] The U.S. government's first public acknowledgment that it tapped the phones of world leaders was reported on October 28, 2013 by the Wall Street Journal after an internal U.S. government internal review turned up NSA monitoring of some 35 world leaders.[232] The GCHQ has tried to keep its mass surveillance program a secret because it feared a "damaging public debate" on the scale of its activities which could lead to legal challenges against them.[233]
The Guardian revealed that the NSA had been monitoring telephone conversations of 35 world leaders after being given the numbers by an official in another US government department. A confidential memo revealed that the NSA encouraged senior officials in such Departments as the White House, State and The Pentagon, to share their "Rolodexes" so the agency could add the telephone numbers of leading foreign politicians to their surveillance systems. Reacting to the news, German leader Angela Merkel, arriving in Brussels for an EU summit, accused the US of a breach of trust, saying: "We need to have trust in our allies and partners, and this must now be established once again. I repeat that spying among friends is not at all acceptable against anyone, and that goes for every citizen in Germany."[231] The NSA collected in 2010 data on ordinary Americans’ cellphone locations, but later discontinued it because it had no “operational value.”[234]
Under a programm known as MUSCULAR the National Security Agency, working with its British counterpart, the Government Communications Headquarters (GCHQ), has secretly broken into the main communications links that connect Yahoo and Google data centers around the world and thereby gained the abilitiy to collect metadata and content at will from hundreds of millions of user accounts.[235][236][237][238][239]
The mobile phone of German Chancellor Angela Merkel might have been tapped by US intelligence.[240][241][242][243][244][245][246] According to the Spiegel this monitoring goes back to 2002[247][248][249] and ended in the summer of 2013,[232] while the New York Times reported that Germany has evidence that the NSA's surveillance of Merkel began during George W. Bush's tenure.[250]
On October 31, 2013, Hans-Christian Ströbele, a member of the German Bundestag, met Snowden in Moscow and revealed the former intelligence contractor's readiness to brief the German government on NSA spying.[251]
A highly sensitive signals intelligence collection program named Stateroom involing the interception of radio, telecommunications and internet traffic is conducted from sites at US embassies and consulates and from the diplomatic missions of other "Five eyes" intelligence partners including Australia, Britain and Canada in 80 locations around the world. The program conducted at US diplomatic missions is run in concert by the US intelligence agencies NSA and CIA in a joint venture group called "Special Collection Service" (SCS), whose members work undercover in shielded areas of the American Embassies and Consulates, where they are officially accredited as diplomats and as such enjoy special privileges. Under diplomatic protection, they are able to look and listen unhindered. The SCS for example used the American Embassy near the Brandenburg Gate in Berlin to monitor communications in Germany's government district with its parliament and the seat of the government.[246][252][253][254]
As part of a NSA program called Stateroom Australia's used Australian diplomatic embassies Australia's Defence Signals Directorate operates the clandestine surveillance facilities to intercept phone calls and data across Asia.[253][255]
The NSA targeted in France both people suspected of association with terrorist activities as well as people belonging to the worlds of business, politics or French state administration. The NSA monitored and recorded the content of telephone communications and the history of the connections of each target i.e. the metadata.[256][257] According to the Wall Street Journal data allegedly collected by the NSA in France was actually collected by French intelligence agencies outside France and then shared with the United States.[258] This was confirmed by National Security Agency director Keith Alexander on October 29, 2013, when he said foreign intelligence services collected phone records in war zones and other areas outside their borders and provided them to the NSA.[259] The French newspaper Le Monde also disclosed new PRISM and Upstream slides (See Page 4, 7 and 8) coming from the "PRISM/US-984XN Overview" presentation.[260]
November
The New York Times reported that the NSA carries out an eavesdropping effort, dubbed Operation Dreadnought, against the Iranian leader Ayatollah Ali Khamenei. During his 2009 visit to Iranian Kurdistan, the agency collaborated with the GCHQ and the US' National Geospatial-Intelligence Agency, collecting radio transmissions between aircraft and airports, examining Khamenei's convoy with satellite imagery, and enumerating military radar stations. According to the story, an objective of the operation is "communications fingerprinting": the ability to distinguish Khamenei's communications from those of other people in Iran.[261]
According to the British newspaper The Independent, the British intelligence agency GCHQ maintains a listening post on the roof of the British Embassy in Berlin that is capable of intercepting mobile phone calls, wi-fi data and long-distance communications all over the German capital, including adjacent government buildings such as the Reichstag (seat of the Germany's parliament) and the Chancellery (seat of Germany's government) clustered around the Brandenburg Gate.[262]
Operating under the code-name "Quantum Insert", the GCHQ set up a fake website masquerading as LinkedIn, a social website used for professional networking, as part of its efforts to install surveillance software on the comptuters of the telecommunications operator Belgacom.[263] In addition, the headquarters of the oil cartel OPEC were infiltrated by the GCHQ as well as the NSA, which bugged the computers of nine OPEC employees and monitored the General Secretary of OPEC.[263]
For more than three years the GCHQ has been using an automated monitoring system code-named "Royal Concierge" to infiltrate the reservation systems of at least 350 upscale hotels in many different parts of the world in order to target, search and analyze reservations to detect diplomats and government officials.[264] First tested in 2010, the aim of the "Royal Concierge" is to track down the travel plans of diplomats, and it is often supplemented with surveillance methods related to human intelligence (HUMINT). Other covert operations include the wiretapping of room telephones and fax machines used in targeted hotels as well as the monitoring of computers hooked up to the hotel network.[264]
In November 2013 The Guardian referred to the claim that the Australian spy agencies attempted to listen to the private phone calls of the president of Indonesia and his wife. The Indonesian foreign minister, Marty Natalegawa, confirmed that he and the president had contacted the ambassador in Canberra. Natalegawa said any tapping of Indonesian politicians’ personal phones “violates every single decent and legal instrument I can think of – national in Indonesia, national in Australia, international as well”.[265]
Under a secret deal approved by British intelligence officials the NSA stored and analyzed since 2007 phone, internet and email records of UK citizens not suspected of any wrongdoing. The NSA has also in 2005 proposed a procedure for spying on the citizens of the UK and other Five-Eyes nations alliance, even where the partner government has explicitly denied the US permission to do so. Under the proposal, partner countries must not be informed about this surveillance, or even the procedure itself.[266]
Towards the end of November, The New York Times released an internal NSA report outlining the agency's efforts to expand its surveillance abilities.[267] The five-page document asserts that the law of the United States has not kept up with the needs of the NSA to conduct mass surveillance in the "golden age" of signals intelligence, but there are grounds for optimism because, in the NSA's own words:
"The culture of compliance, which has allowed the American people to entrust NSA with extraordinary authorities, will not be compromised in the face of so many demands, even as we aggressively pursue legal authorities..."[268]
The report, titled "SIGNT Strategy 2012-2016", also said that the U.S. will try to influence the "global commercial encryption market" through "commercial relationships", and emphasized the need to "revolutionize" the analysis of its vast data collection to "radically increase operational impact".[267]
On November 23, 2013, the Dutch newspaper NRC Handelsblad reported that the Netherlands was targeted by U.S. intelligence agencies in the immediate aftermath of World War II. This period of surveillance lasted from 1946 to 1968, and also included the interception of the communications of other European countries including Belgium, France, West Germany and Norway.[269]

2013 Disclosures by category
Court orders, memos and policy documents
- Memorandum of understanding between the NSA and the Israel SIGINT National Unit (ISNU)
- April 2013 FISC Order demanding that Verizon hand over all telephony metadata to NSA. The order had been initially granted in May 2006. In 2009 the FISC discovered that the government had made repeated and substantial misrepresentations to the court about its use, and had routinely been "running queries of the metadata using querying terms that did not meet the required standard for querying." It further concluded that the violations had been routine and systematic.[271]
- Legal Justification of the bulk telephony metadata collection (officially released)[272]
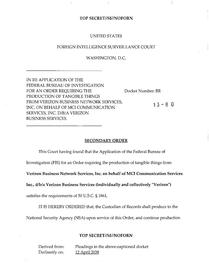
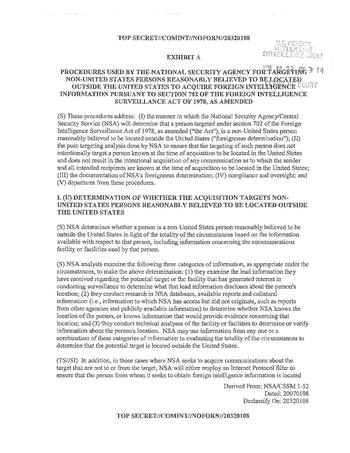
- 2009 NSA Procedures for Targeting Foreigners for Surveillance
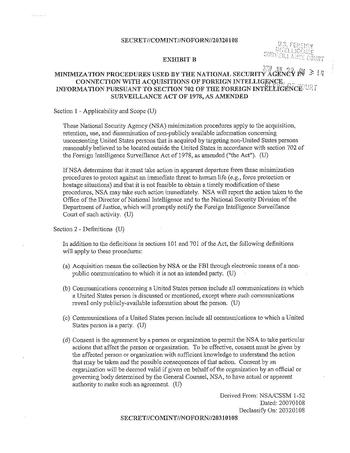
- 2009 NSA Procedures for Minimizing collection on US Persons
- 2011 NSA Procedures for Minimizing collection on US Persons (officially released)[273]
- Reference to a 2011 Change in the court-approved Minimization Procedures allowing analysts to run search queries using US persons' identifiers if there is "effective" oversight by NSA (it is not publicly known if such oversight has been established, or if any such searches have been conducted).[274] The court order mentioned was later officially released.[275]
- October 2011 Court decision finding NSA's upstream collection program, which collected tens of thousands of non-target communications, to have violated the law. It held, citing multiple Supreme Court precedents, that the Fourth Amendment applies to the contents of all communications, whatever the means (they are "papers"). It also finds that the NSA's minimization and targeting policies to be legally and/or constitutionally deficient, and recommends changes. (officially released).[174][175][176][177][178][275][276][277][278][279] Additional findings:
- The collection of Upstream data had begun before a court order approving it, in violation of 50 USC § 1809(a), which makes it a crime to engage in, use or disseminate surveillance knowing, or having reason to know such surveillance was not authorized. [280]
- March 2009 FISC ruling showing a consistent pattern of misrepresentations of the bulk telephone metadata collection program by the government to the Court. It also held that the data was being routinely queried in ways that did not meet "reasonable articulatable suspicion", demonstrating inadequate safeguards in the software and training of analysts. Showing that "thousands of violations resulted from the use of identifiers that were not "RAS-approved by analysts who were not even aware that they were accessing BR metadata," and that in 2006 "there was no single person [in the NSA] who had a complete understanding of the BR FISA system architecture," a situation which persisted until February 2009 or later. RAS is shorthand for Reasonable Articulatable Suspicion. The Court nonetheless reapproved the collection of bulk phone metadata, while mandating additional safeguards and training, and "end-to-end system engineering reviews," and reports from the review. (Officially released by court order)[281][282][283][284][285][286][287]
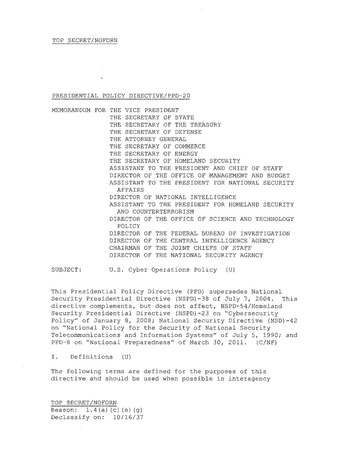
- October 2012 Presidential Policy Directive 20 (PPD20), outlining cyberwarfare.
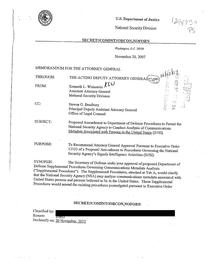
- 2007 Michael Mukasey memo proposing broader powers.
- April 2013 list of US Spying targets and topics by priority. The top priority countries are: Iran, Russia, China, Pakistan, North Korea and Afghanistan. Germany, France, the European Union, and Japan are mid-level priorities; Italy and Spain rank lower.[288][289]
- FY 2013 Intelligence "Black Budget" Summary.[88][290]
- A memorandum of understanding concerning US sharing of raw SIGINT with Israel. The data has not been scrubbed to eliminate US persons, it asks Israel not to deliberately target US persons, however the agreement allows Israel to retain US person data for one full year. The memorandum is not legally binding. A separate document states "And there are other kinds of CI threats that are right on our midst. For example, one of NSA's biggest threats is actually from friendly intelligence services, like Israel.", it continues "Balancing the SIGINT exchange between US and Israeli needs has been a constant challenge. In the last decade, it arguably tilted heavily in favor of Israeli security concerns. 9/11 came and went, and with NSA's only true Third Party CT relationship being driven almost entirely driven by the needs of the partner." [291]
- September 13, 2013 FISC Court order declassifing all the legal opinions relating to Section 215 of the Patriot Act written after May 2011 that aren't already the subject of Freedom of Information Act litigation. The FISA Court ruled that the White House must identify the opinions in question by October 4, 2013.[292][293][294]
- 1,000 pages of documents were released by James R. Clapper Jr. on November 19, 2013 in response to lawsuits filed by the American Civil Liberties Union and the Electronic Frontier Foundation and a directive by U.S. President Barack Obama. Among the documents are what appeared to be the original court document authorizing the National Security Agency to conduct sweeping collections of Americans’ electronic communications records for counterterrorism purposes, the NSA’s failure to abide by court-imposed rules to protect Americans’ privacy, reports to Congress, training slides and regulations issued under President Obama.[295][296][297][298][299]
Reports
- 2009 OIG report on STELLARWIND
- Extracts from reports relating to XKeyscore. One entitled "Tales from the Land of Brothers Grimm" and others detailing the successes of said software, another is a note from an analyst who felt that he always had one foot in prison when using it. XKeyscore is also described as "big and scary, strong and powerful" and lets an analyst do whatever they like.[300]
- Reports detailing thousands of privacy violations[301]
- Numerous reports relating to drones, including "Threats to Unmanned Aerial Vehicles", a report summarizing attempts to shoot down, intercept, control or otherwise spoof drones. While the report details vulnerabilities of specific aircraft, the document itself has not been published, but only excerpts described. Other reports detail American spin efforts, suggesting that the phrases "drone strike," "kill list," "robot warfare," "Aerial Assassins" be avoided, offering "lethal UAV operations" instead, and also terms like "Pre-emptive and Preventive Military Action" and "Inherent Right of Self Defense." Likewise, reports detail efforts by Al-Qaeda to spin, portraying attacks as cowardly and immoral. Analysts also questioned whether America was losing rhetorical battle in courts, media, and public opinion. Another report stated that drone strikes "could be brought under increased scrutiny, perceived to be illegitimate, openly resisted or undermined."[302]
- The US learned that Pakistan engaged in a pattern of extrajudicial killings, mostly against militants. However, not all targets militants, Pakistan also planned to murder a human rights activist, Asma Jahangir, while she was on a visit to India. The plot was aborted when she learned of it. The US sought to avoid public disclosure of this, and other incidents.[303][304]
- The NSA and GCHQ have access to user data in iPhones, BlackBerrys, and Android phones. They are able to read almost all smartphone information, including SMS, location, emails, and notes.[305]
Collection and analysis programs or hardware
- Boundless Informant – Computer program that physically performs the data collection.[306]
- Dropmire – A program that specifically targets foreign embassies and diplomats
- XKeyscore – A program which allows searching collected data in a variety of ways.[166][307]
- SHELLTRUMPET – A metadata program that targets international communications.[139]
- Unified Targeting Tool (UTT) – A graphical frontend for querying databases.[166][308]
- LOPERS – A software based system to spy on PSTNs[309]
- TURBULENCE – Includes cyber-warfare capabilities, such as targeting enemies with malware. (updates to existing knowledge)
- JUGGERNAUT – A system to intercept mobile networks, including voice, fax, data, and text.[309]
- SPYDER[166]
- CHALKFUN[166]
- VLR – Visitor Location Register[166]
- TransX[166]
- RAGTIME – A blanket term for any of four different surveillance programs[166][167]
- Special Collection Service – Joint CIA/NSA eavesdropping team focused based in about 80 US embassies and consulates around the world. There are known branches in Frankfurt and Vienna. According to Der Spiegel, many of their operations are a direct violation of at least 3 signed treaties: "The Convention on the Privileges and Immunities of the United Nations of 1946, the Vienna Convention on Diplomatic Relations of 1961, and a signed an agreement in 1947 that rules out all undercover operations.[310]
- STATEROOM – Surveillance on embassies and consulates. Highly Classified.[310]
- BULLRUN, named after the Battle of Bull Run. - Bullrun refers to the NSA's set of codebreaking capabilities, including the use of Computer Network Exploitation (hacking) to obtain keys, weakening of encryption standards and providing backdoors to the same.[193] The following codenames are known to be related to BULLRUN: APERIODIC, AMBULANT, AUNTIE, PAINTEDEAGLE, PAWLEYS, PITCHFORD, PENDLETON, PICARESQUE, and PIEDMONT. No further explanation of the above codenames has been provided to date.[311]
- Edgehill, named after the Battle of Edgehill - A program similar to BULLRUN, operated by the GCHQ.[193]
- Treasure Map, near real-time, interactive map of the global Internet. Collects Wi-Fi network and geolocation data, and the traffic of 30-50 million unique Internet addresses. It can reveal the location and owner of a computer, mobile device or router on a daily basis. NSA boasts that the program can map “any device, anywhere, all the time.”[267]
Relationships with corporate partners
- Special Source Operations (SSO) – Is a division of the NSA responsible for all programs which collaborate with corporate entities.[79]
- Upstream collects data from fiber-optic cables and internet backbones.[168][312]
- Codenames of companies participating in Upstream: BLARNEY (a surveillance program which was established by the NSA with AT&T and which operates at or near key fiber-optic landing points in the U.S. to capture foreign communications coming in and out of the country),[161][313] STORMBREW, FAIRVIEW (a highly classified program for tapping into the world's intercontinental fiber-optic cables according to NSA whistleblower Thomas Andrews Drake),[313] and OAKSTAR. There are conflicting sources: some that call these "programs",[161][314][315] versus the official statement called "The National Security Agency: Missions, Authorities, Oversight and Partnerships" that describes them as codenames of cooperating companies.[316][317] A third source, just released groups them with describes them as "programs authorized to collect cable transit traffic passing through US Gateways with both sides of the communication being foreign.[166]The FY 2013 budget for the above programs is as follows:[179]
- Miscellaneous codenames of companies: LITHIUM[316]
- RAMPART – Described as being part of Special Source operations, there is at least one known subdivision.[318]
- RAMPART-T – Started in 1991 or earlier, documents describe this program as: "Penetration of hard targets at or near leadership level". The information is intended for "the president and his national security advisers". Rampart-T is aimed at China, Russia, and Eastern European countries, there are around 20 nations targeted.[310]
- Microsoft allows the NSA to bypass encryption on Outlook.com.
- Names and Codenames of companies assisting GCHQ:
- Verizon Business (codenamed "Dacron")
- British Telecommunications (codenamed "Remedy")
- Vodafone Cable (codenamed "Gerontic")
- Global Crossing (codenamed "Pinnage")
- Level 3 (codenamed "Little")
- Viatel (codenamed "Vitreous")
- Interoute (codenamed "Streetcar")
NSA databases
- PINWALE – Stores email and text[131]
- NUCLEON – Stores voice data[319]
- MAINWAY – Stores telephony metadata (i.e. call records)[320]
- MARINA – Stores Internet metadata[131][320]
- TRAFFICTHIEF – Stores metadata from a subset of assigned targets.
- CLOUD/ABR[166]
- DISHFIRE[166]
- FASTSCOPE[166]
- SIGINT NAVIGATOR[166]
- TRACFIN - A database of financial information.[166][321]
- TUNINGFORK[166]
- OCTAVE – A database with a graphical frontend[166][308]
- ANCHORY – A database of completed SIGINT reports.[166][319]
- Nymrod – Apparently a database of names (appears in UTT Screenshot)[308]
Signals intelligence directorates (SIDs)
- PRINTAURA – According to Ambinder, "NSA Unit involved in data filtering for TRAFFICTHIEF"[319]
- Protocol Exploitation – Sorts data types into specific databases[312][319]
Technical directorates
Names associated with specific targets
- Apalatchee = The EU mission by the East River, in New York.[310]
- Magothy = The EU embassy in Washington, DC. This embassy had its internal videoconferencing, and other areas of the computer network tapped. Both by the US, and by the Chinese. The US effort was conducted by the team working for the BLARNEY program.[310]
- Wabash = French diplomatic office in Washington. This office was bugged.[322]
- Blackfoot = French diplomatic office in the UN in New York. This office was bugged and computer screen captures obtained.[322]
- KATEEL = Brazilian embassy in Washington.[323]
- POCOMOKE = Brazilian Permanent Mission to the UN in New York.[323]
Uncategorized or insufficiently described codenames.
- CERF CALL MOSES1[309]
- CONVEYANCE – Provide filtering for PRISM.[312]
- EVILOLIVE- Collects internet traffic and data.[139]
- FACELIFT[318]
- FALLOUT – Provides filtering for PRISM .[312]
- LONGHAUL - Involved in the process of decrypting communications.[193]
- MATRIX[309]
- MOONLIGHTPATH[139][324][325]
- SPINNERET[139][324][325]
- STEELKNIGHT[326]
- CASPORT[166]
- DANCINGOASIS[310]
GCHQ operations
The Government Communications Headquarters (GCHQ) is the main British intelligence agency responsible for providing signals intelligence (SIGINT) and information assurance to the British government and armed forces.
- Tempora – Collects data from transatlantic fibre-optic cables of major telecommunications corporations by directly tapping on them and from Internet backbones. Tempora uses intercepts on the fibre-optic cables that make up the backbone of the internet to gain access to swaths of internet users' personal data. The intercepts are placed in the United Kingdom and overseas, with the knowledge of companies owning either the cables or landing stations. It is a GCHQ program to create a large-scale "Internet buffer" which stores Internet content for three days and metadata for up to 30 days.[233][312][327]
- Britain runs a large-scale intercept station in the Middle East, capable of tapping underwater fiber-optic cables and satellites, and extracting email, telephone, and web traffic. The information is then passed to the GCHQ and shared with the NSA. The operation costs around £1 billion and is still being assembled. It is part of the "Tempora" project.[328] Edward Snowden disputes the Independent's claim that he, or anyone he has had direct contact with is the source of this information.[329] Süddeutsche Zeitung's fiber optic revelations were also described as having been obtained from GC-Wiki by Snowden.[112]
- GCHQ is believed to have forced some six global telecommunications and Internet companies to allow them to access more than 14 fiber optic cables that transport telephone communications.[112] The six companies, BT, Vodafone, Viatel, Interoute, Verizon and Level-3, gave GCHQ access to the cables in return for payment, it is believed the companies had no choice in this decision.[112] Three of the cables' terminal stations are on German territory; two of the cables are partially owned by Deutsche Telekom, who have denied knowledge of or participation in GCHQ's activities.[112]
- Spying on the 2009 G20 Summit in London.
- Life and times of GCHQ employees.
- GC-Wiki – An internal wiki at GCHQ.[328]
- Access to the majority of Internet and telephone communications throughout Europe, and occasionally as far as the United States.[112]
- GCHQ has a team dedicated to cracking encrypted traffic on Hotmail, Google, Yahoo and Facebook.[193]
- The Belgian telecom company Belgacom reports that it had been hacked, and has filed criminal charges, and will be cooperating with the investigation into the hacking. "The inquiry has shown that the hacking was only possible by an intruder with significant financial and logistic means," they said. "This fact, combined with the technical complexity of the hacking and the scale on which it occurred, points towards international state-sponsored cyber espionage." [330] According to documents released by Der Spiegel, the operation against Belgacom was entitled 'Operation Socialist' and was done by the GCHQ for the purpose of enabling Man-in-the-middle attacks against smartphones.[331][332]
NSA operations
- Hacking Tsinghua University, and also Pacnet in China.
- Spying on Latin America with the help of Global Crossing.
- The NSA operates the global monitoring network Special Collection Service that collects from more than 80 embassies and consulates worldwide, often without the knowledge or consent of the host country.[97][333]
- The NSA spied on a UN videoconferencing system, in violation of the US agreement with the UN not to do so. In the process NSA discovered that the Chinese had already done so, and then started analyzing what the Chinese were taking. Shortly thereafter, the NSA gained access to approximately 500 other UN channels of communications.[97][333][334]
- Additional details of the raid on Osama bin Laden's Abbotabad, Pakistan compound. The work of Tailored Access Operations, in installing spyware on phones is highlighted. Also highlighted are the roles of the CIA, other agencies, and the Navy SEALs.[335]
- The NSA's Network Analysis Center cracked the reservation system for Aeroflot, and also hacked Al Jazeera, accessing specially protected material, according to a document dated in 2006.[74]
- The NSA hacked the French Foreign Ministry, and bugged the French diplomatic offices in Washington and New York in 2010.[322]
- The NSA conducted extensive spying on Enrique Peña Nieto, and his aides, accessing their emails. Likewise, the NSA spied on the communications of Dilma Rousseff, and her aides, and also created a two hop contact graph. The source document is dated June 2012, it is unclear whether the operation is ongoing.[336][337][338]
- The NSA and GCHQ target banks and credit card companies by various means including "Tailored Access Operations", specifically by targeting printer traffic from banks. VISA has also been targeted. According to a GCHQ document, the collection involves "bulk data" containing "rich personal information" that is mostly "not about our targets".[321]
- From collection points outside the United States, the NSA gathers contact lists belonging to users of e-mail and instant messaging services, including Yahoo, Hotmail, Facebook and Gmail.[339]
NSA relationships with foreign intelligence services
- Payments to GCHQ from NSA totaling at least £100 million
- Relationships with Germany's BND, exchange of technology: (XKeyscore, and the German programs and bulk metadata (500 Million records in one month alone)).
- The US directly spies on most of its allies, even those with intelligence sharing agreements, with only the Five Eyes being immune.[300]
Suggested protective measures from surveillance
Encryption
In cryptography, encryption is the process of encoding information in such a way that eavesdroppers or hackers cannot read it, but that authorized parties can. According to Snowden's recommendations published by The Guardian Edward in September 2013,[340] properly implemented strong crypto systems were among the few things which one can rely on. However, endpoint security is often too weak to prevent the NSA from finding ways around it.[340]
Underground bunkers
In September 2013, it was reported by the press that a number of countries deemed by the US and its allies to be rogue states, such as Syria, Iran and North Korea, had successfully evaded U.S. government surveillance by constructing secret bunkers deep below the Earth's surface.[341]
China's underground megaproject, the 816 Nuclear Military Plant in Chongqing (now declassified and opened to tourists), was reported to be "most worrying" for the U.S. Defense Intelligence Agency.[341]
Libya evaded surveillance by building "hardened and buried" bunkers at least 40 feet below ground level.[341]
- In 2002, the NSA, in cooperation with the FBI, and in cooperation with Qwest, monitored nearly all communications in the Salt Lake area in the six months surrounding the Olympic games.[161][342][343]
- Since 2005, Canada has been running a bulk phone metadata, email and text message program.[344][345][346]
- The NYPD is engaging in mass surveillance, particularly of Muslims, in mosques, in social gatherings, and even at home. The department employs "rakers" to troll Muslim neighborhoods. The unit employing said rakers, was once called "The Demographics Unit," the name was changed in 2010 to the "Zone Assessment Unit" to mask the appearance, though not change the actual fact of racial profiling. Knowledge of this program was kept from the city council.[347]
- Devices made by the American company Blue Coat Systems, which are used for Internet surveillance and censorship, have turned up repeatedly in countries that censor and surveil the Internet, and have a record of human rights abuses, such as Iran, Syria, China, Burma (Myanmar) and Sudan.[348][349][350][351]
- The ACLU has released a report on the proliferation of license plate readers and on the retention of data from them.[352][353]
- The FBI has been pressuring ISPs to install surveillance software, referred to as the "harvesting program".[354]
- The FBI has been using malware and hacking to surveil suspects. Reports indicate however, that hacking and malware usage remains a last resort, and that warrants are sought for individual cases.[355][356]
- The NSA collects the contents of emails that transit from the US to abroad, and searches them for keywords.[357]
- The Post Office scans all envelopes, outsides of packages and postcards.[358]
- France's Equivalent of PRISM
- India will be building a mass domestic surveillance program called the "Central Monitoring System", which will be able to track all voice, fax, and text across all telephone networks in the country. It will also contract the Israeli company Verint Systems to monitor encrypted Gmail, BlackBerry, Skype and Yahoo! mail.[359][360]
- More than 230 thousand people were questioned under The United Kingdom's Schedule 7 of the Terrorism act of 2000 between April 2009 and March 2012.[361]
- New Zealand passed a bill allowing domestic spying against its citizens and residents, by a narrow margin (61–59).[362][363]
- Russ Tice, on June 19 gave an interview to Boiling Frogs Post, in which he expanded his previous disclosures. Specifically he names persons who had been wiretapped by the NSA, namely: Hillary Clinton, Barack Obama, Dianne Feinstein, Colin Powell, Evan Bayh, Samuel Alito and many others including journalists and political groups. He asserts that all telephony content is collected.[364]
- Blueprints of the Utah Data Center[365]
- "The Find," the NSA can locate cellphones even when they were turned off.[366]
- The DEA's and IRS's use of NSA data to start criminal investigations against US citizens, and their method of "Parallel Construction" to conceal the true origins of their evidence.[367][368]
- CIA operative De Sousa, convicted in absentia in Italy in the extraordinary rendition case of Osama Mustapha Hassan Nasr AKA Abu Omar goes on camera describing the case.[369]
- Insider Threat Program – policy requiring federal employees to report "high-risk persons or behaviors" from among co-workers, as well as to punish those who fail to report such colleagues.[370] In 2013, the NSA planned to investigate over 4000 cases.[88]
- The German Federal Office for Information Security has warned that Windows 8 has a built-in backdoor, that could allow Microsoft, and by extension the NSA to access many Windows 8 machines via the Trusted Platform Module that comes embedded on many Windows 8 machines.[371][372] Of the subset of CIA applicants whose backgrounds raised flags, one fifth were found to have ties to either terrorism or foreign hostile intelligence.[373]
- The NSA has admitted about a dozen cases of willful violations by analysts over the last 10 years.[374] One common form, in which an analyst spies on a love interest, has been dubbed "LOVEINT"[375]
- The Hemisphere Project, a secret partnership between federal and local drug officials and AT&T since September 2007. Law enforcement has access to electronic call detail records for any telephone carrier that uses an AT&T switch to process a telephone call. Records go back to 1987 and about 4 billion are added every day. Officials are instructed to obfuscate the existence of the program, by a method similar to "Parallel Construction" in which a separate subpoena is obtained for records which had already been returned by the Hemisphere project, thus disguising the true origin of the data.[376][377]
- Sweden is helping the GCHQ tap fiber-optic cables and has become, effectively, a member of the 'Five Eyes', according to Duncan Campbell in a hearing of the EU parliament's LIBE committee. He further states that the codename for the tapping operation is "Sardine" and is classified several levels above top secret, and that the information about Sweden was withheld from publication in the Guardian, The New York Times, and Pro Publica.[378][379][380]
- CIA, BND and the Federal Office for the Protection of the Constitution ran Projekt 6 (P6 for short) from 2005 to 2010. It's aim was to gather intelligence on suspected jihadists and terrorism supporters. An American query request for the internal database, code name PX contains the passport number, date of birth and name of German investigative journalist Peter Buchen.[381]
- The ACLU released a 69 page report on the FBI entitled "Unleashed and Unaccountable" detailing warrantless wiretapping, spying on political activists and journalists, biased training and racial profiling, proxy detentions in foreign countries, use of the no-fly list as a means of pressuring people to become informants, bulk data collection (eGuardian and bulk telephony metadata), dodging oversight and misleading the public.[382][383]
- The NSA purchases zero-day exploits from Vupen, as revealed in a FOIA request. In response, the CEO of Vupen suggested that a FOIA request also be made for Raytheon, Lockheed Martin and Northrop, because they also sell exploits.[384]
Fallout
Shortly after the disclosures were published, US President Barack Obama asserted that the American public had no cause for concern because "nobody is listening to your telephone calls",[385] and "there is no spying on Americans".[386]
On June 21, 2013, the Director of National Intelligence James R. Clapper issued an apology for giving false testimony under oath to the United States Congress, which is a felony under 18 USC s. 1001. Earlier in March that year, Clapper was asked by Senator Ron Wyden to clarify the alleged surveillance of U.S. citizens by the NSA:
Senator Wyden: "Does the NSA collect any type of data at all on millions or hundreds of millions of Americans?"
Director Clapper: "No, Sir."[387]
In an interview shortly after Snowden's disclosures were first published, Clapper stated that he had misunderstood Wyden's question and answered in what he thought was the "least untruthful manner".[388] Later, in his letter of apology, Clapper wrote that he had only focused on Section 702 of the Foreign Intelligence Surveillance Act during his testimony to Congress, and therefore, he "simply didn't think" about Section 215 of the Patriot Act, which justifies the mass collection of telephone data from U.S. citizens.[389] Clapper said: "My response was clearly erroneous—for which I apologize".[389]
To increase transparency and because it is in the public interest the Director of National Intelligence authorized the declassification and public release of the following documents pertaining to the collection of telephone metadata pursuant to Section 215 of the PATRIOT Act on July 31, 2013.[390] These documents were:
- Cover Letter and 2009 Report on the National Security Agency’s Bulk Collection Program for USA PATRIOT Act Reauthorization[391]
- Cover Letters and 2011 Report on the National Security Agency's Bulk Collection Program for USA PATRIOT Act Reauthorization[392]
- Primary Order for Business Records Collection Under Section 215 of the USA PATRIOT Act[393]
In a press conference on August 9, 2013 President Obama announced four steps to reform U.S. intelligence gathering measures, to increase transparency and restore public trust in surveillance by NSA, but made no indication to alter the NSA's ongoing mass collection of phone data and surveillance of internet communications in the short term.[394][395] These four steps are:[396][397][398]
- Reform Section 215 of the Patriot Act which allows the National Security Agency to collect telephone data from millions of communications without a warrant.[396]
- More transparency: Declassification of the legal rationale for the US government's phone-data collection,[317][399][400][401] release of NSA information that details its mission, authorities, and oversight,[316][317][402] installation of a "civil liberties and privacy officer" at the National Security and a website created by the American intelligence community to inform Americans and the world what the intelligence community does and what it doesn’t do, how it carries out its mission, and why it does so.[396]
- More balance between security and privacy at the Federal Intelligence Surveillance Court by appointing an adversarial voice – such as a lawyer assigned to advocate privacy rights[403] – to argue against the US government to ensure to make sure civil liberties concerns have an independent voice in appropriate cases.[396]
- Review of all US government intelligence and communications technologies by a group of external experts (composed of former intelligence officials, civil liberties and privacy advocates, and others)[403] which shall provide an interim report in 60 days and a final report by the end of 2014 outlining how the US government can maintain the trust of the people, how it can make sure that there absolutely is no abuse in terms of how surveillance technologies are used and how surveillance impacts US foreign policy.[396] Director of National Intelligence James R. Clapper has been directed on August 13, 2013 to form and review the new Review Group on Intelligence and Communications Technologies, which is to brief Obama on its interim findings within 60 days of the establishment of the group. A final report and recommendations are to be submitted through Clapper to the president no later than December 15, 2013.[402][404][405] The group's purpose is to assess whether the US "employs its technical collection capabilities in a manner that optimally protects our national security and advances our foreign policy while appropriately accounting for other policy considerations, such as the risk of unauthorized disclosure and our need to maintain the public trust."[406]
In a reaction to Obama above reform proposals responsible for overseeing the program which collects Americans’ telephone communications data in bulk say that they felt in recent years limited in their ability to challenge its scope and legality. They pointed out to intelligence officials who would not volunteer details if questions were not asked with absolute precision in regular meetings; hearing only from government officials steeped in the legal and national security arguments for aggressive spying; and House members must rely on the existing committee staff, many of whom used to work for the spy agencies they are tasked with overseeing, while Senate Intelligence Committee members can each designate a full-time staffer for the committee who has full access. Additional obstacles stemmed from the classified nature of documents, which lawmakers may read only in specific, secure offices; rules require them to leave their notes behind and restrict their ability to discuss the issues with colleagues, outside experts or their own staff.[407]
On August 12, 2013, President Obama announced the creation of an "independent" panel of "outside experts" to review the NSA's surveillance programs. The panel is due to be established by the Director of National Intelligence, James R. Clapper, who will consult and provide assistance to them.[408] The "independent" panel of "outside experts" is composed of intelligence insiders, former White House officials and Obama advisers, who did not discuss any changes to the National Security Agency's controversial activities at its first meeting.[409]
On July 19, 2013, Human Rights Watch sent a letter to the Obama administration, urging it to allow companies involved in the NSA's surveillance to report about these activities and to increase government transparency.[410]
On August 18, 2013, Amnesty International asserted that if journalists maintain their independence and report critically about governments, they too may be "targeted" by the British government.[411]
On August 20, 2013, Index on Censorship argued that the British government's "threat of legal action" against The Guardian was a "direct attack on press freedom in the UK".[412]
On September 4, 2013, U.N. Special Rapporteur Frank La Rue stressed that the "protection of national security secrets must never be used as an excuse to intimidate the press into silence."[413]
According to a survey undertaken by the human rights group PEN International, these disclosures have had a chilling effect on American writers. Fearing the risk of being targeted by government surveillance, 28% of PEN's American members have curbed their usage of social media, and 16% have self-censored themselves by avoiding controversial topics in their writings.[414][415]
Attempts to minimize perceived damage
- Press censorship: British government officials issued a confidential DA-Notice to several press organizations, with the aim of restricting their ability to report on these leaks.[416] According to the U.S. Army, its decision to block The Guardian website was based upon the need to prevent service personnel from accessing press coverage and online content related to these disclosures.[417]
- Detention without charge: On August 18, 2013, David Miranda, partner of journalist Glenn Greenwald, was detained under Schedule 7 of the United Kingdom's Terrorism Act of 2000. Miranda was returning from Berlin, carrying 58,000 GCHQ documents on a single computer file[418] to Greenwald in Brazil. Greenwald described Miranda's detention as "clearly intended to send a message of intimidation to those of us who have been reporting on the NSA and GCHQ".[419][420][421][422] The Metropolitan Police and Home Secretary Teresa May argued that Miranda's detention "legally and procedurally sound".[423] However, Lord Falconer of Thoroton, responsible for introducing the bill in the House of Lords, said that under the act, police can only detain someone "to assess whether they are involved in the commission, preparation or instigation of terrorism". He said "I am very clear that this does not apply, either on its terms or in its spirit, to Mr Miranda."[424] Antonio Patriota the Brazilian Minister of External Relations said that Miranda's detention was "not justifiable". The reasons for Miranda's detention were sought from the police by British politicians and David Anderson QC, the independent reviewer of terrorism legislation.[425] The United States government later said that British officials had given them a "heads up" about Miranda's detention, while adding that the decision to detain him had been a British one.[425]
- Destruction of evidence: Guardian editor Alan Rusbridger said the newspaper had received legal threats from the British government and was urged to surrender all documents leaked by Snowden. Security officials from the Government Communications Headquarters (GCHQ) later made a visit to the newspaper's London headquarters to ensure that all computer hard drives containing Snowden's documents were destroyed.[423][426]
- Editing of interview transcript: After the NSA Director of Compliance John Delong was interviewed by The Washington Post regarding these disclosures, the White House sent a "prepared" statement to The Post and ordered that "none of Delong's comments could be quoted on the record". The Post refused to comply.[427][428]
- Forced landing of Morales' plane: Five Latin American countries – Bolivia, Cuba, Ecuador, Nicaragua and Venezuela – voiced their concerns to the UN Secretary-General Ban Ki-Moon after the plane of Bolivia's President Evo Morales was denied entry by a number of western European countries, and was forced to reroute to Austria based on "suspicion that United States whistleblower Edward Snowden was on board".[429] Ban said it was important to prevent such incidents from occurring in the future and emphasized that "A Head of State and his or her aircraft enjoy immunity and inviolability".[429]
- Criminal investigation: Currently, a criminal investigation of these disclosures is being undertaken by Britain's Metropolitan Police Service.[12]
US Congress' attempts to limit NSA
In response to the information released by Snowden, Rep. Justin Amash (R-Mich.) and Rep. John Conyers (D-Mich.) proposed the "Amash-Coyers Amendment" to the National Defense Authorization Act.[430] If passed, the amendment would have curtailed "the ongoing dragnet collection and storage of the personal records of innocent Americans." The House rejected the amendment by a vote of 205–217.[431] An analysis indicated that those who voted against the amendment received 122% more in campaign contributions from defense contractors than those who voted in favor.[432] Template:List of votes on the Amash/Conyers Amendment
In September 2013, Senators Mark Udall, Richard Blumenthal, Rand Paul and Ron Wyden introduced a "sweeping surveillance reform" proposal.[433] Called the most comprehensive proposal to date, the "Intelligence Oversight and Surveillance Reform Act" seeks to end the bulk collection of communication records made legal in section 215 of the Patriot Act and to reign in other "electronic eavesdropping programs".[434] Wyden told the Guardian the Snowden disclosures have "caused a sea change in the way the public views the surveillance system". The draft bill is a blend of 12 similar proposals as well as other legislative proposals.[435]
At the end of October 2013 U.S. Senators introduced two different reform proposals. One, the USA Freedom Act (H.R. 3361/ S. 1599),[436][437][438] would effectively halt “bulk” records collection under the USA Patriot Act, while it also would require a warrant to deliberately search for the e-mail and phone call content of Americans that is collected as part of a surveillance program targeting foreigners located overseas. Another would preserve the program while strengthening privacy protections. It would also codifying the requirement that analysts have a “reasonable articulable suspicion” that a phone number is associated with terrorism to query the NSA phone records database; requiring that the FISA court promptly review each such determination; and limiting the retention period for phone records. Both proposals share the introduction of a special advocate to promote privacy interests before the FISA court.[439]
Impact on foreign relations
The media leaks caused tension in the bilateral relations of the United States with several of its allies and economic partners as well as in its relationship with the European Union:
Former Foreign Minister Bob Carr attacked the U.S. for allowing the leaks in the first place. Saying,"the United States would be critical of any other nation that failed to prevent the release of such material. Certainly if it had gone the other way, if there'd been some official in Canberra, some contractor in Canberra, who allowed a slew of material as sensitive as this to be plastered over the world's media, America would be saying very stern things to someone they'd be regarding as a woefully immature ally and partner."[440]
The Brazilian government expressed outrage at the revelations that the National Security Agency directly targeted the communications of president Dilma Rousseff and her top aides.[204] It called the incident an "unacceptable violation of sovereignty" and requested an immediate explanation from the U.S. government.[441]
Brazil's government signaled it would consider cancelling Rousseff's state visit to Washington – the only state visit for a foreign leader scheduled this year.[442] A senior Brazilian official stated the country would downgrade commercial ties unless Rousseff receives a public apology.[442] That would include ruling out the $4 billion purchase of Boeing F-18 Super Hornet fighters and cooperation on oil and biofuels technology, as well as other commercial agreements.[442]
According to Huang Chengqing, Director of China's Computer emergency response team, about 2.91 million mainframe computers in China have been hijacked by more than 4,000 servers based in the United States.[443] On June 17, 2013, two weeks after the first disclosure was published, a spokesman for the Chinese Foreign Ministry said:
"We believe the United States should pay attention to the international community's concerns and demands and give the international community the necessary explanation"[444]
On October 21, 2013, France summoned Charles Rivkin, the U.S. Ambassador to France, to clarify and explain the NSA's surveillance of French citizens.[445] Speaking to journalists in the French seaport of Lorient, President François Hollande said:
"We cannot accept this kind of behaviour between partners and allies...We ask that this immediately stop."[446]
According to the Wall Street Journal data allegedly collected by the NSA in France was actually collected by French intelligence agencies outside France and then shared with the United States.[258]

On July 1, 2013, the German Foreign Ministry summoned Philip D. Murphy, the U.S. Ambassador to Germany, over allegations that the NSA had spied on institutions of the European Union.[448] On October 24, 2013, the Foreign Ministry summoned John B. Emerson, the U.S. Ambassador to Germany, to clarify allegations that the NSA had tapped into Chancellor Angela Merkel’s mobile phone.[449][450]
In early August 2013, Germany canceled largely symbolic Cold War-era administrative agreements with Britain, the United States and France, which had granted the Western countries which had troops stationed in West Germany the right to request surveillance operations to protect those forces.[451]
Under the orders of the German domestic intelligence agency at the end of August 2013, a federal police helicopter conducted a low-altitude flyover of the United States Consulate in Frankfurt, apparently in search of suspected clandestine eavesdropping facilities. A German official called it a symbolic "shot across the bow."[452]
On November 1, 2013, the Foreign Ministry of Indonesia summoned Australia's Ambassador Greg Moriarty to explain his country's surveillance of President Susilo Bambang Yudhoyono and other Indonesian political leaders.[453]
On November 18, 2013, the Australian ambassador was summoned again by Indonesian government officials, who pledged to review all types of cooperation with Australia. The Indonesian Foreign Minister Marty Natalegawa called the spying "unacceptable", and added that "This is an unfriendly, unbecoming act between strategic partners." The Indonesian ambassador to Australia was also recalled as a response to the incident.[454]
Italy's Prime Minister Enrico Letta asked John Kerry, the U.S. Secretary of State, to clarify if the NSA had illegally intercepted telecommunications in Italy.[455] On October 23, 2013, the Italian Interior Minister Angelino Alfano told reporters in Rome:
"We have a duty to (provide) clarity to Italian citizens - we must obtain the whole truth and tell the whole truth, without regard for anyone."[456]
On November 2, 2013, the Malaysian Foreign Minister Anifah Aman summoned the ambassadors of Australia and the United States in protest against a vast US-led surveillance network in Asia.[457]
On October 24, 2013, the Mexican Foreign Minister José Antonio Meade Kuribreña met with U.S. Ambassador Earl Anthony Wayne to clarify surveillance details revealed by Snowden.[458]
On October 25, 2013, the Spanish Prime Minister Mariano Rajoy summoned James Costos, the U.S. Ambassador to Spain, to clarify reports about the NSA's surveillance of the Spanish government.[459] Spanish EU Minister, Inigo Mendez de Vigo, said such practices, if true, were "inappropriate and unacceptable". An EU delegation was to meet officials in Washington to convey their concerns.[460] According to the Wall Street Journal data allegedly collected by the NSA in Spain was actually collected by Spanish intelligence agencies outside Spain and then shared with the United States.[258] This was confirmed by National Security Agency director Keith Alexander on October 29, 2013, when he said foreign intelligence services collected phone records in war zones and other areas outside their borders and provided them to the NSA.[259]
Early July 2013, the European Commissioner for Home Affairs, Cecilia Malmström, wrote to 2 US officials that "mutual trust and confidence have been seriously eroded and I expect the U.S. to do all that it can to restore them".[461]
On October 20, 2013, a committee at the European Parliament backed a measure that, if enacted, would require American companies to seek clearance from European officials before complying with United States warrants seeking private data. The legislation has been under consideration for two years. The vote is part of efforts in Europe to shield citizens from online surveillance in the wake of revelations about a far-reaching spying program by NSA.[462]
The European Council meeting at the end of October 2013 in its statement signed by all 28 EU leaders while stressing that "intelligence gathering is a vital element in the fight against terrorism" and noting "the close relationship between Europe and the USA and the value of that partnership", said that this must "be based on respect and trust," a lack of which "could prejudice the necessary cooperation in the field of intelligence gathering".[463][464]
Impact on trade
Late October 2013 There has been a notable dropoff of computer hardware and analytic software in the Chinese market. [2] This has been highly attributed to the Snowden document releases, not market saturation or downticks.
Perceived consequences for counter-terrorism and national security
Late June 2013, Keith B. Alexander, the director of the NSA, asserted that these media leaks had caused "significant" and "irreversible" damage to the national security of the United States and this "irresponsible" release of classified information will have a "long-term detrimental" impact on the intelligence community's ability to detect future attacks. Furthermore, these leaks have "inflamed and sensationalized" the work that the intelligence community does lawfully under "strict oversight and compliance".[465]
In early October 2013, former GCHQ director Sir David Omand, speaking of how useful for Russia's intelligence services Snowden's stay in Russia could be, told the BBC: "Part of me says that not even the KGB in its heyday of Philby, Burgess and Maclean in the 1950s could have dreamt of acquiring 58,000 highly classified intelligence documents."[466] Snowden stated that he had not leaked any documents to Russia.[467]
Andrew Parker, the director general of the UK Security Service maintained in October 2013 that the exposing of intelligence techniques had given extremists the ability to evade the intelligence agencies; he said,"It causes enormous damage to make public the reach and limits of GCHQ techniques. Such information hands the advantage to the terrorists. It is the gift they need to evade us and strike at will."[468]
Shortly afterwards, The Financial Times editorialised that security chiefs were "right to be alarmed, knowing that terrorists can change their modus operandi in response to new information on their capabilities" and there was "no firm evidence that the intelligence agencies are using these new collection capabilities for malign ends."[418]
Reaction
United States of America
Executive branch
In early June 2013, the U.S. Director of National Intelligence, James R. Clapper, referring to the surveillance activities reported in The Washington Post and Guardian shortly prior, stressed that those were lawful and conducted under authorities approved by the US Congress and that "significant misimpressions" had resulted from those articles; he called the disclosures of "intelligence community measures used to keep Americans safe" "reckless".[469] He condemned the leaks as having done "huge, grave damage" to the U.S. intelligence capabilities.[470] The NSA formally requested that the Department of Justice launch a criminal investigation into Snowden's actions.[469]
On June 14, 2013, US federal prosecutors filed a sealed complaint, made public on June 21,[471] charging Snowden with theft of government property, unauthorized communication of national defense information, and willful communication of classified intelligence to an unauthorized person; the latter two charges being under the Espionage Act.[6]
In June 2013, the U.S. military blocked access to parts of the Guardian website related to government surveillance programs for thousands of defense personnel across the country, and to the entire Guardian website for personnel stationed in Afghanistan, the Middle East, and South Asia.[472][473] A spokesperson described the filtering as a routine "network hygiene" measure intended to mitigate unauthorized disclosures of classified information onto the Department of Defense's [DOD] unclassified networks.[472]
On Sunday, August 4, Chairman of the Joint Chiefs of Staff Martin Dempsey was shown on the weekly ABC interview show This Week saying that Snowden "has caused us some considerable damage to our intelligence architecture. Our adversaries are changing the way that they communicate."[474]
United States President Barack Obama was dismissive of Snowden in late June, saying, "I'm not going to be scrambling jets to get a 29-year-old hacker."[475][476] In early August, Obama said that Snowden was no patriot and that Americans would have been better off if they had remained unaware of the NSA surveillance activities that Snowden revealed.[477] Obama also said that he had "called for a thorough review of our surveillance operations before Mr. Snowden made these leaks.... My preference, and I think the American people's preference, would have been for a lawful, orderly examination of these laws; a thoughtful fact-based debate that would then lead us to a better place."[477] On August 9, Obama announced that he was ordering Director of National Intelligence James Clapper to arrange for "a high-level group of outside experts to review our entire intelligence and communications technologies.”[478][479] Director of National Intelligence James Clapper acknowledged that Snowden may have done a public service and started a needed debate about the balance between privacy and security. “As loath as I am to give any credit for what’s happened here, which was egregious, I think it’s clear that some of the conversations that this has generated, some of the debate, actually probably needed to happen,” he said, “It’s unfortunate they didn’t happen some time ago, but if there’s a good side to this, that’s it.”[480][481]
Congress
Reactions to Snowden's disclosures among members of Congress initially were largely negative.[482] Speaker of the House John Boehner[483] and senators Dianne Feinstein[484] and Bill Nelson[485] called Snowden a traitor, and several senators and representatives joined them in calling for Snowden's arrest and prosecution.[484][486][487]
Representative Thomas Massie was one of few members of Congress to question the constitutional validity of the government surveillance programs and suggest that Snowden should be granted immunity from prosecution.[488] Senators Ted Cruz[489] and Rand Paul[490] offered tentative support for Snowden, saying they were reserving judgment on Snowden until more information about the surveillance programs and about Snowden's motives were known. Senator Paul said, "I do think when history looks at this, they are going to contrast the behavior of James Clapper, our National Intelligence Director, with Edward Snowden. Mr. Clapper lied in Congress in defiance of the law, in the name of security. Mr. Snowden told the truth in the name of privacy."[491] Paul later called Snowden a "civil disobedient", like Martin Luther King Jr., but who faced life imprisonment.[492] Representative John Lewis made comparisons between Snowden and Gandhi, saying the leaker was appealing to a "higher law".[493]
Senator Bill Nelson, "What Edward Snowden did amounts to an act of treason."[494] Similar comments have also been made by Rep. Peter T. King, Rep. John Boehner, and Sen. Dianne Feinstein.[495]
On July 25, the US Senate Committee on Appropriations unanimously adopted an amendment by Senator Lindsey Graham to the "Fiscal Year 2014 Department of State, Foreign Operations, and Related Programs Appropriations Bill"[496] that would seek sanctions against any country that offers asylum to Snowden.[497][498][499]
In response to the information release by Snowden, Rep. Justin Amash (R-Mich.) and Rep. John Conyers (D-Mich.) proposed an amendment to the National Defense Authorization Act[500] to curtail the NSA gathering and storage of the personal records, but the House rejected it by a narrow margin of 205–217.[501] Amash subsequently told Fox News that Snowden was "a whistle-blower. He told us what we need to know."[502]
On the Sunday ABC interview show This Week, Rep. Dutch Ruppersberger, D-Maryland, of the United States House Select Committee on Intelligence was asked by Raddatz, "Are efforts being thwarted in trying to get information for members of Congress?" He replied,
"...[S]ince this incident occurred with Snowden, we've had three different hearings for members of our Democratic Caucus, and the Republican Caucus, where General Alexander has come with his deputy, Chris Inglis, to ask any questions that people have as it relates to this information. And we will continue to do that because what we're trying to do now is to get the American public to know more about what's going on....But we can do better. I have to educate my caucus more, the Democratic Caucus. And we're trying to declassify as much as we can."[503]
U.S. Senator John McCain (R-AZ) said on the August 11 edition of Fox News Sunday that Snowden had become a hero to young Americans, as he reminded them of the Jason Bourne character. McCain attributed it to generation change and a lack of confidence in the federal government. "Right now there's kind of a generational change," he said. "Young Americans do not trust this government."[504]
Gordon Humphrey, the conservative Republican senator for New Hampshire from 1979–1991, expressed support for Snowden.[505] Glenn Greenwald revealed that Humphrey, a former member of the Senate Foreign Relations Committee, had been in contact with Snowden via email. Humphrey told Snowden, "Provided you have not leaked information that would put in harms way any intelligence agent, I believe you have done the right thing in exposing what I regard as massive violation of the United States Constitution."[506] Humphrey cited Snowden as a "courageous whistle-blower".[507]
Tom McClintock (R-Calif) came out in favor of amnesty for Snowden, saying "I think it would be best if the American government granted him amnesty to get him back to America where he can answer questions without the threat of prosecution... We have some very good laws against sharing secrets and he broke those laws. On the other hand, he broke them for a very good reason because those laws were being used in direct contravention of our 4th Amendment rights as Americans."[508]
Public
Initial polls conducted by news organisations following Snowden's disclosures about government surveillance programs to the press indicated that American public opinion on Snowden's actions was divided. A Gallup poll conducted June 10–11, 2013 showed 44 percent of Americans thought it was right for Snowden to share the information with the press while 42 percent thought it was wrong.[509] A USA Today/Pew Research poll conducted June 12–16 found that 49 percent thought the release of information served the public interest while 44 percent thought it harmed it. The same poll found that 54 percent felt a criminal case should be brought against Snowden, while 38 percent thought one should not be brought,[510][511] while a Washington Post/ABC News poll conducted between the same dates as the Pew poll cited 43 percent of respondents saying Snowden ought to be charged with a crime, while 48 percent said he ought not.[512] Another poll in early July found 38 percent of Americans thought he did the wrong thing, 33 percent said he did the right thing, and 29 percent were unsure.[513] A WSJ/NBC poll conducted July 17–21 found that 11% of Americans viewed Snowden positively while 34% had a negative view.[514] A Quinnipiac University Polling Institute poll conducted June 28 – July 8 found that in the wake of Snowden's disclosures, more Americans said that government goes too far in restricting civil liberties as part of the war on terrorism (45 percent) than said that government does not go far enough to adequately protect the country (40 percent).[515] That finding was evidence of a massive swing in public opinion since an earlier Quinnipiac poll, conducted in 2010, when only 25 percent of respondents had said government goes too far in restricting civil liberties while 63 percent had said government does not go far enough. The same poll found that 55 percent of Americans regarded Snowden as a whistleblower while 34 percent saw him as a traitor.[515] Quinnipiac showed that a majority of Americans, by a wide margin, still regarded Snowden as a whistleblower rather than a traitor when it repeated the poll July 31 – August 1.[516]
After the June 2013 release, mass protests against government surveillance were reported in many parts of the world. In the United States, a political movement known as "Restore the Fourth" was formed and it gained momentum rapidly. In early July, Restore the Fourth was responsible for protests in more than 80 cities including Seattle, San Francisco, Denver, Chicago, Los Angeles and New York City. These protests were loosely coordinated via online messaging services and involved protestors from all over the United States.[517] Towards the end of July, it was reported in the media that the German intelligence agency BND had been actively cooperating with the NSA, which sparked demonstrations in 40 German cities involving thousands of protestors all over the country.[518]
Glenn Greenwald, one of the journalists who received the documents, praised Snowden for having done a service by revealing the surveillance on the American public.[519][520] John Cassidy, also of The New Yorker, called Snowden "a hero", and said that "in revealing the colossal scale of the US government's eavesdropping on Americans and other people around the world, [Snowden] has performed a great public service that more than outweighs any breach of trust he may have committed."[521] CNN columnist Douglas Rushkoff also called Snowden's leak an act of heroism.[522] Amy Davidson, writing in The New Yorker, was thankful for the "overdue" conversation on privacy and the limits of domestic surveillance.[523]
American political commentators and public figures such as Noam Chomsky,[524] Chris Hedges,[525] Michael Moore,[526] Cornel West,[527] Glenn Beck,[526] Matt Drudge,[528] Alex Jones,[529] Andrew Napolitano,[530] Oliver Stone,[531] Michael Savage,[532] and Stephen Walt[533] praised Snowden for exposing secret government surveillance.
Other commentators were more critical of Snowden's methods and motivations.[534] Jeffrey Toobin, for example, denounced Snowden as "a grandiose narcissist who deserves to be in prison."[535] Writing in the The New Yorker, Toobin argued that the programs exposed were not illegal, therefore Snowden was not a whistleblower. Further, Toobin questioned "whether the government can function when all of its employees (and contractors) can take it upon themselves to sabotage the programs they don’t like".[535]
Former Vice President Dick Cheney, suggested in June 2013 that Snowden might be a spy working for the Chinese government.[536]
Stewart Baker, a former NSA general counsel in the early 1990s, said at a July 18, 2013 hearing, "I am afraid that hyped and distorted press reports orchestrated by Edward Snowden and his allies may cause us – or other nations – to construct new restraints on our intelligence gathering, restraints that will leave us vulnerable to another security disaster."[537]
Former CIA and NSA chief General Michael Hayden in late June 2013 welcomed the public debate about the balance between privacy and security that the leaks had provoked: "I am convinced the more the American people know exactly what it is we are doing in this balance between privacy and security, the more they know the more comfortable they will feel."[538][539] In September 2013, Hayden stressed the indisputable legality of "what the NSA is doing" and called Snowden a "troubled young man", albeit "morally arrogant to a tremendous degree"; he also said about his prospects in Russia: "I suspect he will end up like most of the rest of the defectors who went to the old Soviet Union: Isolated, bored, lonely, depressed -- and most of them ended up alcoholics."[540]
Some former U.S. intelligence officials speculated that Chinese or Russian intelligence agents might have gleaned additional classified material from Snowden,[541][542][543] a view shared by some former Russian agents.[544] Snowden, however, told Greenwald in July that "I never gave any information to either government, and they never took anything from my laptops."[545]
In late June 2013, Former US President Jimmy Carter said: "He's obviously violated the laws of America, for which he's responsible, but I think the invasion of human rights and American privacy has gone too far ... I think that the secrecy that has been surrounding this invasion of privacy has been excessive, so I think that the bringing of it to the public notice has probably been, in the long term, beneficial."[546]

The editors of Bloomberg News argued that, while the government ought to prosecute Snowden, the media's focus on Snowden took attention away from issues of U.S. government surveillance, the interpretations of the Patriot Act, and the Foreign Intelligence Surveillance Act (FISA) court actions, all of which are "what really matters in all this."[547] Greenwald accused the media in the U.S. of focusing on Edward Snowden instead of on wrongdoing by Clapper and other U.S. officials.[548] In an op-ed, author Alex Berenson argued that the federal government should have flown a representative to Hong Kong to ask Snowden to give testimony in front of the U.S. Congress and offer him a fair criminal trial, with a view to preventing further unintended disclosures of classified information to other countries.[549]
On June 9, a We the People petition was launched on the whitehouse.gov website to seek "a full, free, and absolute pardon for any crimes [Snowden] has committed or may have committed related to blowing the whistle on secret NSA surveillance programs". The petition attained 100,000 signatures within two weeks, thus meeting the threshold and requiring an official response from the White House.[550] In October 2013, the Administration still had not responded to the petition, but gave no excuse for the four month delay.[551][552]
On August 8, 2013, Lavabit, a Texas-based secure email service provider reportedly used by Snowden, abruptly announced it was shutting down operations after nearly 10 years of business.[553] The owner, Ladar Levison, posted a statement online saying he would rather go out of business than "become complicit in crimes against the American people."[553] He also said that he was barred by law from disclosing what he had experienced over the preceding 6 weeks, and that he was appealing the case in the U.S. Fourth Circuit Court of Appeals.[553] Multiple sources speculated that the timing of the statement suggested that Lavabit had been targeted by the US government in its pursuit of information about Snowden.[553][554][555][556][557] The following day, a similar email service, Silent Circle, preemptively shut down in order to "prevent spying".[558] Snowden said about the Lavabit closure, "Ladar Levison and his team suspended the operations of their 10-year old business rather than violate the Constitutional rights of their roughly 400,000 users. The President, Congress, and the Courts have forgotten that the costs of bad policy are always borne by ordinary citizens, and it is our job to remind them that there are limits to what we will pay." He said that "internet titans" like Google should ask themselves why they weren't "fighting for our interests the same way small businesses are".[559]

An opinion poll carried out by Emnid at the end of June 2013 revealed that 50% of Germans consider Snowden a hero, and 35% would hide him in their homes.[560] Jürgen Trittin, a German Green politician, declared the following month that "Edward Snowden has done us all a great service. The man who revealed that our US and UK allies are spying on us ought to be given refuge by an EU country. [...] If ever a case demonstrated why we need the protection of whistleblowers, this is it."[561] In October 2013, another 50 high-profile Germans wrote to Der Spiegel declaring their support for any German offer to grant Snowden asylum.[562]
A poll of UK public opinion in October 2013 found that Britons generally regarded Snowden as a "hero", with 60% supportive of his actions.[563]
"Stop Watching Us" rally

On October 26, 2013, an anti-NSA rally called "Stop Watching Us" was held in Washington, DC,[564] billed by organizers as the "largest rally yet to protest mass surveillance". A diverse coalition of over 100 advocacy groups organized the event and attracted thousands of protestors calling for an end to the mass surveillance made public by Edward Snowden.[565] According to the Guardian, the most popular sign was printed with the words "Thank you, Edward Snowden". In a statement written by Snowden and read to the crowd by Jesselyn Radack, Snowden said, "This isn't about red or blue party lines, and it definitely isn't about terrorism. It's about being able to live in a free and open society...elections are coming up, and we are watching you", adding that elected officials should be "public servants, not private investigators." Other speakers included former governor Gary Johnson and NSA whistleblower Thomas Drake, who said to the crowd,"It's time to roll back the surveillance state...It is time for the US government to stop watching us".[566][567] Protests also took place in Germany.[568]
The rally was held on the 12th anniversary of the Patriot Act, which protesters see as the beginning of the mass surveillance of American citizens. The "Stop Watching Us" website states[569] that it demands reform of "Section 215 of the USA PATRIOT Act, the state secrets privilege, and the FISA Amendments Act to make clear that blanket surveillance of the Internet activity and phone records of any person residing in the US is prohibited by law and that violations can be reviewed in adversarial proceedings before a public court." It also calls for an investigation into the extent of domestic spying, and asks that officials found violating the constitution be brought to justice.[570]
Europe
Governments
- EU
In the European Parliament, the Greens–European Free Alliance and European United Left–Nordic Green Left nominated Snowden for the 2013 Sakharov Prize for Freedom of Thought, which includes €50,000.[571][572]
- Germany
Documents from Snowden show that cooperation between Berlin and Washington in the area of digital surveillance and defense intensified considerably during time of Chancellor Merkel. The Bundesnachrichtendienst (BND), the foreign intelligence agency of Germany, is directly subordinated to the Chancellor's Office. Although Merkel denied knowing about surveillance, Germans take the claims seriously. According to Hansjörg Geiger, former head of the BND, findings/claims are Orwellian and mutual political and economic espionage would be explicitly forbidden.[573]
- UK
British Foreign Minister William Hague admitted that Britain's GCHQ was also spying and collaborating with the NSA, and defended the two agencies' actions as "indispensable."[574][575][576] Meanwhile, UK Defence officials issued a confidential DA-Notice to British media asking for restraint in running further stories related to surveillance leaks including the PRISM programme and the British involvement therein.[577] British Prime Minister David Cameron issued a veiled threat to resort to prior restraint, through high court injunctions and DA-Notices, if the Guardian did not obey his demands to stop reporting its revelations on spying by GCHQ and the NSA,[578] a development that "alarmed" the Committee to Protect Journalists[579] and that spurred 70 of the world's leading human rights organisation to write an open letter to the newspaper expressing their concern about press and other freedoms in the UK.[580][581]
Non-government organizations

After Amnesty International met Edward Snowden in Moscow in mid July 2013, the organization said:
"What he has disclosed is patently in the public interest and as a whistleblower his actions were justified. He has exposed unlawful sweeping surveillance programmes that unquestionably interfere with an individual’s right to privacy. States that attempt to stop a person from revealing such unlawful behaviour are flouting international law. Freedom of expression is a fundamental right."[583]
Widney Brown, Senior Director of Amnesty, feared that Snowden would be at "great risk" of human rights violations if forcibly transferred to the United States,[584] and urged no country to return Snowden to the US. Michael Bochenek, Director of Law and Policy at Amnesty International deplored the US pressure on governments to block Snowden's asylum attempts, saying "It is his unassailable right, enshrined in international law".[585]
Human Rights Watch said that if Snowden were able to raise the issue of NSA mass surveillance without facing espionage charges, he would not have left the United States in the first place.[586] Human Rights Watch writes that any country where Snowden seeks asylum should consider his claim fairly and protect his rights under international law, which recognizes that revealing official secrets is sometimes justified in the public interest.[587]
Index on Censorship condemned the U.S. government for its "mass surveillance of citizens’ private communications" and urged all government officials to uphold the First Amendment to the United States Constitution. A statement released by Index on Censorship said: "Whistleblowers such as Edward Snowden — as well as journalists reporting on the Prism scandal, who have come under fire — should be protected under the first amendment, not criminalised."[588]
Navi Pillay, the United Nations High Commissioner for Human Rights, said: "Snowden's case has shown the need to protect persons disclosing information on matters that have implications for human rights, as well as the importance of ensuring respect for the right to privacy".[582]
Transparency International, International Association of Lawyers against Nuclear Arms and Vereinigung Deutscher Wissenschaftler awarded Snowden the German Whistleblowerpreis 2013.[589]
The Humanist Union awarded him the Fritz Bauer Prize 2013.[590]
China and Hong Kong
The South China Morning Post published a poll of Hong Kong residents conducted while Snowden was still in Hong Kong that showed that half of the 509 respondents believed the Chinese government should not surrender Snowden to the United States if Washington raises such a request; 33 percent of those polled think of Snowden as a hero, 12.8 percent described him as a traitor, 23 percent described him as "something in between."[591]
Referring to Snowden's presence in the territory, Hong Kong chief executive Leung Chun-Ying assured that the government would "handle the case of Mr Snowden in accordance with the laws and established procedures of Hong Kong [and] follow up on any incidents related to the privacy or other rights of the institutions or people in Hong Kong being violated."[592] Pan-democrat legislators Gary Fan and Claudia Mo said that the perceived U.S. prosecution against Snowden will set "a dangerous precedent and will likely be used to justify similar actions" by authoritarian governments.[593] During Snowden's stay, the two main political groups, the pan-democrats and Pro-Beijing camp, found rare agreement to support Snowden.[594][595] The pro-Beijing DAB party even organised a separate march to Government headquarters for Snowden.
The People's Daily and the Global Times editorials of June 19 stated respectively that the central Chinese government was unwilling to be involved in a "mess" caused by others, and that the Hong Kong government should follow the public opinion and not concern itself with Sino-US relations.[596] A Tsinghua University communications studies specialist, Liu Jianming, interpreted that the two articles as suggesting that the mainland government did not want further involvement in the case and that the Hong Kong government should handle it independently.[596]
After Snowden left Hong Kong, Chinese-language newspapers such as the Ming Pao and the Oriental Daily expressed relief that Hong Kong no longer had to shoulder the burden of the Snowden situation.[597] Mainland experts said that, although the Central Government did not want to appear to be intervening in the matter, it was inconceivable that the Hong Kong government acted independently in a matter that could have far-reaching consequences for Sino-US relations. One expert suggested that, by doing so, China had "returned the favor" for their not having accepted the asylum plea from Wang Lijun in February 2012.[598] The official Chinese Communist Party mouthpiece, the People's Daily denied the US government accusation that the PRC central government had allowed Snowden to escape, and said that Snowden helped in "tearing off Washington's sanctimonious mask."[599]
South America
Robert Menendez, chairman of the United States foreign relations panel, warned Ecuador that accepting Snowden "would severely jeopardize" preferential trade access the United States provides to Ecuador.[600] Ecuador's President Rafael Correa responded by abdicating US trade benefits.[601] A government spokesman said that Ecuador would offer the US "economic aid of US$23 million annually, similar to what we received with the trade benefits, with the intention of providing education about human rights."[602]
Correa criticized the US media for centering its focus on Snowden and countries supporting him, instead of focusing on the global and domestic privacy issues implicated in the leaked documents.[603]
After Bolivian president Morales' plane was, reacting to a false tip that Snowden was on board, denied access to Spanish, French, and Italian airspace during a return flight from Moscow, the presidents of Uruguay, Argentina, Venezuela and Suriname joined Correa and a representative from Brazil, in Cochabamba, Bolivia to discuss the incident.[604] Presidents Nicolás Maduro of Venezuela and Daniel Ortega of Nicaragua offered Snowden asylum after the meeting.
Brazil

In September 2013, Brazil's Chamber of Deputies Foreign Relations Committee decided to send a representative to speak to Edward Snowden about the espionage activities of the NSA in Brazil.[605] Petrobras announced that it was investing R$21 billion over five years to improve its data security.[606]
United Nations
Secretary General Ban Ki-moon said that "the Snowden case is something I consider to be misuse" and that digital communications should not be "misused in such a way as Snowden did."[607] Birgitta Jónsdóttir, an Icelandic legislator, criticized Ban for expressing a personal view while speaking in an official capacity. She said that Ban "seemed entirely unconcerned about the invasion of privacy by governments around the world, and only concerned about how whistleblowers are misusing the system."[607]
Other countries
Russia, Turkey and South Africa reacted angrily after it was revealed that their diplomats had been spied on during the 2009 G-20 London summit.[608]
Whistleblowers
Daniel Ellsberg, the whistleblower and leaker of the top-secret Pentagon Papers in 1971, stated in an interview with CNN that he thought Snowden had done an "incalculable" service to his country and that his leaks might prevent the United States from becoming a surveillance state. He said Snowden had acted with the same sort of courage and patriotism as a soldier in battle.[609] In an op-ed the following morning, Ellsberg added that "there has not been in American history a more important leak than Edward Snowden's release of NSA material ... including the Pentagon Papers."[610] Ray McGovern, a retired CIA officer turned political activist, agreed with Ellsberg and added, "This time today I'm feeling much more hopeful for our democracy than I was feeling this time yesterday."[611]
William Binney, a whistleblower who disclosed details of the NSA's mass surveillance activities, said that Snowden had "performed a really great public service to begin with by exposing these programs and making the government in a sense publicly accountable for what they're doing." After Snowden cited a conversation with a "reliable source" about allegations that the US was "hacking into China", Binney felt he was "transitioning from whistle-blower to a traitor."[612]
Thomas Drake, former senior executive of NSA and whistleblower, said that he feels "extraordinary kinship" with Snowden. "What he did was a magnificent act of civil disobedience. He's exposing the inner workings of the surveillance state. And it's in the public interest. It truly is."[612][613]
WikiLeaks founder Julian Assange hailed Snowden as a "hero" who has exposed "one of the most serious events of the decade – the creeping formulation of a mass surveillance state."[614] After charges against Snowden were revealed, Assange released a statement asking people to "step forward and stand with" Snowden.[615] Following President Obama's assurances that changes are planned for the NSA surveillance program, Assange said in a written statement that Obama had "validated Edward Snowden's role as a whistle-blower".[616][617]
Shamai Leibowitz, who leaked details about an FBI operation, said that the legal threats and "smear campaign" against Snowden are a "grave mistake" because "If the government really wanted to keep more secrets from coming out, they would do well to let this man of conscience go live his life in some other country."[618]
In October 2013, four US whistleblowers and activists visited Moscow to present Snowden with an award for truth-telling titled The Sam Adams Award for Integrity in Intelligence.[619][620] Thomas Drake, one of the presenters, told reporters after the event that the US had "unchained itself from their own constitution" by banning the "real law and [using] a secret law and secret interpretations of law." He further explained that Snowden "had to escape the US to ensure any chance of freedom", claiming the US had made Snowden stateless by revoking his passport while in Russia, leading to his temporary asylum in the country. Drake praised Russia, saying it had "actually recognized the international law and granted him political asylum".[621]
List of Americans under surveillance
In September 2013, names of prominent figures in the United States were released to public following an Interagency Security Classification Appeals Panel-mandated declassification by the NSA of relevant documents, and in response to an appeal by the National Security Archive at George Washington University.[624]
Activists
- Martin Luther King, Jr, a leader of the African-American Civil Rights Movement, was subjected to NSA surveillance right up until the day of his assassination.[624]
Celebrities
- Muhammad Ali, a former heavyweight boxing champion, was targeted by Project MINARET of the NSA, according to documents declassified in September 2013.[624]
Journalists
- Art Buchwald, a columnist for The Washington Post, was nominated by the FBI to be placed under NSA surveillance, according to documents declassified in September 2013[624]
- Tom Wicker, a columnist for The New York Times, was among those included in the Enemies List of the White House[624]
Members of Congress
- Frank Church, a U.S. Senator from Idaho, was placed on the NSA watch list because of his "irresponsible" political views and criticism of the Vietnam War.[624]
- Howard Baker, a Senate Majority Leader from Tennessee, was placed on the NSA watch list, according to documents declassified in September 2013[624]
-
Court order demanding that Verizon hand over all metadata to NSA.
-
Procedures used to target Foreigners.
-
Procedures used to Minimize collection on US persons.
-
2009 OIG Draft Report on Stellar Wind.
-
2007 Memos by Michael Mukasey requesting Broader powers.
-
Presidential Policy Directive – PPD 20 Signed By Barack Obama Relating to Cyberwarfare
-
NSA report on privacy violations.
-
What's a 'privacy violation'
-
FISA Court finds NSA surveillance "deficient on statutory and constitutional grounds" but nonetheless recertifies it.
-
Targeting Rationale Guidelines
-
Extracts of FY 2013 Intelligence Budget, volume 1
-
FY 2013 Intelligence Budget, additional tables
-
SilverZephyr Slide
-
Dropmire Slide.
-
Documents relating to spying on the 2009 G20 SummitDocuments relating to spying on the 2009 G20 Summit
-
Cover page of the PRISM presentation.
-
Map of global internet bandwidth.
-
Names of the PRISM content providers and which services they typically provide.
-
Dates each content provider joined PRISM.
-
Flowchart of the PRISM tasking process.
-
PRISM dataflow.
-
Explanation of PRISM case names.
-
REPRISMFISA web application.
-
Upstream and PRISM.Upstream and PRISM.
-
A week in the life of Prism
-
A 2008 Presentation of the XKeyscore program. (PDF, 27.26 MB)
-
Geopolititical Trends: Key Challenges
-
Geopolitical trends: Global Drivers
-
Benefits of contact graph analysis.
-
Benefits of contact graph analysis.
-
Contact graph.
-
Hops in a contact graph.
-
2 hop contact graph.
-
Spying against Enrique Peña Nieto and his associates.
-
Details of the process in the Nieto operation.
-
Emails from Nieto detailing potential cabinet picks.
-
Spying effort against Dilma Rousseff and her advisers.
-
Details of the process in the Rousseff operation (2 hop contact graph)
-
Details of the process in the Rousseff operation (2 hop contact graph)
-
Benefits of contact graph analysis.
-
Exploitation of Common Internet Encryption Technologies.
Comparison with previous leaks
| Year | Disclosure | Size | Main Source(s) | Major publisher(s) |
|---|---|---|---|---|
| 2013 | Mass surveillance disclosures | 15,000 – 20,000 documents | Edward Snowden | The Guardian, The New York Times, The Washington Post, Der Spiegel, Le Monde, |
| 2010 | United States diplomatic cables leak | 251,287 diplomatic cables | Chelsea Manning | The Guardian, The New York Times. Der Spiegel, Le Monde, El Pais, Wikileaks |
| 1971 | Pentagon Papers | 4,100 pages | Daniel Ellsberg | The New York Times |
See also
- 2013 Department of Justice investigations of reporters
- Terrorist Finance Tracking Program
- Top Secret America
References
- ^ Greenwald, Glenn. "NSA collecting phone records of millions of Verizon customers daily". The Guardian. Retrieved August 16, 2013.
Exclusive: Top secret court order requiring Verizon to hand over all call data shows scale of domestic surveillance under Obama
- ^ "USA must not persecute whistleblower Edward Snowden". Amnesty International. Retrieved August 16, 2013.
- ^ "US: Statement on Protection of Whistleblowers in Security Sector". Human Rights Watch. Retrieved August 16, 2013.
- ^ Transparency International Germany. "Transparency International Germany: Whistleblower Prize 2013 for Edward Snowden". Transparency International. Retrieved August 16, 2013.
- ^ "US needs to protect whistleblowers and journalists". Index on Censorship. Retrieved August 16, 2013.
- ^ a b U.S. vs. Edward J. Snowden criminal complaint. The Washington Post.
- ^ http://www.nytimes.com/2013/07/17/world/europe/snowden-submits-application-for-asylum-in-russia.html?_r=0
- ^ Snowden Asylum Hits U.S.-Russia Relations
- ^ U.S. 'Extremely Disappointed' At Russia's Asylum For Snowden
- ^ Henderson. "Obama To Leno: 'There Is No Spying On Americans'". NPR. Retrieved August 16, 2013.
- ^ Francis Elliott. "Cameron hints at action to stop security leaks". The Times. Retrieved November 13, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b RAPHAEL SATTER. "UK Pursuing Criminal Investigation Into NSA Leaks". ABC News. Retrieved November 13, 2013.
- ^ a b "New Details Emerge From the Einstein Files; How the F.B.I. Tracked His Phone Calls and His Trash". The New York Times. Retrieved September 17, 2013.
{{cite news}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Cauley, Leslie. "NSA has massive database of Americans' phone calls". "USA Today".
- ^ "Ex-CIA employee source of leak on PRISM program". France 24. Retrieved September 17, 2013.
Snowden's decision to reveal his identity and whereabouts lifts the lid on one of the biggest security leaks in US history and escalates a story that has placed a bright light on Obama's extensive use of secret surveillance.
- ^ a b Fiddler, Stephen (July 1, 2013). Echoes of Echelon in Charges of NSA Spying in Europe. The Wall Street Journal.
- ^ Pre-Emption - The Nsa And The Telecoms | Spying On The Home Front | FRONTLINE | PBS
- ^ Cohen, Martin. No Holiday. New York: Disinformation Company Ltd. ISBN 978-1-932857-29-0.
{{cite book}}:|access-date=requires|url=(help) - ^ Peggy Becker (October 1999). DEVELOPMENT OF SURVEILLANCE TECHNOLOGY AND RISK OF ABUSE OF ECONOMIC INFORMATION (Report). STOA, European Parliament. Retrieved November 3, 2013.
{{cite report}}: Cite has empty unknown parameter:|coauthors=(help) - ^ Snowden has ‘thousands’ of damaging NSA documents, says Greenwald
- ^ Glenn Greenwald and Ewen MacAskill. "Boundless Informant: the NSA's secret tool to track global surveillance data". The Guardian. Retrieved June 12, 2013.
- ^ "Senators: Limit NSA snooping into US phone records". Associated Press. Retrieved October 15, 2013.
"Is it the goal of the NSA to collect the phone records of all Americans?" Udall asked at Thursday's hearing. "Yes, I believe it is in the nation's best interest to put all the phone records into a lockbox that we could search when the nation needs to do it. Yes," Alexander replied.
- ^ Siobhan Gorman. "Meltdowns Hobble NSA Data Center". The Wall Street Journal. Retrieved October 19, 2013.
The Utah facility, one of the Pentagon's biggest U.S. construction projects, has become a symbol of the spy agency's surveillance prowess, which gained broad attention in the wake of leaks from NSA contractor Edward Snowden.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "New data show how closely FBI monitored Marilyn Monroe". CBS News. December 28, 2012.
- ^ Ryan Gallagher (2002/05/07). "Documents Show the NSA Spied on Muhammad Ali, Martin Luther King Jr., and ... Art Buchwald". Slate (magazine). Retrieved October 27, 2013.
{{cite web}}: Check date values in:|date=(help); Italic or bold markup not allowed in:|publisher=(help) - ^ a b c "Factbox: History of mass surveillance in the United States". Reuters. Retrieved August 14, 2013.
- ^ The Center for Cryptologic History. "The Origins of NSA (NSA.gov)". Web.archive.org. Archived from the original on March 18, 2004.
- ^ Epsley-Jones, Katelyn; Frenzel, Christina. "The Church Committee Hearings & the FISA Court". PBS. Retrieved August 14, 2013.
- ^ Bamford, James. "The Agency That Could Be Big Brother". The New York Times. Retrieved August 14, 2013.
- ^ DAVID BURNHAM. "TRUMAN WIRETAPS ON EX-NEW DEAL AIDE CITED". The New York Times. Retrieved September 18, 2013.
{{cite news}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "FBI campaign against Einstein revealed". BBC. Retrieved September 17, 2013.
- ^ "Albert Einstein: Fact or Fiction?". History (TV channel). Retrieved September 17, 2013.
Because of his controversial political beliefs-his support for socialism, civil rights, and nuclear disarmament, for example-many anti-Communist crusaders believed that Einstein was a dangerous subversive. Some, like FBI director J. Edgar Hoover, even thought he was a spy. For 22 years, Hoover's agents tapped Einstein's phones, opened his mail, rifled through his trash and even bugged his secretary's nephew's house, all to prove that he was more radical (as his 1,500-page FBI dossier noted) than "even Stalin himself."
- ^ RONALD J. OSTROW and LISA GETTER. "FBI Files on Sinatra Detail Links to JFK, Mob Figures". Los Angeles Times. Retrieved September 18, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ MOLOTSKY, IRVIN. "F.B.I. Releases Its Sinatra File, With Tidbits Old and New". The New York Times. Retrieved September 18, 2013.
{{cite news}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "Question: Why is Eleanor Roosevelt's FBI file so large?". George Washington University. Retrieved September 18, 2013.
- ^ "Eleanor Roosevelt". History (TV channel). Retrieved September 18, 2013.
J. Edgar Hoover (1895–1972), the longtime director of the Federal Bureau of Investigation, considered Eleanor Roosevelt's liberal views dangerous and believed she might be involved in communist activities. He ordered his agents to monitor Roosevelt and keep what became an extensive file on her.
- ^ "FBI removes many redactions in Marilyn Monroe file". Associated Press. Retrieved September 18, 2013.
- ^ Cohen, Adam. "While Nixon Campaigned, the F.B.I. Watched John Lennon". The New York Times. Retrieved September 18, 2013.
{{cite news}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "Martin Luther King, Jr. FBI File". Pickler Memorial Library (Truman State University). Retrieved September 17, 2013.
- ^ Church, Frank (April 23, 1976), "Church Committee Book III", Dr. Martin Luther King, Jr., Case Study, Church Committee
- ^ "FBI tracked King's every move". CNN. Retrieved September 17, 2013.
- ^ "'Life Lessons' From a White House Plumber". NPR.
When Daniel Ellsberg leaked the Pentagon Papers to The New York Times in 1971, the Nixon White House tried to discredit him. Among other things, Nixon loyalists burglarized the office of Ellsberg's psychiatrist.
- ^ "The Watergate Story". The Washington Post. Retrieved September 17, 2013.
The White House "plumbers" unit - named for their orders to plug leaks in the administration - burglarizes a psychiatrist's office to find files on Daniel Ellsberg, the former defense analyst who leaked the Pentagon Papers.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "Watergate and the Constitution". National Archives and Records Administration. Retrieved September 17, 2013.
- ^ "INVESTIGATIONS: Nobody Asked: Is It Moral?". Time. May 10, 1976.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "British intelligence 'birdwatchers spied on Nelson Mandela's hideout'". The Daily Telegraph. Retrieved September 21, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "Nelson Mandela 'was spied on by MI6 birdwatchers'". The Times. Retrieved September 21, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "NSA Admits to Spying on Princess Diana". The Washington Post. Retrieved September 21, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ David Hencke and Rob Evans (August 6, 1999). "US holds secret files on Diana". The Guardian.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b U.S. National Security Agency. Early Papers Concerning US-UK Agreement – 1940–1944. Agreement between British Government Code and Cipher School and U.S. War Department dated May 17, 1943. Retrieved: October 5, 2013.
- ^ a b c d Norton-Taylor, Richard (June 25, 2010). "Not so secret: deal at the heart of UK-US intelligence". The Guardian. Retrieved June 25, 2010.
- ^ Campbell, Duncan (August 12, 1988). "Somebody's Listening". New Statesman. Archived from the original on January 3, 2007. Retrieved September 16, 2013.
{{cite news}}: Unknown parameter|deadurl=ignored (|url-status=suggested) (help) - ^ a b Schmid, Gerhard (July 11, 2001). "On the existence of a global system for the interception of private and commercial communications (ECHELON interception system), (2001/2098(INI))" (PDF). European Parliament: Temporary Committee on the ECHELON Interception System. p. 194. Retrieved September 16, 2013.
{{cite web}}: Unknown parameter|deadurl=ignored (|url-status=suggested) (help) - ^ Andrew Bomford (November 3, 1999). "Echelon spy network revealed". BBC.
- ^ "UK 'spied on UN's Kofi Annan'". BBC. February 2004.
- ^ James Chapman, Gerri Peev and Ian Drury (November 30, 2010). "WikiLeaks are a bunch of terrorists, says leading U.S. congressman as No10 warns of threat to national security". Daily Mail.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "US diplomats spied on UN leadership". The Guardian. Retrieved August 27, 2013.
- ^ "Warrantless Surveillance and the Foreign Intelligence Surveillance Act: The Role of Checks and Balances in Protecting Americans' Privacy Rights (Part II): Hearing Before the H. Comm. on the Judiciary, 110th Cong. 13–30 (statement of J.M. McConnell, Director of National Intelligence)" (PDF). September 18, 2007.
- ^ a b Risen, James; Lichtblau, Eric. "Bush Lets U.S. Spy on Callers Without Courts". The New York Times. Retrieved August 14, 2013.
The White House asked The New York Times not to publish this article
- ^ a b "President Visits Troops at Brooke Army Medical Center". White House. January 1, 2006, 12:05 PM CST. Retrieved August 15, 2013.
{{cite web}}: Check date values in:|date=(help) - ^ "AT&T Whistle-Blower's Evidence". Wired. May 17, 2006. Retrieved August 14, 2013.
- ^ a b Poulsen, Kevin. "Whistle-Blower: Feds Have a Backdoor Into Wireless Carrier — Congress Reacts". Wired. Retrieved August 14, 2013.
- ^ WILLIAM SAFIRE (November 14, 2002). "You Are a Suspect". The New York Times. Retrieved September 20, 2013.
{{cite news}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "WikiLeaks FAQ: What Do the Diplomatic Cables Really Tell Us?". Der Spiegel. Retrieved August 14, 2013.
- ^ Davies, Nick; Leigh, David (July 25, 2010). "Afghanistan war logs: Massive leak of secret files exposes truth of occupation". The Guardian. London. Retrieved July 26, 2010.
- ^ "The WikiLeaks Iraq War Logs: Greatest Data Leak in US Military History". Der Spiegel. October 22, 2010. Retrieved October 23, 2010.
- ^ "The NSA Is Building the Country's Biggest Spy Center (Watch What You Say)". Wired. Retrieved August 14, 2013.
- ^ Greenberg, Andy. "NSA Chief Denies Wired's Domestic Spying Story (Fourteen Times) In Congressional Hearing". Forbes. Retrieved August 14, 2013.
- ^ "U.S. agency denies data center to monitor citizens' emails". Reuters. Retrieved September 22, 2013.
- ^ a b Laura Poitras, Marcel Rosenbach and Holger Stark. "Codename 'Apalachee': How America Spies on Europe and the UN". Der Spiegel. p. 2. Retrieved August 26, 2013.
- ^ a b MacAskill, Ewen; Davies, Nick; Hopkins, Nick; Borger, Julian; Ball, James (June 17, 2013). "GCHQ intercepted foreign politicians' communications at G20 summits". The Guardian. London.
{{cite news}}: CS1 maint: multiple names: authors list (link) - ^ "Edward Snowden: US government has been hacking Hong Kong and China for years". South China Morning Post. Retrieved September 9, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Laura Poitras, Marcel Rosenbach, Fidelius Schmid and Holger Stark. "Attacks from America: NSA Spied on European Union Offices". Der Spiegel. Retrieved September 9, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help)CS1 maint: multiple names: authors list (link) - ^ a b Staff (August 31, 2013). "Snowden Document: NSA Spied On Al Jazeera Communications". Retrieved August 31, 2013.
- ^ ROMERO, SIMON. "N.S.A. Spied on Brazilian Oil Company, Report Says". The New York Times. Retrieved September 9, 2013.
{{cite news}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "US bugged Merkel's phone from 2002 until 2013, report claims". BBC. Retrieved October 27, 2013.
- ^ Duran-Sanchez, Mabel (August 10, 2013). "Greenwald Testifies to Brazilian Senate about NSA Espionage Targeting Brazil and Latin America". Retrieved August 13, 2013.
- ^ "Glenn Greenwald afirma que documentos dizem respeito à interesses comerciais do governo americano". August 6, 2013. Retrieved August 13, 2013.
- ^ a b How Microsoft handed the NSA access to encrypted messages, The Guardian, July 12, 2013. Retrieved July 13, 2013.
- ^ Bridie Jabour in Sydney (July 12, 2013). "Telstra signed deal that would have allowed US spying". The Guardian.
- ^ The first three days of revelations were: the FISC court order that Verizon provide bulk metadata on its customers to the NSA; presentation slides explaining the cooperation of nine US internet giants through the PRISM program; and the bulk collection of Chinese users' text messages, which coincided with Xi Jinping's visit to California to meet Barack Obama.
- ^ a b c d e f Laura Poitras, Marcel Rosenbach and Holger Stark. "Ally and Target: US Intelligence Watches Germany Closely". Der Spiegel. Retrieved August 13, 2013.
- ^ "Colombia asks Kerry to explain NSA spying". The Washington Post. Retrieved August 13, 2013.
- ^ "Greenwald diz que espionagem dá vantagens comerciais e industriais aos Estados Unidos" (in Portuguese). Federal Senate of Brazil. Retrieved August 13, 2013.
- ^ "Greenwald diz que EUA espionam para obter vantagens comerciais" (in Portuguese). Deutsche Welle. Retrieved August 13, 2013.
- ^ "NSA's activity in Latin America is 'collection of data on oil and military purchases from Venezuela, energy and narcotics from Mexico' – Greenwald". Voice of Russia. Retrieved August 13, 2013.
- ^ a b "Exclusive: U.S. directs agents to cover up program used to investigate Americans". Reuters. Retrieved August 14, 2013.
- ^ a b c d e f "U.S. spy network's successes, failures and objectives detailed in 'black budget' summary". August 29, 2013. Retrieved August 29, 2013.
{{cite news}}: Cite uses deprecated parameter|authors=(help) - ^ Maass, Peter. "How Laura Poitras Helped Snowden Spill His Secrets". The New York Times. Retrieved August 13, 2013.
- ^ Easley, Jonathan. "Snowden: NSA targeted journalists critical of government after 9/11". The Hill. Retrieved August 14, 2013.
- ^ Laura Poitras, Marcel Rosenbach, Fidelius Schmid and Holger Stark. "Attacks from America: NSA Spied on European Union Offices". Der Spiegel. Retrieved August 26, 2013.
{{cite web}}: CS1 maint: multiple names: authors list (link) - ^ "Report: Canada spies targeted Brazil mine ministry". Associated Press. Retrieved October 7, 2013.
- ^ "'Success Story': NSA Targeted French Foreign Ministry". Der Spiegel. Retrieved September 24, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b Shobhan Saxena. "NSA planted bugs at Indian missions in D.C., U.N." The Hindu. Retrieved September 24, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Jens Glüsing, Laura Poitras, Marcel Rosenbach and Holger Stark. "Fresh Leak on US Spying: NSA Accessed Mexican President's Email". Der Spiegel. Retrieved October 20, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help)CS1 maint: multiple names: authors list (link) - ^ a b c d Laura Poitras, Marcel Rosenbach, Fidelius Schmid und Holger Stark. "Geheimdokumente: NSA horcht EU-Vertretungen mit Wanzen aus". Der Spiegel (in German). Retrieved June 29, 2013.
{{cite web}}: CS1 maint: multiple names: authors list (link) - ^ a b c d e f g h i "US-Geheimdienst hörte Zentrale der Vereinten Nationen ab". Der Spiegel (in German). Retrieved August 25, 2013.
- ^ a b c d e f "5-nation spy alliance too vital for leaks to harm". Associated Press. Retrieved August 29, 2013.
- ^ a b c "NDB und NSA kooperieren enger als bisher bekannt" (in German). Handelszeitung. Retrieved September 18, 2013.
- ^ a b c unlisted (August 3, 2013). "Überwachung: BND leitet massenhaft Metadaten an die NSA weiter". Der Spiegel (in German). Retrieved August 3, 2013.
- ^ a b 'Prolific Partner': German Intelligence Used NSA Spy Program, Der Spiegel. Retrieved July 21, 2013.
- ^ "Verfassungsschutz beliefert NSA" (in German). Süddeutsche Zeitung. Retrieved September 14, 2013.
Seit Juli 2013 testet der Verfassungsschutz die Späh- und Analysesoftware XKeyscore. Sollte der Geheimdienst das Programm im Regelbetrieb nutzen, hat sich das BfV verpflichtet, alle Erkenntnisse mit der NSA zu teilen. Das hatte der Präsident des Bundesamtes, Hans-Georg Maaßen, dem US-Dienst zugesichert. Im Januar und Mai war Maaßen zu Besuchen bei der NSA.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "Verfassungsschutz beliefert NSA" (in German). Süddeutsche Zeitung. Retrieved September 14, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b Glenn Greenwald, Laura Poitras and Ewen MacAskill (September 11, 2013). "NSA shares raw intelligence including Americans' data with Israel". The Guardian. Retrieved September 14, 2013.
- ^ "NSA asked Japan to tap regionwide fiber-optic cables in 2011". The Japan Times. Retrieved October 28, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Olmer, Bart. "Ook AIVD bespiedt internetter" (in Dutch). De Telegraaf. Retrieved September 10, 2013.
Niet alleen Amerikaanse inlichtingendiensten monitoren internetters wereldwijd. Ook Nederlandse geheime diensten krijgen informatie uit het omstreden surveillanceprogramma 'Prism'.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "Norway denies U.S. spying, said it shared intelligence with U.S." Reuters. Retrieved 19 November 2013.
- ^ Kjetil Malkenes Hovland. "Norway Monitored Phone Traffic and Shared Data With NSA". The Wall Street Journal. Retrieved 19 November 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b c Dorling, Philip. "Australian spies in global deal to tap undersea cables". The Sydney Morning Herald. Retrieved August 29, 2013.
- ^ a b "Sverige deltog i NSA-övervakning" (in Swedish). Svenska Dagbladet. Retrieved September 10, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Christof Moser and Alan Cassidy. "Geheimdienst-Aufsicht will Kooperation des NDB mit der NSA prüfen" (in German). Schweiz am Sonntag. Retrieved September 18, 2013.
Die NSA hat sowohl mit der Schweiz wie Dänemark eine geheime Vereinbarung abgeschlossen, die den Austausch von Geheimdienstinformationen regelt. Die Vereinbarung berechtigt die NSA, eigene Schlüsselbegriffe in die Abhörsysteme beider Staaten einspeisen zu lassen. Im Tausch für damit gewonnene Erkenntnisse der schweizerischen und dänischen Auslandaufklärung erhalten der NDB und der dänische Geheimdienst PET von der NSA Informationen, die sie im eigenen Land aufgrund gesetzlicher Schranken nicht selber sammeln dürfen. Das geheime Abkommen macht auch die Schweiz zu einem NSA-Horchposten.
- ^ a b c d e f g h John Goetz, Hans Leyendecker and Frederik Obermaier (August 28, 2013). "British Officials Have Far-Reaching Access To Internet And Telephone Communications". Retrieved August 28, 2013.
- ^ "Edward Snowden Interview: The NSA and Its Willing Helpers". Der Spiegel. Retrieved August 29, 2013.
Snowden: Yes, of course. We're (the NSA) in bed together with the Germans the same as with most other Western countries.
- ^ Laura Poitras, Marcel Rosenbach and Holger Stark. "Ally and Target: US Intelligence Watches Germany Closely". Der Spiegel. Retrieved August 29, 2013.
The NSA classifies about 30 other countries as "3rd parties," with whom it cooperates, though with reservations. Germany is one of them. "We can, and often do, target the signals of most 3rd party foreign partners," the secret NSA document reads.
- ^ "Terror attacks hit U.S." CNN. September 11, 2001.
- ^ a b Leslie Cauley (5/11/2006). "NSA has massive database of Americans' phone calls". USA Today.
{{cite web}}: Check date values in:|year=(help); Italic or bold markup not allowed in:|publisher=(help) - ^ JOHN O'NEIL (May 11, 2006). "Bush Says U.S. Spying Is Not Widespread". The New York Times.
{{cite news}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b Glenn Greenwald (June 6, 2013). "NSA collecting phone records of millions of Verizon customers daily". The Guardian. Retrieved September 16, 2013.
{{cite news}}: Unknown parameter|deadurl=ignored (|url-status=suggested) (help) - ^ Shorrock, Tim (April 15, 2013). "The Untold Story: Obama's Crackdown on Whistleblowers: The NSA Four reveal how a toxic mix of cronyism and fraud blinded the agency before 9/11". The Nation.
- ^ Mayer, Jane (May 23, 2011). "The Secret Sharer: Is Thomas Drake an enemy of the state?". The New Yorker.
- ^ JAMES RISEN and ERIC LICHTBLAU (December 16, 2005). "Bush Lets U.S. Spy on Callers Without Courts". The New York Times.
{{cite news}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b Mark Hosenball (August 15, 2013), Snowden downloaded NSA secrets while working for Dell, sources say Reuters
- ^ a b Peter Maass (August 18, 2013), How Laura Poitras Helped Snowden Spill His Secrets The New York Times
- ^ Carmon, Irin (June 10, 2013). "How we broke the NSA story". Salon. Retrieved June 11, 2013.
- ^ Greenwald, Glenn; MacAskill, Ewen; Poitras, Laura (June 9, 2013). "Edward Snowden: the whistleblower behind the NSA surveillance revelations". The Guardian. London. Retrieved June 9, 2013.
- ^ Smith, Matt; Pearson, Michael (June 10, 2013). "NSA leaker holed up in Hong Kong hotel, running low on cash". CNN. Retrieved June 10, 2013.
- ^ "How Edward Snowden led journalist and film-maker to reveal NSA secrets". The Guardian. Retrieved August 20, 2013.
- ^ "U.S., British intelligence mining data from nine U.S. Internet companies in broad secret program". The Washington Post. Retrieved August 20, 2013.
- ^ MacAskill, Ewen; Borger, Julian; Hopkins, Nick; Davies, Nick; Ball, James (June 21, 2013). "GCHQ taps fiber-optic cables for secret access to world's communications". The Guardian.
- ^ Greenwald, Glenn (July 31, 2013)."XKeyscore: NSA tool collects 'nearly everything a user does on the internet' – XKeyscore Gives 'Widest-Reaching' Collection of Online Data – NSA Analysts Require No Prior Authorization for Searches – Sweeps Up Emails, Social Media Activity and Browsing History". The Guardian. Retrieved August 1, 2013.
- ^ a b c Nakashima, Ellen (July 31, 2013). "Newly declassified documents on phone records program released". The Washington Post. Retrieved August 4, 2013.
- ^ Charlie Savage and David E. Sanger (July 31, 2013). "Senate Panel Presses N.S.A. on Phone Logs". The New York Times. Retrieved August 4, 2013.
- ^ Glenn Greenwald, Ewen MacAskill, Laura Poitras, Spencer Ackerman and Dominic Rushe (July 11, 2013). "Revealed: how Microsoft handed the NSA access to encrypted messages". The Guardian. Retrieved July 11, 2013.
{{cite news}}: CS1 maint: multiple names: authors list (link) - ^ EXCLUSIVE: US hacks Chinese mobile phone companies, South China Morning Post
- ^ NSA targeted China's Tsinghua University in hacking attacks, South China Morning Post
- ^ Lam, Lana (June 23, 2013). "US hacked Pacnet, Asia Pacific fibre-optic network operator, in 2009". South China Morning Post (Hong Kong). Retrieved June 25, 2013.
- ^ Laura Poitras, Marcel Rosenbach und Holger Stark. "Geheimdokumente: NSA überwacht 500 Millionen Verbindungen in Deutschland". Der Spiegel (in German). Retrieved June 30, 2013.
- ^ Glenn Greenwald and Spencer Ackerman (June 27, 2013). "NSA collected US email records in bulk for more than two years under Obama". The Guardian. Retrieved August 1, 2013.
- ^ a b c d e Glenn Greenwald and Spencer Ackerman (June 27, 2013). "How the NSA is still harvesting your online data". The Guardian. Retrieved August 1, 2013.
- ^ MacAskill, Ewen; Borger, Julian (June 30, 2013). "New NSA leaks show how US is bugging its European allies". The Guardian. London.
{{cite news}}: CS1 maint: multiple names: authors list (link) - ^ Aid, Matthew M. (June 10, 2013). "Inside the NSA's Ultra-Secret China Hacking Group". Foreign Policy. Retrieved June 11, 2013.
- ^ EUA espionaram milhões de e-mails e ligações de brasileiros, O Globo, July 6, 2013. Retrieved July 8, 2013.
- ^ The NSA's mass and indiscriminate spying on Brazilians, Glenn Greenwald, The Guardian, July 7, 2013. Retrieved July 8, 2013.
- ^ EUA expandem o aparato de vigilância continuamente, O Globo, July 6, 2013. Retrieved July 8, 2013.
- ^ Philip Dorling (July 8, 2013). "Snowden reveals Australia's links to US spy web". The Age World. Retrieved July 8, 2013.
- ^ "Interview mit Edward Snowden: NSA liefert BND Werkzeuge für Lauschangriff". Der Spiegel (in German). July 7, 2013. Retrieved September 14, 2013.
- ^ "Snowden: NSA steckte "unter einer Decke mit den Deutschen" Zusammenarbeit zwischen US-Geheimdienst und BND offenbar enger als bekannt" (in German). Deutschlandradio. July 7, 2013. Retrieved September 14, 2013.
- ^ Angwin, Julia (December 13, 2012). "U.S. Terrorism Agency to Tap a Vast Database of Citizens". The Wall Street Journal. Retrieved August 21, 2013.
- ^ Iain Thomson (July 8, 2013). "Snowden: US and Israel did create Stuxnet attack code". The Register. Retrieved July 8, 2013.
- ^ Révélations sur le Big Brother français(2), Le Monde, July 4, 2013. Retrieved July 5, 2013.
- ^ France 'runs vast electronic spying operation using NSA-style methods', The Guardian, July 4, 2013. Retrieved July 5, 2013.
- ^ "NDR/SZ: Neue Dokumente belasten britischen Geheimdienst – Deutsche Telekom verlangt Auskünfte". NDR Presse und Information (in German). NDR. August 28, 2013. Retrieved August 30, 2013.
- ^ a b John Goetz, Hans Leyendecker and Frederik Obermaier (August 28, 2013). "Britischer Geheimdienst zapft Daten aus Deutschland ab". Süddeutsche Zeitung (in German). Retrieved August 30, 2013.
- ^ a b c d e f g h John Goetz and Frederik Obermaier. "Snowden enthüllt Namen der spähenden Telekomfirmen". Süddeutsche Zeitung (in German). Retrieved August 2, 2013.
In den internen Papieren des GCHQ aus dem Jahr 2009 stehen sie nun aufgelistet: Verizon Business, Codename: Dacron, British Telecommunications (codenamed "Remedy"), Vodafone Cable ("Gerontic"), Global Crossing ("Pinnage"), Level 3 (codenamed "Little"), Viatel ("Vitreous") und Interoute ("Streetcar").
- ^ "Snowden enthüllt Namen der spähenden Telekomfirmen". Süddeutsche Zeitung. Retrieved August 2, 2013.
- ^ unlisted (August 3, 2013). "Überwachung: BND leitet massenhaft Metadaten an die NSA weiter". Retrieved August 3, 2013.
- ^ Geiger, Friedrich (August 3, 2013). "German Intelligence Agency Providing NSA With Metadata – Report". Retrieved August 3, 2013.
- ^ Mass Data: Transfers from Germany Aid US Surveillance August 5, 2013
- ^ Savage, Charlie (August 8, 2013). "N.S.A. Said to Search Content of Messages to and From U.S." The New York Times. Retrieved September 30, 2013.
- ^ "Snowden-Enthüllungen: NSA spionierte al-Dschasira aus". Der SPIEGEL (in German). August 31, 2013. Retrieved August 31, 2013.
- ^ a b c d Siobhan Gorman and Jennifer Valentiono-Devries (August 20, 2013). "New Details Show Broader NSA Surveillance Reach – Programs Cover 75% of Nation's Traffic, Can Snare Emails". The Wall Street Journal. Retrieved August 21, 2013.
- ^ "Graphic: How the NSA Scours Internet Traffic in the U.S." The Wall Street Journal. August 20, 2013. Retrieved August 21, 2013.
- ^ Jennifer Valentiono-Devries and Siobhan Gorman (August 20, 2013). "What You Need to Know on New Details of NSA Spying". The Wall Street Journal. Retrieved August 21, 2013.
- ^ Jennifer Valentino-Devries and Danny Yadron (August 1, 2013). "FBI Taps Hacker Tactics to Spy on Suspects". The Wall Street Journal. Retrieved October 9, 2013.
- ^ Jennifer Valentino-DeVries and Danny Yadron (August 1, 2013). "How the FBI Hacks Criminal Suspects". The Wall Street Journal. Retrieved October 9, 2013.
- ^ a b c d e f g h i j k l m n o p q r "NSA report on privacy violations in the first quarter of 2012". The Washington Post. August 16, 2013. Retrieved August 16, 2013.
- ^ a b Barton Gellman and Matt DeLong (August 15, 2013). "What to say, and not to say, to 'our overseers'". The Washington Post. Retrieved August 25, 2013.
- ^ a b Barton Gellman and Matt DeLong (August 15, 2013). "First direct evidence of illegal surveillance found by the FISA court". The Washington Post. Retrieved August 25, 2013.
- ^ Gellmann, Barton (August 16, 2013). "NSA broke privacy rules thousands of times per year, audit finds". The Washington Post. Retrieved August 24, 2013.
- ^ Nakashima, Ellen (August 16, 2013). "Lawmakers, privacy advocates call for reforms at NSA". The Washington Post. Retrieved August 25, 2013.
- ^ Gellmann, Barton (August 16, 2013). "NSA statements to The Post". The Washington Post. Retrieved August 25, 2013.
- ^ Barton Gellman and Matt DeLong (August 15, 2013). "What's a 'violation'?". The Washington Post. Retrieved August 25, 2013.
- ^ Leonnig, Carol D. (August 16, 2013). "Court: Ability to police U.S. spying program limited". The Washington Post. Retrieved August 25, 2013.
- ^ a b Nakashima, Ellen (August 21, 2013). "NSA gathered thousands of Americans' e-mails before court ordered it to revise its tactics". The Washington Post. Retrieved September 16, 2013.
- ^ a b "FISA court ruling on illegal NSA e-mail collection program". The Washington Post. August 21, 2013. Retrieved September 16, 2013.
- ^ a b Barton Gellman and Matt DeLong (August 15, 2013). "First direct evidence of illegal surveillance found by the FISA court". The Washington Post. Retrieved September 16, 2013.
- ^ a b Charlie Savage and Scott Shane (August 21, 2013). "Secret Court Rebuked N.S.A. on Surveillance". The New York Times. Retrieved September 16, 2013.
- ^ a b Mark Hosenball and Tabassum Zakaria (August 22, 2013). "NSA collected 56,000 emails by Americans a year: documents". Reuters. NBC News. Retrieved September 16, 2013.
- ^ a b Craig Timberg and Barton Gellman (August 30, 2013). "NSA paying U.S. companies for access to communications networks". The Washington Post. Retrieved August 31, 2013.
- ^ Wallsten, Peter (August 17, 2013). "House panel withheld document on NSA surveillance program from members". The Washington Post. Retrieved August 25, 2013.
- ^ Weich, Ronald. "Report of the National Security Agency's Bulk Collection Programs for USA PATRIOT Act Reauthorization" (PDF). Office of the Assistant Attorney General. Director of National Intelligence. Retrieved August 25, 2013.
- ^ James Ball, Luke Harding and Juliette Garside (August 1, 2013). "Exclusive: NSA pays £100m in secret funding for GCHQ". Retrieved August 2, 2013.
- ^ James Ball and Spencer Ackerman (August 9, 2013). "NSA loophole allows warrantless search for US citizens' emails and phone calls – Exclusive: Spy agency has secret backdoor permission to search databases for individual Americans' communications". The Guardian. Retrieved August 12, 2013.
- ^ Farivar, Cyrus (August 10, 2013). "New leak: NSA can search US e-mail data but theoretically won't". Ars Technica. Retrieved August 13, 2013.
- ^ Roberts, Dan (August 23, 2013). "US surveillance guidelines not updated for 30 years, privacy board finds – Privacy watchdog points out in letter to intelligence chiefs that rules designed to protect Americans are severely outdated". The Guardian. Retrieved August 24, 2013.
- ^ Medine, David (August 22, 2013). "2013-08-22 Privacy and Civil Liberties Oversight Board letter to US Attorney General Eric Holder and Directer of National Intelligence James Clapper" (PDF). amazonnews.com. Retrieved August 24, 2013.
- ^ Strohm, Chris (August 24, 2013). "Lawmakers Probe Willful Abuses of Power by NSA Analysts". Bloomberg News. Retrieved August 24, 2013.
- ^ Roberts, Dan (August 23, 2013). "NSA analysts deliberately broke rules to spy on Americans, agency reveals – Inspector general's admission undermines fresh insistences from president that breaches of privacy rules were inadvertent". The Guardian. Retrieved August 24, 2013.
- ^ Gorman, Siobhan (August 23, 2013). "NSA Officers Spy on Love Interests". The Wall Street Journal. Retrieved August 24, 2013.
- ^ MacAskill, Ewen (August 23, 2013). "NSA paid millions to cover Prism compliance costs for tech companies • Top-secret files show first evidence of financial relationship • Prism companies include Google and Yahoo, says NSA • Costs were incurred after 2011 Fisa court ruling". The Guardian. Retrieved August 24, 2013.
- ^ David Leppard and Chris Williams (May 3, 2009). "Jacqui Smith's secret plan to carry on snooping". The Sunday Times. Retrieved May 3, 2009.
- ^ Henry Porter. "GCHQ revelations: mastery of the internet will mean mastery of everyone". The Guardian. Retrieved October 19, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b c d e James Ball, Julian Borger and Glenn Greenwald (September 5, 2013). "US and UK spy agencies defeat privacy and security on the internet". The Guardian. Retrieved September 5, 2013.
- ^ Nicole Perlroth, Jeff Larson and Scott Shane (September 5, 2013). "N.S.A. Foils Much Internet Encryption". The New York Times. Retrieved September 5, 2013.
- ^ "Secret Documents Reveal N.S.A. Campaign Against Encryption". The New York Times. September 5, 2013. Retrieved September 7, 2013.
- ^ "Unlocking Private Communications". The New York Times. September 5, 2013. Retrieved September 7, 2013.
- ^ Perlroth, Nicole, Larson, Jeff, and Shane, Scott (September 5, 2013). "The NSA's Secret Campaign to Crack, Undermine Internet Security". ProPublica.
{{cite news}}: Italic or bold markup not allowed in:|publisher=(help)CS1 maint: multiple names: authors list (link) - ^ Nakashima, Ellen (September 6, 2013). "NSA has made strides in thwarting encryption used to protect Internet communication". The Washington Post. Retrieved September 7, 2013.
- ^ "Frankreich liefert Informationen an britische und US-Geheimdienste". Süddeutsche Zeitung (in German). October 26, 2013. Retrieved October 26, 2013.
- ^ "Verfassungsschutz spionierte für Geheimdienste - Bundesamt-Chef Maaßen stimmte zu". Norddeutscher Rundfunk (in German). Norddeutscher Rundfunk. September 13, 2013. Retrieved September 14, 2013.
- ^ "Verfassungsschutz beliefert NSA". Süddeutsche Zeitung (in German). September 13, 2013. Retrieved September 14, 2013.
- ^ "Auch Verfassungsschutz liefert Daten an NSA "Süddeutsche Zeitung" und NDR berichten über intensiven Datenaustausch". Deutschland Radio (in German). Deutschland Radio. September 13, 2013. Retrieved September 14, 2013.
- ^ "'Follow the Money': NSA Spies on International Payments". Der Spiegel. September 15, 2013. Retrieved September 24, 2013.
- ^ a b "Brazil Angered Over Report N.S.A. Spied on President". The New York Times. Retrieved September 16, 2013.
{{cite news}}: Unknown parameter|deadurl=ignored (|url-status=suggested) (help) - ^ "NSA Documents Show United States Spied Brazilian Oil Giant". Jornal da Globo Fantástico. September 8, 2013. Retrieved September 24, 2013.
- ^ James Risen and Laura Poitras (September 28, 2013). "N.S.A. Gathers Data on Social Connections of U.S. Citizens". The New York Times. Retrieved September 30, 2013.
- ^ "NSA and Israeli intelligence: memorandum of understanding – full document". The Guardian. September 11, 2013. Retrieved September 14, 2013.
- ^ Barton Gellman. "Secret documents detail U.S. war in cyberspace". The Washington Post (via The Japan Times). Retrieved September 2, 2013.
- ^ Barton Gellman and Ellen Nakashima (August 31, 2013). "U.S. spy agencies mounted 231 offensive cyber-operations in 2011, documents show". The Washington Post. Retrieved August 31, 2013.
- ^ Konrad Lischka und Julia Stanek (August 31, 2013). "Cyber-Angriffe: USA infizieren Zehntausende Computer mit NSA-Trojanern". Der SPIEGEL (in German). Retrieved August 31, 2013.
- ^ Zetter, Kim (September 4, 2013). "NSA Laughs at PCs, Prefers Hacking Routers and Switches". Wired.com. Retrieved October 2, 2013.
- ^ a b c d e Laura Poitras, Marcel Rosenbach and Holger Stark. "iSpy: How the NSA Accesses Smartphone Data". Der Spiegel. Retrieved September 9, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b Laura Poitras, Marcel Rosenbach, and Holger Stark. "Photo Gallery: Spying on Smartphones". Der Spiegel. Retrieved September 9, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help)CS1 maint: multiple names: authors list (link) - ^ Barton Gellman, Craig Timberg and Steven Rich (4 October 2013). "Secret NSA documents show campaign against Tor encrypted network". The Washington Post. Retrieved 19 November 2013.
- ^ Steven Rich and Matt DeLong (4 October 2013). "NSA slideshow on 'The TOR problem'". The Washington Post. Retrieved 19 November 2013.
- ^ Lee, Timothy B. (4 October 2013). "Everything you need to know about the NSA and Tor in one FAQ". The Washington Post. Retrieved 19 November 2013.
- ^ "NSA report on the Tor encrypted network". The Washington Post. 4 October 2013. Retrieved 19 November 2013.
- ^ "GCHQ report on 'MULLENIZE' program to 'stain' anonymous electronic traffic". The Washington Post. 4 October 2013. Retrieved 19 November 2013.
- ^ James Ball, Bruce Schneier and Glenn Greenwald (4 October 2013). "NSA and GCHQ target Tor network that protects anonymity of web users". The Guardian. Retrieved 19 November 2013.
- ^ Schneier, Bruce (4 October 2013). "Attacking Tor: how the NSA targets users' online anonymity". The Guardian. Retrieved 19 November 2013.
- ^ "'Tor Stinks' presentation – read the full document". The Guardian. 4 October 2013. Retrieved 19 November 2013.
- ^ "Tor: 'The king of high-secure, low-latency anonymity'". The Guardian. 4 October 2013. Retrieved 19 November 2013.
- ^ "Ministério de Minas e Energia está na mira de espiões americanos e canadenses". O Globo. October 6, 2013. Retrieved October 8, 2013.
- ^ "Report: Canada spies targeted Brazil mine ministry". Associated Press. The Associated Press. October 6, 2013. Retrieved October 8, 2013.
- ^ Ockenden, Will (October 8, 2013). "Australia prepared briefing on US global internet spying program PRISM before Snowden revelations". ABC News (Australia). Retrieved October 8, 2013.
- ^ "AG Department Prism FOI PDF". ABC News Online. June 27, 2013. Retrieved October 8, 2013.
- ^ Jens Glüsing, Laura Poitras, Marcel Rosenbach and Holger Stark (October 20, 2013). "Fresh Leak on US Spying: NSA Accessed Mexican President's Email". Der Spiegel. Retrieved October 22, 2013.
{{cite news}}: CS1 maint: multiple names: authors list (link) - ^ "NSA-Spionage: Mexiko fordert Aufklärung über US-Bespitzelungen". Der Spiegel (in German). October 21, 2013. Retrieved October 22, 2013.
- ^ Mark Mazzetti and David E. Sanger (October 30, 2013). "Tap on Merkel Provides Peek at Vast Spy Net". The New York Times. Retrieved November 1, 2013.
- ^ Mark Landler and Michael S. Schmidt (October 30, 2013). "Spying Known at Top Levels, Officials Say". The New York Times. Retrieved November 1, 2013.
- ^ a b Ball, James (October 24, 2013). "NSA monitored calls of 35 world leaders after US official handed over contacts". The Guardian. Retrieved October 24, 2013.
- ^ a b Siobhan Gorhan and Adam Entous (October 28, 2013). "Obama Unaware as U.S. Spied on World Leaders: Officials". The Wall Street Journal. Retrieved October 28, 2013.
- ^ a b Ball, James (October 25, 2013). "Leaked memos reveal GCHQ efforts to keep mass surveillance secret". The Guardian. Retrieved October 25, 2013.
- ^ Nakashima, Ellen (October 2, 2013). "NSA had test project to collect data on Americans' cellphone locations, director says". The Washington Post. Retrieved October 18, 2013.
- ^ Barton Gellman and Ashkan Soltani (October 30, 2013). "NSA infiltrates links to Yahoo, Google data centers worldwide, Snowden documents say". The Washington Post. Retrieved October 31, 2013.
- ^ Barton Gellman, Todd Lindeman and Ashkan Soltani (October 30, 2013). "How the NSA is infiltrating private networks". The Washington Post. Retrieved October 31, 2013.
- ^ Barton Gellman and Matt DeLong (October 30, 2013). "How the NSA's MUSCULAR program collects too much data from Yahoo and Google". The Washington Post. Retrieved October 31, 2013.
- ^ Peterson, Andrea (October 30, 2013). "PRISM already gave the NSA access to tech giants. Here's why it wanted more". The Washington Post. Retrieved October 31, 2013.
- ^ Washington Post Staff (October 30, 2013). "NSA statement on Washington Post report on infiltration of Google, Yahoo data center links". The Washington Post. Retrieved October 31, 2013.
- ^ Jacob Appelbaum, Holger Stark, Marcel Rosenbach and Jörg Schindler (October 23, 2013). "Berlin Complains: Did US Tap Chancellor Merkel's Mobile Phone?". Der Spiegel. Retrieved October 25, 2013.
{{cite news}}: CS1 maint: multiple names: authors list (link) - ^ Fischer, Sebastian (October 24, 2013). "Merkel's Phone: Spying Suspicions Put Obama in a Tight Spot". Der Spiegel. Retrieved October 25, 2013.
- ^ Charly Wilder and Rupert Neat (October 24). "'Out of Hand': Europe Furious Over US Spying Allegations". Der Spiegel. Retrieved October 25, 2013.
{{cite news}}: Check date values in:|date=(help) - ^ Ian Traynor in Brussels, Philip Oltermann in Berlin, and Paul Lewis in Washington (October 24). "Angela Merkel's call to Obama: are you bugging my mobile phone?". The Guardian. Retrieved October 25, 2013.
{{cite news}}: Check date values in:|date=(help)CS1 maint: multiple names: authors list (link) - ^ Ball, James (October 25, 2013). "NSA monitored calls of 35 world leaders after US official handed over contacts". The Guardian. Retrieved October 25, 2013.
- ^ Traynor, Ian (October 25, 2013). "Germany and France warn NSA spying fallout jeopardises fight against terror". The Guardian. Retrieved October 25, 2013.
- ^ a b Jacob Appelbaum, Nikolaus Blome, Hubert Gude, Ralf Neukirch, René Pfister, Laura Poitras, Marcel Rosenbach, Jörg Schindler, Gregor Peter Schmitz and Holger Stark. Translated from the German by Kristen Allen and Charly Wilder. (October 27, 2013). "Der Spiegel Cover Story: How NSA Spied on Merkel Cell Phone from Berlin Embassy - Embassy Espionage: The NSA's Secret Spy Hub in Berlin". Der Spiegel. Retrieved November 1, 2013.
{{cite news}}: CS1 maint: multiple names: authors list (link) - ^ "NSA-Überwachung: Merkels Handy steht seit 2002 auf US-Abhörliste". Der Spiegel (in German). October 26, 2012. Retrieved October 26, 2013.
- ^ "U.S. monitored German Chancellor Angela Merkel's phone since 2002". Reuters. The Daily Mail. October 26, 2012. Retrieved October 26, 2013.
- ^ Ofer Aderet (October 26, 2015). "Obama: Had I known NSA tapped Merkel's cell, I would have stopped it, German media reports". Haaretz. Retrieved October 26, 2013.
- ^ David E. Sanger and Mark Mazzetti (October 24, 2013). "Allegation of U.S. Spying on Merkel Puts Obama at Crossroads". The New York Times. Retrieved October 26, 2013.
- ^ "Germany hopes for details from Snowden on US spying". bbc.co.uk. November 1, 2013. Retrieved November 1, 2013.
- ^ "Photo Gallery: Spies in the Embassy 10/27/2013". Der Spiegel. October 27, 2013. Retrieved November 1, 2013.
- ^ a b Dorling, Philipp (October 31, 2013). "Exposed: Australia's Asia spy network". The Sydney Morning Herald. Retrieved November 1, 2013.
- ^ Konrad Lischka and Matthias Kremp (October 28, 2013). "NSA-Spähskandal: So funktionieren die Abhöranlagen in US-Botschaften". Der Spiegel (in German). Retrieved November 1, 2013.
- ^ Perlez, Jane (October 31, 2013). "Australia Said to Play Part in N.S.A. Effort". The New York Times. Retrieved November 1, 2013.
- ^ Jacques Follorou and Glenn Greenwald (October 21, 2013). "France in the NSA's crosshair : phone networks under surveillance". Le Monde. Retrieved October 22, 2013.
- ^ Gearan, Anna (October 22, 2013). "Report that NSA collected French phone records causing diplomatic headache for U.S." The Washington Post. Retrieved October 22, 2013.
- ^ a b c Adam Entous and Siobhan Gorman (October 29, 2013). "U.S. Says France, Spain Aided NSA Spying". The Wall Street Journal. Retrieved October 29, 2013.
- ^ a b Ellen Nakashima and Karen DeYoung (October 29, 2013). "NSA chief says NATO allies shared phone records with the U.S. spy agency". The Washington Post. Retrieved October 30, 2013.
- ^ "Espionnage de la NSA : tous les documents publiés par "Le Monde"". Le Monde. October 21, 2013. Retrieved October 22, 2013.
- ^ Shane, Scott (2013-11-02). "No Morsel Too Minuscule for All-Consuming N.S.A." New York Times. Archived from the original on 2013-11-25. Retrieved 2013-11-25.
This "communications fingerprinting," as a document called it, is the key to what the N.S.A. does. It allows the agency's computers to scan the stream of international communications and pluck out messages tied to the supreme leader.
- ^ Campbell, Duncan (November 5, 2013). "Revealed: Britain's 'secret listening post in the heart of Berlin'". The Independent. Retrieved November 5, 2013.
- ^ a b Tony Paterson. "GCHQ used 'Quantum Insert' technique to set up fake LinkedIn pages and spy on mobile phone giants". The Independent. Retrieved November 10, 2013.
{{cite news}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b Laura Poitras, Marcel Rosenbach and Holger Stark (November 17, 2013). "'Royal Concierge': GCHQ Monitors Hotel Reservations to Track Diplomats". Der Spiegel. Retrieved November 17, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ ndonesia recalls Canberra ambassador over Yudhoyono phone tapping attempt, Foreign minister demands explanation after documents reveal Australian agencies targeted phones of president and his wife The Guardian 18 November 2013
- ^ Ball, James (20 November 2013). "US and UK struck secret deal to allow NSA to 'unmask' Britons' personal data". The Guardian. Retrieved 21 November 2013.
- ^ a b c JAMES RISEN and LAURA POITRAS (November 22, 2013). "N.S.A. Report Outlined Goals for More Power". The New York Times. Retrieved 23 November 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "A Strategy for Surveillance Powers". The New York Times. Retrieved 23 November 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Floor Boon, Steven Derix and Huib Modderkolk. "Document Snowden: Nederland al sinds 1946 doelwit van NSA" (in Dutch). NRC Handelsblad. Retrieved 23 November 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Floor Boon, Steven Derix and Huib Modderkolk. "NSA infected 50,000 computer networks with malicious software". NRC Handelsblad. Retrieved 23 November 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ John D Bates (October 3, 2011). "[redacted]" (PDF). p. 16.
- ^ Turner, Shawn (July 31, 2013). "DNI Clapper Declassifies and Releases Telephone Metadata Collection Documents". Retrieved August 22, 2013.
- ^ "Minimization Procedures Used by the National Security Agency in Connection with Acquisitions of Foreign Intelligence Information Pursuant to Section 702, as amended" (PDF). October 31, 2011.
- ^ James Ball and Spencer Ackerman (August 9, 2013). "NSA loophole allows warrantless search for US citizens' emails and phone calls". Retrieved August 12, 2013.
- ^ a b John D Bates (October 3, 2011). "[redacted]" (PDF). p. 71.
- ^ Perez, Evan (August 22, 2013). "NSA misrepresented scope of data collection to secret court". CNN. Retrieved October 2, 2013.
- ^ Turner, Shawn (August 21, 2013). "DNI Declassifies Intelligence Community Documents Regarding Collection Under Section 702 of the Foreign Intelligence Surveillance Act (FISA)". Office of the Director of National Intelligence. IC on the Record. Retrieved October 2, 2013.
- ^ Clapper, James (August 21, 2013). "DNI James Clapper's Cover Letter Announcing the Document Release" (PDF). Director of National Intelligence. Retrieved October 2, 2013.
- ^ Kimberly Dozier and Stephen Braun (August 21, 2013). "NSA Collected Thousands Of Emails, Other Communications By Americans With No Terror Ties". The Huffington Post. Associated Press. Retrieved October 2, 2013.
- ^ Fung, Brian (August 21, 2013). "The FISA court got really upset when the NSA didn't tell the truth on surveillance". The Washington Post. Retrieved September 16, 2013.
- ^ Siobhan Gorman and Devlin Barrett (September 10, 2013). "NSA Violated Privacy Protections, Officials Say". Retrieved September 10, 2013.
- ^ Ackerman, Spencer (September 10, 2013). "NSA violations led judge to consider viability of surveillance program". The Guardian. Retrieved September 16, 2013.
- ^ Ellen Nakashima, Julie Tate and Carol Leonnig (September 10, 2013). "Declassified court documents highlight NSA violations in data collection for surveillance". The Washington Post. Retrieved September 14, 2013.
- ^ Office of the Director of National Intelligence. (September 10). "Declassified FISA court documents on intelligence collection". The Washington Post. Retrieved September 14, 2013.
{{cite news}}: Check date values in:|date=(help) - ^ James R. Clapper (Director of National Intelligence) (September 10, 2013). "DNI Clapper Declassifies Intelligence Community Documents Regarding Collection Under Section 501 of the Foreign Intelligence Surveillance Act (FISA)". Office of the Director of National Intelligence. IC On the Record. Retrieved September 14, 2013.
- ^ Tim, Trevor (September 10, 2013). "Government Releases NSA Surveillance Docs and Previously Secret FISA Court Opinions In Response to EFF Lawsuit". Electronic Frontier Foundation. Electronic Frontier Foundation. Retrieved September 14, 2013.
- ^ David Kravets. Kim Zetter, Kevin Poulsen (September 10, 2013). "NSA Illegally Gorged on U.S. Phone Records for Three Years". Wired.com. Retrieved September 22, 2013.
- ^ Staff (August 10, 2013). "US-Geheimdienst: NSA führt Deutschland als Spionageziel".
- ^ Timothy Jones (August 11, 2008). "Germany and EU targets for US espionage, Spiegel reports".
- ^ "The Black Budget". August 29, 2013. Retrieved August 29, 2013.
- ^ "NSA shares raw intelligence including Americans' data with Israel". September 11, 2013. Retrieved September 11, 2013.
{{cite news}}: Cite uses deprecated parameter|authors=(help) - ^ Sailor IV, F. Dennis (September 13, 2013). "United States Foreign Intelligence Surveillance Court In Re Orders of this Court Interpretating Section 215 of the Patriot Act (Docket No. Misc. 13-02)" (PDF). www.uscourts.gov. Retrieved September 15, 2013.
- ^ Fung, Brian (September 13, 2013). "The FISA court will release more opinions because of Snowden". The Washington Post. Retrieved September 15, 2013.
- ^ Ackerman, Spencer (September 13, 2013). "Fisa judge: Snowden's NSA disclosures triggered important spying debate". The Guardian. Retrieved September 16, 2013.
- ^ "DNI Clapper Declassifies Additional Intelligence Community Documents Regarding Collection Under Section 501 of the Foreign Intelligence Surveillance Act". Office of the Director of National Intelligence. IC ON THE RECORD. 18 November 2013. Retrieved 19 November 2013.
- ^ "DNI Clapper Declassifies Additional Intelligence Community Documents Regarding Collection Under Section 501 of the Foreign Intelligence Surveillance Act". Office of the Director of National Intelligence. odni.gov. 18 November. Retrieved 19 November 2013.
{{cite web}}: Check date values in:|date=(help) - ^ Charlie Savage and James Risen (18 November 2013). "Latest Release of Documents on N.S.A. Includes 2004 Ruling on Email Surveillance". The New York Times. Retrieved 19 November 2013.
- ^ Ellen Nakashima and Greg Miller (19 November 2013). "Official releasing what appears to be original court file authorizing NSA to conduct sweeps". The Washington Post. Retrieved 19 November 2013.
- ^ "Documents show NSA reported violations of court's surveillance rules". The New York Daily News. Associated Press.
- ^ a b "Ally and Target: US Intelligence Watches Germany Closely". August 12, 2013. Retrieved August 12, 2013.
{{cite news}}: Cite uses deprecated parameter|authors=(help) - ^ Gellman, Barton (August 16, 2013). "NSA broke privacy rules thousands of times per year, audit finds". Retrieved August 16, 2013.
- ^ "U.S. documents detail al-Qaeda's efforts to fight back against drones". September 3, 2013. Retrieved September 3, 2013.
{{cite news}}: Cite uses deprecated parameter|authors=(help) - ^ "Top-secret U.S. intelligence files show new levels of distrust of Pakistan". September 2, 2013. Retrieved September 3, 2013.
{{cite news}}: Cite uses deprecated parameter|authors=(help) - ^ Staff (September 4, 2013). "US intelligence uncovered Pak army plot to kill Asma Jahangir in India: report". Retrieved September 4, 2013.
- ^ Staff (September 7, 2013). "Privacy Scandal: NSA Can Spy on Smart Phone Data". Retrieved September 7, 2013.
- ^ A published heat map shows that most data is collected from Iran, Pakistan and Jordan, with over 40 billion individual pieces of information collected from these three countries alone in March 2013 alone, from a total of 97 billion worldwide.
- ^ Snowden reveals Australia's links to US spy web, The Sydney Morning Herald, July 8, 2013. Retrieved July 11, 2013.
- ^ a b c "What to say, and not to say, to 'our overseers'". August 16, 2013. Retrieved August 16, 2013.
- ^ a b c d Staff (July 29, 2013). "Photo Gallery: NSA Documentation of Spying in Germany". Retrieved August 11, 2013.
- ^ a b c d e f "Codename 'Apalachee': How America Spies on Europe and the UN". August 26, 2013. Retrieved August 26, 2013.
{{cite news}}: Cite uses deprecated parameter|authors=(help) - ^ "Project Bullrun – classification guide to the NSA's decryption program". September 5, 2013.
- ^ a b c d e f NSA slides explain the PRISM data-collection program, The Washington Post, June 6, 2013, updated July 10, 2013. Retrieved July 12, 2013.
- ^ a b "New slides about NSA collection programs". Top Level Telecommunications. July 16, 2013 and updated on July 16, 2013. Retrieved August 27, 2013.
{{cite web}}: Check date values in:|date=(help) - ^ Kloc, Joe (July 12, 2013). "Forget PRISM: FAIRVIEW is the NSA's project to "own the Internet"". Retrieved August 11, 2013.
- ^ "Espionagem dos EUA se espalhou pela América Latina". July 12, 2013. Retrieved August 11, 2013.
{{cite news}}: Cite uses deprecated parameter|authors=(help) - ^ a b c "The National Security Agency: Missions, Authorities, Oversight and Partnerships" (PDF). National Security Agency. August 9, 2013. Retrieved August 12, 2013.
- ^ a b c Perez, Evan (August 10, 2013). "Documents shed light on U.S. surveillance programs". CNN. Retrieved August 12, 2013.
- ^ a b "NSA loophole allows warrantless search for US citizens' emails and phone calls". August 9, 2013. Retrieved August 11, 2013.
{{cite news}}: Cite uses deprecated parameter|authors=(help) - ^ a b c d e Ambinder, Marc (August 14, 2013). "An Educated Guess About How the NSA Is Structured". Retrieved August 14, 2013.
- ^ a b Gellman, Barton (June 15, 2013). "U.S. surveillance architecture includes collection of revealing Internet, phone metadata". Retrieved August 11, 2013.
- ^ a b Staff (September 15, 2013). "'Follow the Money': NSA Spies on International Payments 'Follow the Money': NSA Spies on International Payments". Retrieved September 15, 2013.
- ^ a b c Staff (September 1, 2013). "'Success Story': NSA Targeted French Foreign Ministry". Retrieved September 1, 2013.
- ^ a b "Jornal O Globo revela que Brasil teria sido espionado pelos Estados Unidos". July 8, 2013. Retrieved September 5, 2013.
- ^ a b Peterson, Josh (June 27, 2013). "Report: NSA Internet spying program collected half-a-trillion records in 2012". The Daily Caller. Retrieved July 29, 2013.
- ^ a b Bamford, James (July 12, 2013). "They Know Much More Than You Think". The New York Review of Books. Retrieved July 29, 2013.
- ^ No alvo dos EUA, Infographic, O Globo. Retrieved July 8, 2013.
- ^ James Ball, Julian Borger and Glenn Greenwald (September 6, 2013). "Revealed: how US and UK spy agencies defeat internet privacy and security". The Guardian. Retrieved September 7, 2013.
- ^ a b "Exclusive: Edward Snowden leaks reveal UK's secret Middle-East web surveillance base". August 22, 2013. Retrieved August 22, 2013.
{{cite news}}: Cite uses deprecated parameter|authors=(help) - ^ Greenwald, Glenn (August 23, 2013). "Snowden: UK government now leaking documents about itself". Retrieved August 23, 2013.
- ^ staff (September 16, 2013). "'Foreign nation with significant means' in spying on Belgium probe". Retrieved September 16, 2013.
- ^ Schmitz, Gregor-Peter (September 20, 2013). "Cyber Attack: Belgians Angered by British Spying". Retrieved September 20, 2013.
- ^ Gallagher, Ryan (September 20, 2013). "http://www.slate.com/blogs/future_tense/2013/09/20/operation_socialist_u_k_s_gchq_hacked_belgacom_snowden_documents_reveal.html". Retrieved September 20, 2013.
{{cite news}}: External link in|title= - ^ a b Goebel, Nicole (August 25, 2013). Schuster, Kathleen (ed.). "NSA spied on UN, German report says". Deutsche Welle. Retrieved August 25, 2013.
- ^ "NSA bugged UN headquarters – newspaper". August 25, 2013. Retrieved August 25, 2013.
- ^ "To hunt Osama bin Laden, satellites watched over Abbottabad, Pakistan, and Navy SEALs". August 29, 2013. Retrieved August 29, 2013.
{{cite news}}: Cite uses deprecated parameter|authors=(help) - ^ Brooks, Bradley (September 1, 2013). "Report: NSA spied on leaders of Brazil, Mexico". Retrieved September 1, 2013.[dead link]
- ^ "Saiba como o maior sistema de espionagem do mundo monitora comunicações em Brasília". September 1, 2013. Retrieved September 1, 2013.
{{cite news}}: Unknown parameter|editors=ignored (|editor=suggested) (help) - ^ "EUA espionaram Dilma". September 1, 2013. Retrieved September 1, 2013.
{{cite news}}: Cite uses deprecated parameter|authors=(help) - ^ Barton Gellman and Ashkan Soltani (October 14, 2013). "NSA collects millions of e-mail address books globally".
- ^ a b "NSA surveillance: A guide to staying secure". The Guardian. Retrieved September 24, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b c Narayan Lakshman. "Secret bunkers, a challenge for U.S. intelligence". The Hindu. Retrieved September 24, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Nelson, Kimberly (August 22, 2013). "In Salt Lake for the 2002 Olympics? Your texts, emails and phone calls likely reviewed by NSA". Retrieved August 25, 2023.
- ^ Davidson, Lee (August 23, 2013). "Former Salt Lake mayor: NSA snooping is the scandal of the century". Retrieved August 25, 2013.
- ^ Freeze, Colin (June 15, 2013). "How Canada's shadowy metadata-gathering program went awry". Retrieved August 27, 2013.
- ^ "Raw documents: Canada's 'top secret' data mining program". June 10, 2013. Retrieved August 27, 2013.
- ^ Freeze, Colin (June 10, 2013). "Data-collection program got green light from MacKay in 2011". Retrieved August 27, 2013.
- ^ "The NYPD Division of Un-American Activities". August 25, 2013. Retrieved August 26, 2013.
{{cite news}}: Cite uses deprecated parameter|authors=(help) - ^ "Blue Coat". Reporters Without Borders. March 12, 2013.
- ^ Citizen Lab, Munk School of Global Affairs, University of Toronto (January 15, 2013). "Planet Blue Coat: Mapping Global Censorship and Surveillance Tools".
{{cite web}}: CS1 maint: multiple names: authors list (link) - ^ Markoff, John (January 16, 2013). "Rights Group Reports on Abuses of Surveillance and Censorship Technology". The New York Times.
- ^ Nakashima, Ellen (July 8, 2013). "Web monitoring devices made by U.S. firm Blue Coat detected in Iran, Sudan". The Washington Post.
- ^ "You Are Being Tracked: How License Plate Readers Are Being Used to Record Americans' Movements". July 17, 2013. Retrieved August 11, 2013.
- ^ Martinez, Michael (July 18, 2013). "ACLU raises privacy concerns about police technology tracking drivers". Retrieved August 11, 2013.
- ^ McCullagh, Declan (August 2, 2013). "FBI pressures Internet providers to install surveillance software".
- ^ "FBI Taps Hacker Tactics to Spy on Suspects". August 3, 2013. Retrieved August 12, 2013.
{{cite news}}: Cite uses deprecated parameter|authors=(help) - ^ Choney, Suzanne (August 6, 2013). "FBI hacking squad used in domestic investigations, experts say". Retrieved August 12, 2013.
- ^ Savage, Charlie (August 8, 2013). "N.S.A. Said to Search Content of Messages to and From U.S". Retrieved August 11, 2013.
- ^ Nixon, Ron (July 3, 2013). "U.S. Postal Service Logging All Mail for Law Enforcement". Retrieved August 11, 2013.
{{cite news}}: Unknown parameter|deadurl=ignored (|url-status=suggested) (help) - ^ Dharmakumar, Rohin (August 13, 2013). "Keep your virtual life away from prying governments". Retrieved August 13, 2013.
- ^ Parbat, Kalyan (July 27, 2013). "Israel's Verint to get government contract for interception tools". Retrieved August 13, 2013.
- ^ Kirka, Danica (August 19, 2013). "Partner of reporter at center of NSA leak detained". Retrieved August 19, 2013.
- ^ Staff (August 21, 2013). "New Zealand passes bill allowing domestic spying". Retrieved August 23, 2013.
- ^ Watkins, Tracy (August 21, 2013). "Spy bill passes into law amid wide criticism". Retrieved August 23, 2013.
- ^ "Podcast Show #112: NSA Whistleblower Goes on Record -Reveals New Information & Names Culprits!" (Podcast). June 19, 2013. Retrieved August 15, 2013.
- ^ Hill, Kashmir (July 24, 2013). "Blueprints of NSA's Ridiculously Expensive Data Center in Utah Suggest It Holds Less Info Than Thought". Retrieved August 11, 2013.
- ^ Priest, Dana (July 21, 2013). "NSA growth fueled by need to target terrorists". Retrieved August 11, 2013.
- ^ "Exclusive: U.S. directs agents to cover up program used to investigate Americans". August 5, 2013. Retrieved August 11, 2013.
{{cite news}}: Cite uses deprecated parameter|authors=(help) - ^ "Exclusive: IRS manual detailed DEA's use of hidden intel evidence". August 7, 2013. Retrieved August 12, 2013.
{{cite news}}: Cite uses deprecated parameter|authors=(help) - ^ Lindsay, Jonathan S (July 27, 2013). "U.S. allowed Italian kidnap prosecution to shield higher-ups, ex-CIA officer says". Retrieved August 11, 2013.
- ^ Obama’s crackdown views leaks as aiding enemies of U.S., McClatchy, June 20, 2013. Retrieved July 12, 2013.
- ^ "Stellungnahme des BSI zur aktuellen Berichterstattung zu MS Windows 8 und TPM". August 21, 2013. Retrieved August 22, 2013.
- ^ Staff (August 22, 2013). "German Federal Government Warns on the Security Dangers of Windows 8". Retrieved August 22, 2013.
- ^ "U.S. intelligence agencies spend millions to hunt for insider threats, document shows". September 1, 2013. Retrieved September 2, 2013.
{{cite news}}: Cite uses deprecated parameter|authors=(help) - ^ Strohm, Chris (August 23, 2013). "Lawmakers Probing Intentional Abuses of Power by NSA Analysts". Retrieved August 23, 2013.
- ^ Gorman, Siobhan (August 23, 2013). "NSA Officers Sometimes Spy on Love Interests". Retrieved August 23, 2013.
- ^ "Drug Agents Use Vast Phone Trove, Eclipsing N.S.A.'s". August 1, 2013,. Retrieved August 2, 2013.
{{cite news}}: Check date values in:|date=(help); Cite uses deprecated parameter|authors=(help)CS1 maint: extra punctuation (link) - ^ "Synopsis of the Hemisphere Project". September 1, 2013. Retrieved September 2, 2013.
- ^ Andersson, Aron (September 6, 2013). "Video: Här pekar Duncan Campbell ut Sverige" (in Swedish). Retrieved September 7, 2013.
- ^ "Uppgifter om Sverige fick inte publiceras" (in Swedish). September 6, 2013. Retrieved September 7, 2013.
{{cite news}}: Cite uses deprecated parameter|authors=(help) - ^ Staff (September 6, 2013). "Sweden sits on pipeline of intelligence 'gold'". Retrieved September 7, 2013.
- ^ Staff (September 8, 2013). "Datenbank PX: CIA und deutsche Dienste betrieben jahrelang Geheimprojekt" (in German). Retrieved September 8, 2013.
- ^ Greenberg, Andy (September 17, 2013). "Amid NSA Scandal, ACLU Report Turns Spotlight Back To FBI's 'Unchecked Abuse Of Authority'". Retrieved September 17, 2013.
- ^ "Unleashed and Unaccountable: The FBI's Unchecked Abuse of Authority". September 17, 2013. Retrieved September 17, 2013.
- ^ Cushing, Tim (September 18, 2013). "NSA Apparently Purchasing Software Exploits From French Security Firm". Retrieved September 18, 2013.
- ^ "Obama: "Nobody is listening to your telephone calls"". CBS News. Retrieved July 9, 2013.
- ^ "Obama To Leno: 'There Is No Spying On Americans'". NPR. Retrieved August 14, 2013.
- ^ Kessler, Glenn. "James Clapper's 'least untruthful' statement to the Senate". The Washington Post. Retrieved August 13, 2013.
- ^ James Clapper interviewed by Andrea Mitchell of NBC News, June 9 2013. Retrieved September 19, 2013.
- ^ a b "DNI Clapper Letter on Misunderstandings Arising from his March 12th Appearance Before the Senate Select Committee on Intelligence". Director of National Intelligence. Archived from the original (PDF) on December 16, 2013. Retrieved July 9, 2013.
- ^ Turner, Shawn (July 31, 2013). "DNI Clapper Declassifies and Releases Telephone Metadata Collection Documents". Director of Public Affairs Office of the Director of National Intelligence. Retrieved August 17, 2013.
- ^ Assistant Attorney General Roland Weich (December 14, 2009). "Cover Letter and 2009 Report on the National Security Agency's Bulk Collection Program for USA PATRIOT Act Reauthorization" (PDF). U.S. Department of Justice Office of Legal Affairs. Retrieved August 17, 2013.
- ^ Assistant Attorney General Roland Weich (February 2, 2011). "Cover Letters and 2011 Report on the National Security Agency's Bulk Collection Program for USA PATRIOT Act Reauthorization" (PDF). U.S. Department of Justice Office of Legal Affairs. Retrieved August 17, 2013.
- ^ Vinson, Roger (April 25, 2013). "United States Foreign Intelligence Surveilllance Court Docket-Nr: BR 13–80 Primary Order for Business Records Collection Under Section 215 of the USA PATRIOT Act" (PDF). United States Foreign Intelligence Surveillance Court. Office of Director of National Intelligence. Retrieved August 17, 2013.
- ^ Paul Lewis and Spencer Ackerman (August 9, 2013). "Obama touts NSA surveillance reforms to quell growing unease over program". The Guardian. Retrieved August 12, 2013.
- ^ Mark Mazzetti and Scott Shane (August 9, 2013). "Threats Test Obama's Balancing Act on Surveillance". The New York Times. Retrieved August 12, 2013.
- ^ a b c d e "Barack Obama pledges greater surveillance transparency". BBC News US & CANDA. August 9, 2013. Retrieved August 12, 2013.
- ^ "Obama pledges spy programme transparency". Al Jazeera. August 10, 2013. Retrieved August 12, 2013.
- ^ Chelsea J. Carter and Jessica Yellin (August 10, 2013). "Obama: Snowden can 'make his case' in court; no Olympics boycott". CNN. Retrieved August 12, 2013.
- ^ "White House surveillance reform plan – Administration White Paper: 'Bulk Collection of Telephony Metadata under Section 215 of the USA Patriot Act'". The Washington Post. August 9, 2013. Retrieved August 14, 2013.
- ^ "Obama administration asserts broad surveillance powers". The Washington Post. August 10, 2013. Retrieved August 14, 2013.
- ^ Priest, Dana (August 9, 2013). "Piercing the confusion around NSA's phone surveillance program". The Washington Post. Retrieved August 14, 2013.
- ^ a b Ribeiro, James (August 13, 2013). "Intelligence chief Clapper to set up US surveillance review group". PC World. Retrieved August 13, 2013.
- ^ a b Scott Wilson and Zachary A. Goldfarb (August 9, 2013). "Obama announces proposals to reform NSA surveillance". The Washington Post. Retrieved August 12, 2013.
- ^ Serwer, Adam (August 12, 2013). "Intel chief misled Congress on NSA spying. Now he's leading program's review". MSNBC. Retrieved August 13, 2013.
- ^ Masnick, Mike (August 12, 2013). "Confessed Liar To Congress, James Clapper, Gets To Set Up The 'Independent' Review Over NSA Surveillance". Techdirt. Retrieved August 13, 2013.
- ^ Mullin, Joe (August 13, 2013). "Obama's "reform" panel to be led by Clapper, who denied spying to Congress". Ars technica. Retrieved August 13, 2013.
- ^ Peter Wallsten (August 11, 2013). "Lawmakers say obstacles limited oversight of NSA's telephone surveillance program". The Washington Post. Retrieved August 25, 2013.
- ^ Johnson, Luke. "James Clapper, Director of National Intelligence Who Misled Congress, To Establish Surveillance Review Group". Huffington Post. Retrieved August 13, 2013.
- ^ Ackerman, Spencer (September 12, 2013). "Obama's NSA surveillance review panel did not discuss changes, attendees say - Pair say meeting was dominated by tech firms' interests and session did not broach the topic of changes to data collectio". The Guardian. Retrieved October 2, 2013.
- ^ "US: Increase Transparency on Surveillance". Human Rights Watch. Retrieved August 20, 2013.
- ^ "UK: Detention of Guardian journalist's partner at Heathrow unlawful and unwarranted". Amnesty International. Retrieved August 20, 2013.
- ^ "Forcing The Guardian to destroy materials is a direct attack on press freedom". Index on Censorship. Retrieved August 20, 2013.
- ^ "UK: "National security concerns must never justify intimidating journalists into silence," warn UN experts". Office of the United Nations High Commissioner for Human Rights. Retrieved September 4, 2013.
- ^ Matt Sledge. "NSA 'Chilling' Effect Feared By Writers". The Huffington Post. Retrieved November 14, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "PEN American Center Report Shows Impact of NSA Surveillance on American Writers". PEN American Center. Retrieved November 14, 2013.
- ^ Halliday, Josh. "MoD serves news outlets with D notice over surveillance leaks". The Guardian. Retrieved June 27, 2013.
- ^ "The Guardian Blocked by the Army After NSA Stories". Huffington Post. Retrieved August 20, 2013.
- ^ a b "The security threat posed by Snowden". The Financial Times. October 9, 2013.
- ^ "David Miranda Heathrow detention: No 10 'kept abreast of operation'". BBC News. August 20, 2013.
- ^ Boadle, Anthony (August 6, 2013). "Glenn Greenwald: Snowden Gave Me 15–20,000 Classified Documents". Huffington Post. Retrieved August 9, 2013.
- ^ Greenwald, Glenn (August 19, 2013). "Glenn Greenwald: detaining my partner was a failed attempt at intimidation". The Guardian. London.
- ^ "White House knew Glenn Greenwald's partner David Miranda would be detained". CNN. Retrieved August 20, 2013.
- ^ a b "Guardian says Britain made it destroy Snowden material". Reuters. Retrieved August 20, 2013.
- ^ David Miranda's detention had no basis in law, says former lord chancellor | World news. The Guardian. (August 21, 2013).
- ^ a b "US given 'heads up' on David Miranda detention". BBC News. August 19, 2013.
- ^ Rusbridger, Alan (August 19, 2013). "David Miranda, schedule 7 and the danger that all reporters now face". The Guardian. Retrieved August 21, 2013.
- ^ "NSA statements to The Post". The Washington Post. Retrieved August 20, 2013.
- ^ Lloyd Grove. "At the Obama White House: Transparency Transhmarency". The Daily Beast. Retrieved September 23, 2013.
- ^ a b "Latin American nations voice concerns to Ban over rerouting of Bolivian leader's plane". United Nations. Retrieved August 20, 2013.
- ^ Ehrenfreund, Max (July 25, 2013). "House proposal to curtail NSA in response to Edward Snowden's leaks fails narrowly". The Washington Post. Retrieved July 29, 2013.
- ^ Abby Ohlheiser and Philip Bump (July 24, 2013). "The Amash Amendment Fails, Barely". The Atlantic Wire. Retrieved July 29, 2013.
- ^ Kravets, David (July 26, 2013). "Lawmakers Who Upheld NSA Phone Spying Received Double the Defense Industry Cash". Retrieved August 3, 2013.
- ^ Serwer, Adam (September 25, 2013). "New calls for surveillance reform after Snowden". MSNBC. Retrieved October 18, 2013.
- ^ Zengerle, Patricia (September 25, 2013). "U.S. lawmakers seek to end bulk NSA telephone records collection". Reuters. Retrieved October 18, 2013.
- ^ Paul Lewis and Dan Roberts (September 25, 2013). "NSA reform bill to trim back US surveillance unveiled in Congress". The Guardian. Washington. Retrieved October 18, 2013.
- ^ Roberts, Dan (October 10, 2013). "The USA Freedom Act: a look at the key points of the draft bill". The Guardian. Retrieved November 1, 2013.
- ^ Risen, Tom (October 29, 2013). "Freedom Act to End NSA Data Collection Introduced". US News. Retrieved November 1, 2013.
- ^ Sensenbrenner, Congressman Jim. "The USA FREEDOM Act". http://sensenbrenner.house.gov/. Retrieved November 1, 2013.
{{cite web}}: External link in|publisher= - ^ Nakashima, Ellen (October 29, 2013). "NSA bills set up a choice in Congress: End bulk collection of phone records or endorse it". The Washington Post. Retrieved November 1, 2013.
- ^ Spying row: Indonesian president Susilo Bambang Yudhoyono accuses Tony Abbott of taking claims too lightly - Yahoo!7
- ^ "Brazil Reacts With Fury To NSA Spying; Mexico Orders Probe". International Business Times. Retrieved September 16, 2013.
{{cite web}}: Unknown parameter|deadurl=ignored (|url-status=suggested) (help) - ^ a b c "Exclusive: Brazil's Rousseff wants U.S. apology for NSA spying". Reuters. Retrieved September 16, 2013.
{{cite web}}: Unknown parameter|deadurl=ignored (|url-status=suggested) (help) - ^ "China has 'mountains of data' about U.S. cyber attacks: official". Reuters. June 5, 2013. Retrieved October 24, 2013.
- ^ "China asks U.S. to explain Internet surveillance". Reuters. Retrieved October 24, 2013.
- ^ "France summons U.S. ambassador over spying report". Reuters. Retrieved October 24, 2013.
- ^ Michael Mainville. "France warns US spying claims threaten trade talks". AFP. Retrieved October 24, 2013.
- ^ "NSA-Spähskandal: So funktionieren die Abhöranlagen in US-Botschaften". Spiegel Online. October 28, 2013. Retrieved October 30, 2013.
- ^ "German Foreign Ministry Summons US Ambassador Over NSA Spying Claims". The Wall Street Journal'. July 1, 2013.
Seeking clarification on the matter, the foreign ministry has called the U.S. ambassador to Germany, Philip Murphy, for a meeting later Monday, a spokesman for the ministry said.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "German foreign minister summons US ambassador over Merkel spying allegations". Deutsche Welle. Retrieved October 24, 2013.
- ^ "NSA spying allegations: Are US allies really shocked?". BBC. October 26, 2013. Retrieved October 26, 2013.
- ^ "Germany ends spy pact with US and UK after Snowden". BBC. August 2, 2013.
- ^ German Helicopter Searched For NSA Listening Post In Frankfurt SPIEGEL ONLINE.
- ^ "Indonesia Summons Australian Ambassador Over US Spying Allegations". Voice of America. Retrieved November 4, 2013.
- ^ George Roberts. "Indonesia recalls ambassador after leaked documents reveal Australia spied on president Susilo Bambang Yudhoyono". Australian Broadcasting Corporation. Retrieved 18 November 2013.
- ^ "Italy Presses Kerry Over US Surveillance". Voice of America. Retrieved October 24, 2013.
- ^ "Letta quizzes Kerry on US spy claims". Gazzetta del Sud. Retrieved October 24, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "Malaysia summons US, Australia missions over spy row". Channel NewsAsia. Retrieved November 4, 2013.
- ^ "Mexico foreign minister meets US envoy over spy claims". AFP. Retrieved October 26, 2013.
- ^ "Spanish PM summons U. S. ambassador over NSA spying". Agenzia Giornalistica Italia. Retrieved October 27, 2013.
- ^ "NSA surveillance: Spain demands US explain 'monitoring'". bbc.co.uk. October 28, 2013. Retrieved October 28, 2013.
- ^ "European Union threatens to stop sharing data with United States over spying reports". Daily News. Retrieved July 8, 2013.
- ^ "Rules Shielding Online Data From N.S.A. and Other Prying Eyes Advance in Europe", James Kanter and Mike Scott, New York Times, October 21, 2013. Retrieved October 22, 2013.
- ^ "EU-US spying row stokes concern over anti-terror campaign". EU Business. October 26, 2013. Retrieved October 26, 2013.
- ^ "EU says distrust of US on spying may harm terror fight". BBC. October 25, 2013. Retrieved October 26, 2013.
- ^ Roulo, Claudette. "Leaks Damage National Security, NSA Director Says". American Forces Press Service. Archived from the original on December 16, 2013. Retrieved July 8, 2013. (Archive)
- ^ Corera, Gordon (October 4, 2013). "Edward Snowden revelations: Can we trust the spying state?". BBC.
- ^ Edward Snowden: Russia, China Did Not Get Any Documents From Me
- ^ Whitehead, Tom (October 9, 2013). "GCHQ leaks have 'gifted' terrorists ability to attack 'at will', warns spy chief". Daily Telegraph.
- ^ a b Gardner, Timothy; Hosenball, Mark (June 9, 2013). "Spy agency seeks criminal probe into leaks". Reuters. Retrieved June 9, 2013.
- ^ Blake, Aaron (June 9, 2013). "Clapper: Leaks are 'literally gut-wrenching,' leaker being sought". The Washington Post. Retrieved August 8, 2013.
- ^ Finn, Peter; Horwitz, Sari (June 21, 2013). "U.S. charges Snowden with espionage". The Washington Post. Retrieved June 21, 2013.
- ^ a b Ackerman, Spencer; Roberts, Dan (June 28, 2013). "US army blocks access to Guardian website to preserve 'network hygiene'". The Guardian. London. Retrieved June 29, 2013.
- ^ Ackerman, Spencer (July 1, 2013). "US military blocks entire Guardian website for troops stationed abroad". The Guardian.
- ^ Raddatz, Martha (August 4, 2013). "Transcript for Joint Chiefs Chairman Gen. Martin Dempsey on 'This Week'". ABC News 'This Week'. Retrieved August 14, 2013.
- ^ "Obama downplays Snowden case, says US not 'scrambling jets' to get 'hacker'". Fox News. June 27, 2013.
- ^ Pecquet, Julian (June 27, 2013). "US won't 'scramble jets' to capture 'hacker' Snowden, Obama says". The Hill.
- ^ a b Wolf, Z. Byron (August 13, 2013). "Fact-checking Obama's claims about Snowden". CNN.
- ^ MacAskill, Ewen (August 13, 2013). "White House insists James Clapper will not lead NSA surveillance review". The Guardian.
- ^ Farivar, Cyrus (August 23, 2013). "Obama's 'outside experts' surveillance review panel has deep ties to gov't". Ars Technica.
- ^ Waterman, Shaun (September 12, 2013). "Congress will rein in NSA's domestic snooping, predicts top U.S. intel official". The Washington Times. Retrieved September 16, 2013.
- ^ Dilanian, Ken (September 12, 2013). "Clapper: Snowden case brings healthy debate; more disclosures to come". The Los Angeles Times. Retrieved September 15, 2013.
- ^ Reeve, Elspeth (June 10, 2013). "Washington turns on the NSA blinders to target weird 'IT guy' leaker instead". The Atlantic Wire.
- ^ LoGiurato, Brett (June 11, 2013). "John Boehner: Edward Snowden Is A 'Traitor'". San Francisco Chronicle. Retrieved June 11, 2013.
- ^ a b Herb, Jeremy; Sink, Justin (June 10, 2013). "Sen. Feinstein calls Snowden's NSA leaks an 'act of treason'". thehill.com.
- ^ Nelson, Bill (June 11, 2013). "This man is a traitor". Daily News. New York.
- ^ "Edward Snowden: Ex-CIA leaker drops out of sight, faces legal battle". The Chicago Tribune. Reuters. June 10, 2013. Retrieved June 12, 2013.
- ^ Blake, Aaron (June 11, 2013). "DNC chair Debbie Wasserman Schultz: Snowden is a coward". The Washington Post. Retrieved June 13, 2013.
- ^ Dumain, Emma; Lesniewski, Niels (June 10, 2013). "Snowden Has a Few Defenders on the Hill". Roll Call. Retrieved June 11, 2013.
- ^ Morgenstern, Madeleine (June 11, 2013). "Ted Cruz Reserving Judgement on Whether NSA Leaker Is a 'Patriot' or a 'Traitor'". The Blaze. Retrieved June 11, 2013.
- ^ Sink, Justin (June 11, 2013). "Rand Paul 'reserving judgment' on NSA leaker". The Hill.
- ^ Sullivan, Sean (June 23, 2013). "Rand Paul: Snowden will face problems if he 'cozies up' to Russia, China". The Washington Post.
- ^ "Rand Paul: Edward Snowden 'civil disobedient' – Tal Kopan –". Politico.com. June 18, 2013.
- ^ "John Lewis compares Edward Snowden, Gandhi – James Arkin –". Politico.com. August 8, 2013.
- ^ "This man is a traitor". senate.gov. Retrieved September 18, 2013.
- ^ "John Boehner: Edward Snowden Is A 'Traitor'". The Huffington Post. Retrieved September 18, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ S. 1372 at Congress.gov. S. 1372 at GovTrack. S. 1372 at OpenCongress.
- ^ Zengerle, Patricia (July 25, 2013). "U.S. lawmakers want sanctions on any country taking in Snowden". Reuters.
- ^ "U.S. Senate advances law pressuring Russia not to give Snowden asylum". Xinhua. July 26, 2013.
- ^ "FY14 Full Committee Markup of State-Foreign Operations, and Financial Services General Government Bills" (Podcast). United States Senate Committee on Appropriations. July 25, 2013. Event occurs at 1:10:08.
- ^ Max Ehrenfreund. "House proposal to curtail NSA in response to Edward Snowden's leaks fails narrowly". The Washington Post.
- ^ "The Amash Amendment Fails, Barely – Abby Ohlheiser and Philip Bump". The Atlantic Wire. July 24, 2013.
- ^ "Amash: Snowden a whistle-blower, 'told us what we need to know'". Fox News. August 4, 2013. Retrieved October 6, 2013.
- ^ Raddatz, Martha (August 4, 2013). "'This Week' Transcript: Gen. Martin Dempsey, Reps. Ruppersberger and King, and Glenn Greenwald". ABC News 'This Week'. Retrieved August 14, 2013.
- ^ "McCain: Young Americans admire Snowden, see him as 'some kind of Jason Bourne'". The Washington Times. Retrieved August 11, 2013.
- ^ Johnson, Luke. "Edward Snowden Receives Support From Former GOP Sen. Gordon Humphrey". Huffington Post. Retrieved August 11, 2013.
- ^ Greenwald, Glenn. "Email exchange between Edward Snowden and former GOP Senator Gordon Humphrey". The Guardian. Retrieved August 11, 2013.
- ^ Gold, Hadas. "Former Sen. Gordon Humphrey emails with Edward Snowden". Politico. Retrieved July 17, 2013.
- ^ "Rep. McClintock Says the US Should Grant Snowden Amnesty – Hit & Run". Reason. July 24, 2013.
- ^ Newport, Frank (June 12, 2013). "Americans Disapprove of Government Surveillance Programs". Gallup.
- ^ "Public Split over Impact of NSA Leak, But Most Want Snowden Prosecuted". Pew Research Center. June 17, 2013.
{{cite journal}}: Cite journal requires|journal=(help) - ^ Page, Susan (June 18, 2013). "Poll: Snowden should be prosecuted for NSA leaks". USA Today. Washington DC.
- ^ "Post-ABC poll: NSA surveillance and Edward Snowden". The Washington Post. June 19, 2013.
- ^ Emily Swanson (July 5, 2013). "Edward Snowden Poll Finds More Americans Now Think He Did The Wrong Thing". Huffington Post. Retrieved July 9, 2013. See more polls reported in early July, see here [1].
- ^ Rebecca Ballhaus (July 24, 2013) WSJ/NBC Poll: Most Americans View Snowden Negatively The Wall Street Journal
- ^ a b Salant, Jonathan D. (July 10, 2013). "Snowden Seen as Whistle-Blower by Majority in New Poll". Bloomberg News. Retrieved July 10, 2013.
- ^ Nelson, Steven (August 1, 2013). "As Edward Snowden receives asylum in Russia, poll shows Americans sympathetic to NSA 'whistle-blower'". US News & World Report.
- ^ Heather, Kelly. "Protests against the NSA spring up across U.S." CNN. Retrieved August 13, 2013.
- ^ "Thousands fill German streets to protest Berlin's NSA spying involvement". Russia: RT. Retrieved August 13, 2013.
- ^ Greenwald, Glenn (June 22, 2013). "On the Espionage Act charges against Edward Snowden". The Guardian Security and Liberty blog. London. Archived from the original on June 23, 2013. Retrieved June 23, 2013.
{{cite news}}: Unknown parameter|deadurl=ignored (|url-status=suggested) (help) - ^ Guariglia, Matthew (June 10, 2013). "Edward Snowden: Traitor or Hero?". heavy.com. Retrieved June 11, 2013.
- ^ Cassidy, John (June 10, 2013). "Why Edward Snowden Is A Hero". The New Yorker.
- ^ Rushkoff, Douglas (June 10, 2013). "Edward Snowden is a hero". CNN. Retrieved June 16, 2013.
- ^ Davidson, Amy (June 9, 2013). "Edward Snowden, The N.S.A. Leaker, Comes Forward". The New Yorker.
- ^ Harvey, Fiona (June 19, 2013). "NSA surveillance is an attack on American citizens, says Noam Chomsky". The Guardian. London. Retrieved July 4, 2013.
- ^ "New Yorkers Declare 'I Stand With Edward Snowden': Dozens Rally & Draw Massive Media Attention for NSA Whistleblower (updated)". the sparrow project. June 10, 2013. Retrieved June 11, 2013.
- ^ a b Gold, Hadas (June 10, 2013). "Glenn Beck, Michael Moore call Edward Snowden a hero". Politico. Retrieved June 11, 2013.
- ^ "Cornel West Calls Edward Snowden the 'John Brown' of National Security". colorlines. June 28, 2013. Retrieved July 4, 2013.
- ^ Budowsky, Brent (June 7, 2013). "Matt Drudge, Bernie Sanders and Ron Paul versus Barack Obama, George W. Bush and Big Brother". The Hill. Washington DC. Retrieved June 11, 2013.
- ^ "Arrest Congressman Peter King, Not NSA Whistleblower". Infowars. June 10, 2013. Retrieved June 11, 2013.
- ^ "Napolitano: NSA Leaker Is an "American Hero"". Fox News Channel. June 10, 2013. Retrieved July 4, 2013.
- ^ "Oliver Stone calls National Security Agency secret-leaker Edward Snowden 'a hero'". July 4, 2013.
- ^ Kirell, Andrew (June 11, 2013). "Michael Savage Rants Against Fox News' 'Empty Skirts' & 'Lipstick With Legs' For Condemning NSA Leaker". Mediaite. Retrieved June 12, 2013.
- ^ Walt, Stephen (July 8, 2013). "Snowden deserves an immediate presidential pardon". Financial Times. Retrieved July 8, 2013.
- ^ Reeve, Elspeth (June 10, 2013). "These Pundits Have Decided Snowden Deserves to Go to Jail". The Atlantic Wire. Washington DC. Retrieved June 12, 2013.
- ^ a b Toobin, Jeffrey (June 10, 2013). "Edward Snowden is no hero". The New Yorker.
- ^ "Edward Snowden is a 'traitor' and possible spy for China – Dick Cheney". The Guardian. Retrieved September 18, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Branigin, William (July 17, 2013). "Lawmakers of both parties voice doubts about NSA surveillance programs". The Washington Post.
- ^ Former CIA, NSA chief Michael Hayden: Open spy programs to reassure U.S. public, The Washington Times, June 30, 2013. Retrieved Jul 9, 2013.
- ^ Former CIA, NSA director sounds off on PRISM, spying tools, Network World, July 1, 2013. Retrieved Jul 9, 2013.
- ^ Peterson, Andrea. "Former NSA chief: 'Morally arrogant' Snowden will probably become an alcoholic". The Washington Post. Retrieved September 18, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Schindler, John R. (June 27, 2013). "Snowden in the U.S.-Russian 'SpyWar'". National Affairs.
- ^ Ross, Brian (June 26, 2013). "Edward Snowden Steps Into Secret U.S.-Russia Spy Scuffle". ABC News
- ^ Ewing, Philip (June 25, 2013). "What Russian intel might ask Edward Snowden". Politico.
- ^ Simon Schuster (July 10, 2013). Snowden in Moscow: What Russian Authorities Might Be Doing With the NSA Whistle-Blower Time
- ^ Snowden: I never gave any information to Chinese or Russian governments, Glenn Greenwald, July 10, 2013
- ^ Watkins, Tom (June 30, 2013). "Father proposes deal for Snowden's voluntary return", CNN
- ^ The Editors (June 24, 2013). "This Is Not About Edward Snowden". Bloomberg News. New York. Retrieved June 25, 2013.
{{cite news}}:|author=has generic name (help) - ^ Greenwald, Glenn (July 3, 2013). "James Clapper, EU play-acting, and political priorities". The Guardian Security and Liberty blog (London). Retrieved July 3, 2013.
- ^ Berenson, Alex (June 25, 2013). "Snowden, Through the Eyes of a Spy Novelist". The New York Times. Retrieved June 26, 2013.
- ^ "NSA leaker petition hits 100,000-signature threshold in under 2 weeks". RT USA. June 18, 2013. Retrieved June 25, 2013.
- ^ White House Remains Silent on 'Pardon Edward Snowden' Petition - Washington Whispers (usnews.com)
- ^ Three Months After It Cleared The 100K Signature Threshold, 'Pardon Snowden' Petition Still Unanswered | Techdirt
- ^ a b c d Poulsen, Kevin (August 8, 2013). "Edward Snowden's email provider shuts down amid secret court battle". Wired.
- ^ Associated Press (August 8, 2013). "Texas-based secure email service linked to NSA leaker Edward Snowden abruptly shuts down". The Washington Post.
- ^ Masnick, Mike (August 8, 2013). "Edward Snowden's email provider, Lavabit, shuts down to fight gov't intrusion". Techdirt.
- ^ Hill, Kashmir (August 8, 2013). "Email company reportedly used by Edward Snowden shuts down rather than hand over data to the Feds". Forbes.
- ^ Schneier, Bruce (August 22, 2013). "The real, terrifying reason why British authorities detained David Miranda". The Atlantic.
- ^ "Lavabit privacy row: second email service closes 'to prevent spying' | Technology". The Guardian.
- ^ Glenn Greenwald (August 9, 2013). "Email service used by Snowden shuts itself down, warns against using US-based companies". The Guardian.
- ^ Pop, Valentina (July 8, 2013). "Germany defends intelligence co-operation with US". EUobserver. Retrieved July 9, 2013.
- ^ Trittin, Jürgen (July 2, 2013). "Edward Snowden deserves shelter in Germany". The Guardian. United Kingdom. Retrieved July 13, 2013.
- ^ Oltermann, Philip (November 3, 2013). "Germany 'should offer Edward Snowden asylum after NSA revelations' ". theguardian.com. Retrieved November 3, 2013.
- ^ Elgot, Jessica; Freeman, Sunny (October 30, 2013). "Edward Snowden A 'Hero' In UK, But Americans Are More Divided". The Huffington Post UK. Retrieved October 30, 2013.
- ^ http://www.c-span.org/Events/Group-Holds-Rally-Against-Mass-Surveillance/10737442319-1/
- ^ Bart Jansen and Carolyn Pesce. "Anti-NSA rally attracts thousands to march in Washington". USA Today. Retrieved October 27, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Bart Jansen and Carolyn Pesce, USA TODAY (October 26, 2013). "Anti-NSA rally attracts thousands to march in Washington". Usatoday.com. Retrieved November 1, 2013.
- ^ Thousands gather in Washington for anti-NSA 'Stop Watching Us' rally | World news | theguardian.com
- ^ "Stop Watching Us in Europe: Germans protest in Cologne against surveillance - News - World - The Voice of Russia: News, Breaking news, Politics, Economics, Business, Russia, International current events, Expert opinion, podcasts, Video". The Voice of Russia. Retrieved November 1, 2013.
- ^ "Stop Watching Us - A Coalition Against Mass Surveillance | Stop Watching Us". Optin.stopwatching.us. June 14, 2013. Retrieved November 1, 2013.
- ^ "'Time to reform surveillance state': Stop Watching Us rally challenges NSA spying — RT USA". Rt.com. Retrieved November 1, 2013.
- ^ "2013 Sakharov Prize for Freedom of Thought - seven nominations". September 16, 2013. Retrieved September 18, 2013.
Edward Snowden - nominated by the Greens/EFA group and GUE/NGL group
- ^ "Pakistan's Malala, Snowden Nominated for E.U. Prize". September 16, 2013. Retrieved September 18, 2013.
- ^ 'Key Partners': The Secret Link Between Germany and the NSA July 22, 2013 Spiegel Online
- ^ "Data snooping: law abiding citizens have 'nothing to fear', says Hague – video". The Guardian (London). June 9, 2013.
- ^ "NSA Prism programme: William Hague makes statement on GCHQ – video". The Guardian (London). June 10, 2013.
- ^ Travis, Alan; Connolly, Kate; Watt, Nicholas (June 26, 2013). "GCHQ surveillance: Germany blasts UK over mass monitoring". The Guardian. London.
{{cite news}}: CS1 maint: multiple names: authors list (link) - ^ Staines, Paul (June 8, 2013). "D-Notice, June 7, 2013". Guido Fawkes blog.
- ^ Watt, Nicholas (October 28, 2013). "David Cameron makes veiled threat to media over NSA and GCHQ leaks". theguardian.com. Retrieved November 3, 2013.
- ^ "CPJ alarmed by Cameron's threat against UK press". cpj.org. October 29, 2013. Retrieved November 3, 2013.
- ^ Taylor, Matthew; Hopkins, Nick (November 3, 2013). "UK government reaction to NSA leaks eroding freedom, rights groups warn". theguardian.com. Retrieved November 3, 2013.
- ^ Jouleva, Gergana; et al. "Human rights groups' open letter to David Cameron on surveillance". theguardian.com. Retrieved November 3, 2013.
{{cite news}}: Explicit use of et al. in:|first=(help) - ^ a b "UN rights chief urges protection for individuals revealing human rights violations". United Nations. Retrieved August 4, 2013.
- ^ Amnesty International meets US whistleblower Edward Snowden July 12, 2013
- ^ "USA must not hunt down whistleblower Edward Snowden". Amnesty International. Retrieved June 25, 2013.
- ^ USA must not persecute whistleblower Edward Snowden July 2, 2013 Amnesty
- ^ "US: Protect National Security Whistleblowers". Human Rights Watch. Retrieved June 25, 2013.
- ^ Countries Should Consider Snowden’s Asylum Claim Fairly". Human Rights Watch, July 2013
- ^ "US needs to protect whistleblowers and journalists". Index on Censorship. Retrieved August 4, 2013.
- ^ Heise Online-Autoren Detlef Borchers, anw (July 23, 2013). "Whistleblower-Preis für Edward Snowden". Heise Online. Archived from the original on July 25, 2013. Retrieved July 25, 2013.
- ^ Sven Lüders (July 24, 2013). "Fritz-Bauer-Preis an Edward Snowden". Humanistischer Pressedienst. Archived from the original on July 25, 2013. Retrieved July 25, 2013.
- ^ But, Joshua (June 16, 2013). "Hongkongers don't want Snowden handed over to the US, according to poll". South China Morning Post. Hong Kong. Retrieved June 17, 2013.
- ^ "HK, US govt lawyers 'not working together' on Snowden, say sources as CY breaks silence". South China Morning Post. Hong Kong. June 16, 2013.
- ^ Fraser, Niall (June 13, 2013). "H.K. lawmakers petition Obama for leniency against whistleblower". Kyodo News International. Retrieved June 15, 2013.
- ^ Ma, Mary (June 20, 2013). "Ip in security minister's shoes". The Standard. Hong Kong.
However, surrounding the Snowden case is something never before seen in local politics. Not only are the pan-democrat and pro-establishment camps singing off the same song sheet, the pan-democrats and mainland propagandists are humming a similar tune.
- ^ Lau, Stuart (June 24, 2013). "Hong Kong's political foes made allies amid Edward Snowden storm". South China Morning Post. Hong Kong. Retrieved June 24, 2013.
Snowden's arrival in the city gave Hong Kong a rare place in the global geopolitical spotlight and ushered in near-unprecedented political solidarity as pan-democrats and Beijing loyalists lined up to take a shot at an unlikely target: the United States.
- ^ a b Zuo, Mandy (June 20, 2013). "Beijing wants Hong Kong to handle Snowden on its own, party newspapers suggest". South China Morning Post. Hong Kong. Retrieved June 20, 2013. In print as "Articles highlight possible Beijing role".
{{cite news}}: CS1 maint: postscript (link) - ^ Lai Ying-kit (June 24, 2013). "Edward Snowden's depature seen as a relief: Chinese-language newspapers". South China Morning Post. Hong Kong. Retrieved June 24, 2013.
- ^ "Beijing made final decision, say analysts". South China Morning Post. Hong Kong. June 25, 2013. p. 2.
- ^ Kaiman, Jonathan (June 25, 2013). "China's state newspaper praises Edward Snowden for 'tearing off Washington's sanctimonious mask'". The Guardian. London. Retrieved June 25, 2013.
- ^ "Ecuador warned: Asylum for Edward Snowden would jeopardize millions in trade". Michelle Malkin. June 27, 2013.
- ^ "Ecuador offers U.S. rights aid, waives trade benefits". Reuters. June 27, 2013.
- ^ "Ecuador waives US trade rights after threats made over Snowden case". South China Morning Post. Hong Kong. June 28, 2013.
- ^ "Ecuador president blasts coverage of Snowden case". Newsday. New York. Associated Press. June 26, 2013. Archived from the original on June 29, 2013. Retrieved June 28, 2013.
- ^ Snowden's fate up in the air after Nicaragua, Venezuela offer asylum, CTV Television Network, July 5, 2013. Retrieved July 9, 2013.
- ^ Sotero, Paulo (September 17, 2013). "Mission impossible in Moscow". O Estado de S. Paulo. Retrieved September 18, 2013.
- ^ Leahy, Joe (September 18, 2013). "Brazil's Petrobras to invest heavily in data security". Financial Times. São Paulo. Retrieved September 18, 2013. (registration required)
- ^ a b Pilkington, Ed. "Edward Snowden's digital 'misuse' has created problems, says Ban Ki-moon." The Guardian. July 3, 2013. Retrieved July 3, 2013.
- ^ G20 summits: Russia and Turkey react with fury to spying revelations, The Guardian, June 17, 2013. Retrieved Jul 2013.
- ^ O'Malley, Nick (June 10, 2013). "NSA leaker reveals himself after fleeing US". The Sydney Morning Herald. Retrieved June 10, 2013.
- ^ Ellsberg, Daniel (June 10, 2013). "Edward Snowden: saving us from the United Stasi of America". The Guardian. Retrieved June 10, 2013.
- ^ Noor, Jaisal (June 11, 2013). "Former CIA Analyst: Snowden Did The Right Thing". The Real News Network.
- ^ a b Eisler, Peter; Page, Susan (June 16, 2013). "3 NSA veterans speak out on whistle-blower: We told you so." USA Today (Washington DC). Retrieved June 19, 2013.
- ^ Snowden saw what I saw: surveillance criminally subverting the constitution The Guardian. Retrieved July 10, 2013
- ^ Addley, Esther (June 10, 2013). "Julian Assange praises Edward Snowden as a hero". The Guardian. London. Retrieved June 10, 2013.
- ^ Dart, Tom (June 22, 2013). "Support NSA whistleblower Edward Snowden, says Julian Assange". The Guardian (London). Retrieved June 22, 2013.
- ^ David Jackson. "Assange: Obama 'validates' Snowden". USA Today.
- ^ "Assange calls Obama reform plans 'victory of sorts' for Snowden". Reuters. August 10, 2013.
- ^ Blowback from the White House's vindictive war on whistleblowers." Leibowitz, Shamai in The Guardian. July 5, 2013. Retrieved July 5, 2013.
- ^ The Washington Post
- ^ Former National Security Whistleblowers Meet in Moscow and Award Sam Adams Prize to Snowden - Government Accountability Project
- ^ 'US unchained itself from constitution': Whistleblowers on RT after secret Snowden meeting — RT News
- ^ John Hudson. "Exclusive: After Multiple Denials, CIA Admits to Snooping on Noam Chomsky". Foreign Policy. Retrieved September 27, 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Nikhil Kumar. "Memo shows CIA 'did keep file on Noam Chomsky'". The Independent. Retrieved September 27, 2013.
{{cite news}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b c d e f g Aid, Matthew M. "Secret Cold War Documents Reveal NSA Spied on Senators". Foreign Policy. Retrieved September 25, 2013.
...That's according to a recently declassified NSA history, which called the effort "disreputable if not outright illegal." For years the names of the surveillance targets were kept secret. But after a decision by the Interagency Security Classification Appeals Panel, in response to an appeal by the National Security Archive at George Washington University, the NSA has declassified them for the first time. The names of the NSA's targets are eye-popping.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help)
Further reading
- "Global Surveillance. An annotated and categorized "overview of the revelations following the leaks by the whistleblower Edward Snowden. There are also some links to comments and followups". By Oslo University Library.
- "The NSA Files". The Guardian.
- Politico Staff. "NSA leaks cause flood of political problems." Politico. June 13, 2013.
- NSA inspector general report on email and internet data collection under Stellar Wind as provided by The Guardian on June 27, 2013.
- "Putin talks NSA, Syria, Iran, drones in exclusive RT interview (FULL VIDEO)." Russia Today. June 12, 2013.
- Ackerman, Spencer. "NSA warned to rein in surveillance as agency reveals even greater scope." The Guardian. July 17, 2013.
- Ackerman, Spencer. "Slew of court challenges threaten NSA's relationship with tech firms." The Guardian. Wednesday July 17, 2013.
- Ackerman, Spencer and Paul Lewis. "NSA amendment's narrow defeat spurs privacy advocates for surveillance fight." The Guardian. Thursday July 25, 2013.
- Ackerman, Spencer and Dan Roberts. "US embassy closures used to bolster case for NSA surveillance programs." The Guardian. Monday August 5, 2013.
- Two of the 'trips' (numbers 29 and 76) in the 2006 book, 'No Holiday', Cohen, Martin. No Holiday. New York: Disinformation Company Ltd. ISBN 978-1-932857-29-0.
{{cite book}}:|access-date=requires|url=(help) are investigating the NSA and its activities. - Greenwald, Glenn. "Members of Congress denied access to basic information about NSA." The Guardian. Sunday August 4, 2013.
- "Obama’s former adviser ridicules statement that NSA doesn’t spy on Americans." (Archive) Russia Today. August 9, 2013.
- MacAskill, Ewen. "Justice Department fails in bid to delay landmark case on NSA collection." The Guardian. Thursday July 25, 2013.
- Rushe, Dominic. "Microsoft pushes Eric Holder to lift block on public information sharing." The Guardian. Tuesday July 16, 2013.
- Perez, Evan. "Documents shed light on U.S. surveillance programs." (Archive) CNN. August 9, 2013.
- Gellman, Barton. "NSA broke privacy rules thousands of times per year, audit finds." Washington Post. Thursday August 15, 2013.
- Roberts, Dan and Robert Booth. "NSA defenders: embassy closures followed pre-9/11 levels of 'chatter'." The Guardian. Sunday August 4, 2013.
- Greenwald, Glenn. "The crux of the NSA story in one phrase: 'collect it all'." The Guardian. Monday July 15, 2013.
- Sanchez, Julian. "Five things Snowden leaks revealed about NSA’s original warrantless wiretaps." Ars Technica. July 9, 2013.
- Forero, Juan. "Paper reveals NSA ops in Latin America." Washington Post. July 9, 2013.
- Jabour, Bridie. "Telstra signed deal that would have allowed US spying." The Guardian. Friday July 12, 2013.
- Ackerman, Spencer. "White House stays silent on renewal of NSA data collection order." The Guardian. Thursday July 18, 2013.
- Naughton, John. "Edward Snowden's not the story. The fate of the internet is." The Guardian. July 28, 2013.
- Adams, Becket. "MAD MAGAZINE USES ICONIC CHARACTERS TO HIT OBAMA OVER GOV’T SURVEILLANCE." The Blaze. August 8, 2013.
- Howerton, Jason. "HERE IS THE PRO-NSA SURVEILLANCE ARGUMENT." The Blaze. June 10, 2013.
- "Edward Snowden NSA files: secret surveillance and our revelations so far – Leaked National Security Agency documents have led to several hundred Guardian stories on electronic privacy and the state" by the Guardian's James Ball on August 21, 2013
- 2013-07-29 Letter of FISA Court president Reggie B. Walton to the Chairman of the U.S. Senate Judiciary Committee Patrick J. Leahy about certain operations of the FISA Court; among other things the process of accepting, modifying and/or rejecting surveillance measures proposed by the U.S. government, the interaction between the FISA Court and the U.S. government, the appearance of non-governmental parties before the court and the process used by the Court to consider and resolve any instances where the government entities notifies the court of compliance concerns with any of the FISA authorities.
- "The Spy Files". Wikileaks. December 1, 2011. A collection of documents relating to surveillance.
- "The Spy Files". Wikileaks. December 8, 2011. Part 2 of the above.
- "Spy Files 3". Wikileaks. September 4, 2013. Part 3 of the above.
- "Veja os documentos ultrassecretos que comprovam espionagem a Dilma" (in Portuguese). September 2, 2013. Retrieved September 4, 2013. Documents relating to the surveillance against Dilma Roussef and Enrique Peña Nieto
- NSA surveillance: A guide to staying secure - The NSA has huge capabilities – and if it wants in to your computer, it's in. With that in mind, here are five ways to stay safe by The Guardian's Bruce Schneier on September 5, 2013.